The cybercriminal landscape continues to witness a concerning evolution in ransomware tactics, with the emerging LeakNet threat actor demonstrating a sophisticated and stealthy approach to infiltrate corporate networks. Recent analyses reveal LeakNet’s adoption of the "ClickFix" social engineering technique for initial access, coupled with the innovative use of the open-source Deno runtime to execute malicious payloads directly in system memory. This dual strategy significantly enhances their ability to evade detection and minimize forensic footprints, posing an escalating threat to organizations worldwide.
The ClickFix Lure and the Deno Gambit
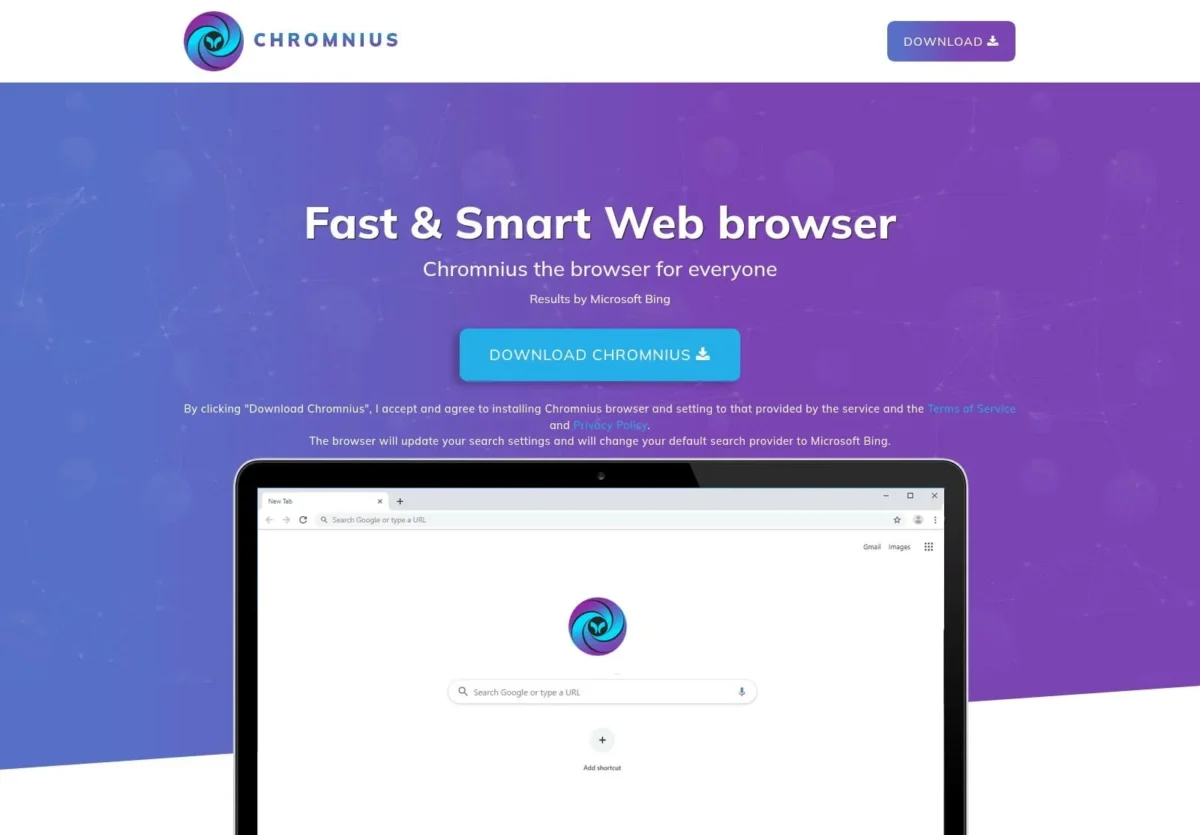
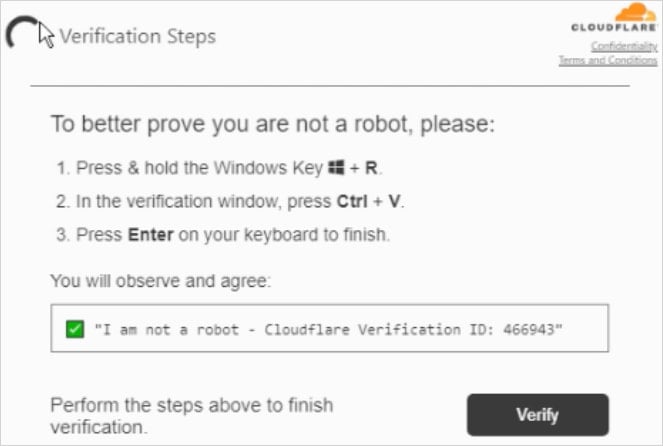
At the heart of LeakNet’s current operational modus operandi lies the exploitation of the ClickFix attack vector. This well-established social engineering method preys on user trust and prompt-driven interactions, often tricking unsuspecting individuals into executing malicious commands disguised as legitimate system prompts or software updates. While not a novel technique, its persistent effectiveness across various threat actors, including notable groups like Termite and Interlock, underscores its value in breaching initial defenses.
LeakNet elevates this by integrating the Deno runtime into their attack chain. Deno, a secure runtime for JavaScript and TypeScript that emphasizes security and developer productivity, is leveraged by LeakNet not for its intended purposes, but as a covert execution engine. The attackers utilize Deno to decode and directly inject malicious code into the system’s memory, bypassing traditional disk-based malware analysis and significantly reducing the chances of detection by signature-based security solutions. This "bring your own runtime" (BYOR) approach, as termed by cybersecurity researchers, is particularly insidious because Deno itself is a legitimate, signed binary. This inherent legitimacy allows it to bypass many security filters and blocklists designed to prevent the execution of unknown or unauthorized executables.
"Rather than deploying a custom malware loader that’s more likely to get flagged," explained a spokesperson for cybersecurity firm ReliaQuest, who first detailed these tactics, "the attackers install the legitimate Deno executable and use it to run malicious code. This process was observed initiated through Visual Basic Script (VBS) and PowerShell scripts, cleverly named Romeo.ps1 and Juliet.vbs in some instances." The choice of these script names adds a layer of obfuscation, potentially leading defenders to dismiss them as benign development or administrative scripts.
LeakNet: A Growing Threat Profile
LeakNet, though a relatively recent entrant into the ransomware arena, has demonstrated a consistent and concerning operational tempo. Active since late 2024, the group has been averaging approximately three victims per month. While this rate might seem moderate compared to some more established ransomware operations, the adoption of these advanced tactics signals a potential for significant expansion. Their evolving toolkit suggests a calculated approach to scaling their operations and increasing their success rate in achieving successful data exfiltration and encryption.

The impact of these new tactics on LeakNet’s operational efficiency is substantial. By executing payloads in memory, they leave behind a significantly reduced digital trail on the compromised system’s storage. This makes forensic investigations more challenging and time-consuming, potentially allowing the attackers more time to complete their objectives before being fully identified and eradicated. The perception of legitimate Deno activity as a "normal developer task" further aids in their stealth, making it harder for security analysts to distinguish malicious actions from benign system operations.
The Attack Chain: From Infiltration to Exfiltration
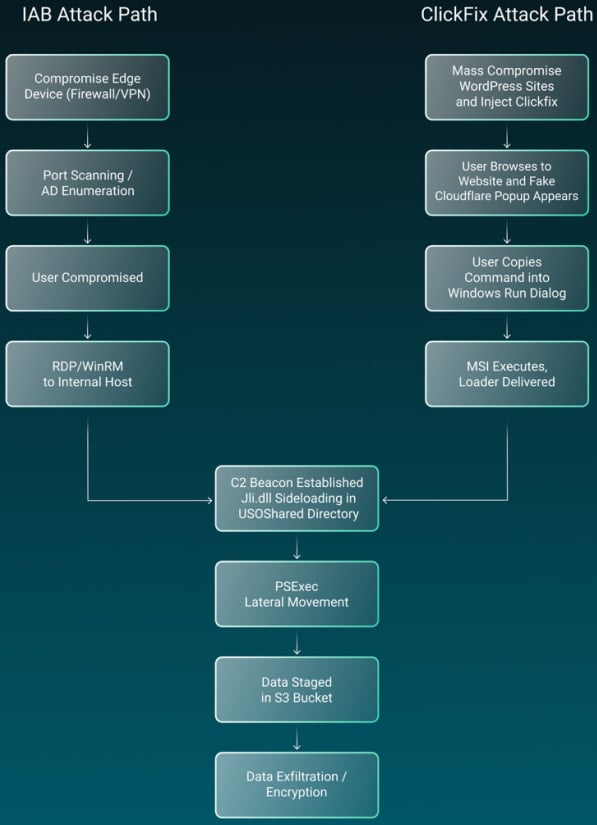
The observed attack chain employed by LeakNet provides a clear, albeit disturbing, roadmap of their intrusion process.
-
Initial Access (ClickFix): The attack commences with a user interaction driven by the ClickFix social engineering lure. This typically involves a convincing prompt that, when acted upon, triggers the execution of initial malicious scripts.
-
Payload Delivery and Execution (Deno Loader): The initial scripts, such as the observed Romeo.ps1 and Juliet.vbs, are designed to download and execute the legitimate Deno runtime. Deno then acts as the loader, decoding and injecting the primary malicious JavaScript payload directly into system memory. This in-memory execution is a critical step in their evasion strategy.
-
Reconnaissance and Command & Control (C2) Establishment: Once the payload is active in memory, it begins to fingerprint the compromised host. This involves gathering information about the system’s configuration, user accounts, and network environment. Simultaneously, it establishes a connection to the attacker’s command-and-control (C2) server. This connection is crucial for receiving further instructions and downloading the second-stage payload, which typically contains the ransomware’s core encryption functionality. The malware also initiates a persistent polling loop to continuously await new commands from the C2.
-
Post-Exploitation and Lateral Movement: Following successful C2 communication and payload acquisition, LeakNet moves into the post-exploitation phase. This stage is characterized by techniques designed to escalate privileges, discover sensitive information, and move laterally across the network.
-
DLL Sideloading: The attackers employ DLL sideloading, a technique where a legitimate application loads a malicious DLL file. In LeakNet’s case, this has been observed with
jli.dllbeing loaded via Java inC:ProgramDataUSOShared. This directory, while seemingly innocuous, can be exploited by attackers to mask their malicious components. -
Credential Discovery: LeakNet actively seeks to harvest credentials. This includes using commands like
klistto enumerate Kerberos tickets, which can be leveraged to impersonate legitimate users and gain access to other systems or resources. -
Lateral Movement: To expand their reach within the compromised network, LeakNet utilizes established tools like PsExec. PsExec allows for the remote execution of commands on other systems, enabling the attackers to spread their influence and identify further targets for data exfiltration and encryption.
-
Data Staging and Exfiltration: Before encryption, LeakNet engages in data staging and exfiltration. They identify and gather valuable data from the network, and then exfiltrate it to attacker-controlled infrastructure. The observed abuse of Amazon S3 buckets for this purpose highlights their reliance on cloud services, which can offer a seemingly legitimate and scalable platform for data transfers.
-
Implications for Cybersecurity Defense
The consistent and repeatable nature of LeakNet’s attack chain, despite its sophisticated components, presents defenders with crucial opportunities for detection and mitigation. Cybersecurity researchers emphasize that while the tactics are advanced, they are not entirely invisible.
Key indicators that may signal potential LeakNet activity include:
- Deno Execution Outside Development Environments: The presence of the Deno runtime executing on systems not designated for software development is a significant anomaly.
- Suspicious "misexec" Execution: Any unusual execution of processes originating from browser-related activities, particularly those that might be misidentified or disguised as legitimate execution, warrants investigation.
- Abnormal PsExec Usage: Unscheduled or unauthorized use of PsExec, especially from unexpected sources or at unusual times, is a strong indicator of malicious lateral movement.
- Unexpected Outbound Traffic to S3 Buckets: Anomalous or high-volume outbound traffic directed towards Amazon S3 buckets, particularly from systems that do not typically interact with cloud storage services, should be flagged.
- DLL Sideloading in Non-Standard Directories: The loading of DLL files in unconventional or temporary directories, such as the observed
C:ProgramDataUSOShared, is a classic indicator of a sideloading attack.
Broader Impact and Defensive Strategies
The rise of actors like LeakNet, employing advanced evasion techniques, underscores the need for a multi-layered and adaptive cybersecurity strategy. Organizations must move beyond traditional signature-based defenses and embrace more behavioral and anomaly-detection approaches.
"The cybersecurity industry is in a constant arms race," commented Dr. Anya Sharma, a leading cybersecurity analyst. "Threat actors are increasingly sophisticated in their use of legitimate tools for malicious purposes. This ‘living off the land’ technique, as exemplified by LeakNet’s use of Deno, makes detection incredibly challenging. It requires security teams to have deep visibility into their network and endpoint activities, coupled with robust threat intelligence."
Defensive strategies should focus on:
- Enhanced Endpoint Detection and Response (EDR): EDR solutions that monitor process behavior, memory usage, and network connections can detect the subtle indicators of in-memory execution and lateral movement.
- Application Whitelisting and Control: Implementing strict application whitelisting policies can prevent unauthorized executables, including legitimate but misused runtimes like Deno, from running.
- User Education and Awareness: Reinforcing user awareness training on social engineering tactics like ClickFix remains paramount. Users are often the first line of defense, and their vigilance can prevent initial compromise.
- Network Segmentation and Least Privilege: Network segmentation can limit the blast radius of an attack, preventing attackers from easily moving laterally. Adhering to the principle of least privilege ensures that user and system accounts have only the necessary permissions, thereby restricting the impact of compromised credentials.
- Proactive Threat Hunting: Regularly conducting threat hunting exercises to search for indicators of compromise that may not be caught by automated systems is crucial for early detection.
The evolution of LeakNet with its ClickFix and Deno-based attack vectors serves as a stark reminder that the threat of ransomware is not static. Continuous adaptation of defensive postures, coupled with a deep understanding of emerging attacker methodologies, is essential for organizations to protect themselves against these increasingly sophisticated cyber threats. The challenge lies not only in detecting known threats but also in anticipating and defending against the novel ways in which attackers leverage legitimate technologies to achieve their malicious ends.