
A critical security vulnerability within the Nginx UI, a popular web-based management interface for the Nginx web server, is currently being actively exploited in the wild, posing a severe risk of complete server takeover without the need for any authentication. The flaw, officially designated as CVE-2026-33032, exploits a weakness in the Model Context Protocol (MCP) support, leaving a crucial endpoint unprotected and susceptible to malicious manipulation. This discovery has sent ripples through the cybersecurity community, highlighting the persistent threat of unpatched vulnerabilities and the speed at which sophisticated attackers can leverage them.
The Anatomy of the Vulnerability: CVE-2026-33032
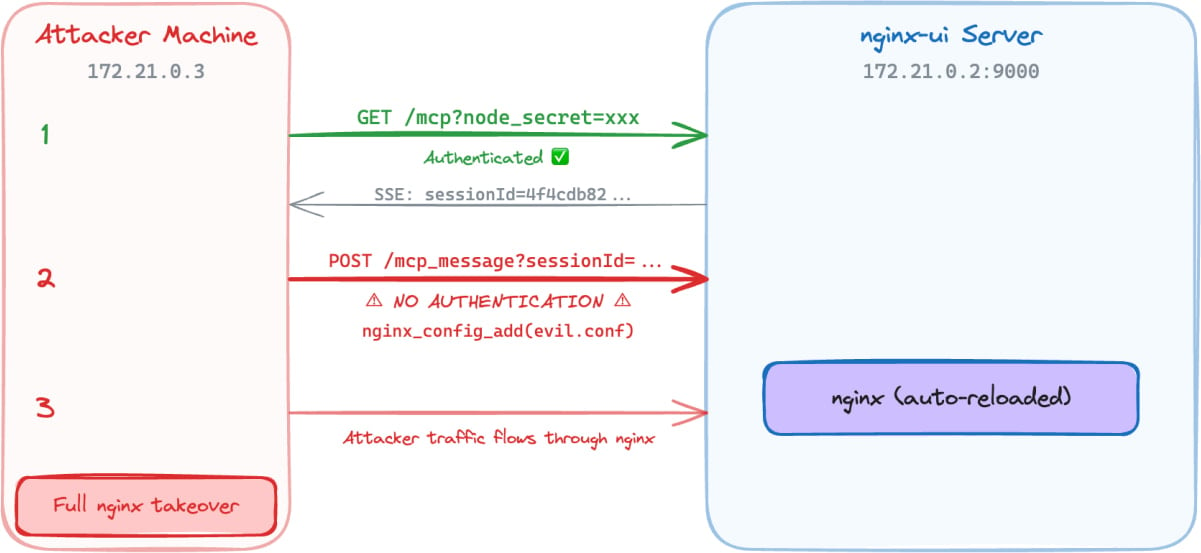
The root cause of the vulnerability lies in the Nginx UI’s failure to adequately secure the /mcp_message endpoint. This endpoint is designed to handle privileged Model Context Protocol (MCP) actions. However, due to a misconfiguration or oversight, it remains accessible to remote attackers without requiring any form of credential verification. MCP is a powerful protocol that allows for direct interaction with the Nginx server’s core functionalities, including the ability to modify configuration files and restart or reload the server process.
By exploiting this unauthenticated access, attackers can effectively issue commands that would normally require administrative privileges. The implications are profound: a single, unauthenticated request directed at the /mcp_message endpoint can lead to the modification of Nginx configuration files. This modification can alter the server’s behavior, redirect traffic, inject malicious content, or even grant the attacker complete control over the web server’s operations, effectively achieving a full server takeover.
The National Vulnerability Database (NVD) description of the flaw succinctly summarizes the severity: "[…] any network attacker can invoke all MCP tools without authentication, including restarting nginx, creating/modifying/deleting nginx configuration files, and triggering automatic config reloads – achieving complete nginx service takeover." The CVSS score assigned to this vulnerability underscores its critical nature, typically reflecting a high level of exploitability and impact. While the original article did not explicitly state the CVSS score, vulnerabilities of this nature often fall into the 9.0-10.0 range (Critical).

A Rapidly Evolving Threat Landscape: Timeline and Discovery
The discovery of CVE-2026-33032 paints a picture of swift vulnerability research and disclosure, followed by equally rapid exploitation. Researchers at Pluto Security AI, a company specializing in AI workflow security, identified the vulnerability and responsibly reported it to NGINX on March 14th. NGINX, demonstrating a commendable commitment to security, released a fix for the flaw in version 2.3.4 of the Nginx UI on March 15th, a mere day after the initial report.
However, the public disclosure of the vulnerability, including its identifier (CVE-2026-33032), detailed technical explanations, and a proof-of-concept (PoC) exploit, emerged at the end of March. This timeline is not uncommon in the cybersecurity world, allowing vendors a window to patch before widespread public knowledge of a flaw. Despite the vendor’s swift response, the emergence of public PoCs significantly lowers the barrier to entry for attackers, transforming a theoretical risk into an immediate and active threat.
The urgency of the situation was further underscored by a report from Recorded Future, a prominent threat intelligence company. In their "CVE Landscape" report, published earlier this week (relative to the original article’s publication), Recorded Future explicitly noted that CVE-2026-33032 was already under active exploitation. This confirmation from a leading threat intelligence firm validates the concerns raised by Pluto Security AI and serves as a stark warning to organizations relying on Nginx UI.
Widespread Exposure and Attack Methodology
The Nginx UI is a widely adopted component within the web server ecosystem. Its popularity is evident in its substantial presence on platforms like GitHub, where it boasts over 11,000 stars, and Docker, with hundreds of thousands of pulls, indicating its extensive use in various deployment scenarios. This widespread adoption, unfortunately, translates into a large potential attack surface.
Pluto Security’s extensive internet scans, leveraging the Shodan search engine, revealed a concerning number of publicly exposed instances that are potentially vulnerable. Their findings indicated approximately 2,600 publicly accessible Nginx UI instances that could be susceptible to attacks exploiting CVE-2026-33032. The geographical distribution of these vulnerable instances is significant, with a notable concentration in China, the United States, Indonesia, Germany, and Hong Kong. This global spread means that organizations across different regions are at risk.

The technical details of the exploitation, as outlined by Yotam Perkal of Pluto Security, are relatively straightforward, further contributing to its widespread threat. The attack requires only network access to the vulnerable Nginx UI instance. The process involves establishing a Server-Sent Events (SSE) connection, which is a standard web technology for pushing updates from a server to a client. Following this, an MCP session is initiated. The critical step involves capturing the sessionID returned by this session. This sessionID is then used to send unauthenticated requests to the /mcp_message endpoint.
Once authenticated through the compromised sessionID, attackers can then freely invoke any MCP tool. This includes, but is not limited to:
- Restarting the Nginx service: This can be used to disrupt service availability or to apply malicious configurations without detection.
- Creating, modifying, or deleting Nginx configuration files: This is the most direct path to server takeover, allowing attackers to inject malicious code, redirect traffic, or exfiltrate data.
- Triggering automatic configuration reloads: This ensures that any malicious changes made to the configuration are quickly applied to the running Nginx server.
Pluto Security’s demonstration of the exploit clearly illustrates how an attacker can leverage the unauthenticated MCP message endpoint to execute these privileged Nginx management actions. This capability allows for complete configuration injection and, ultimately, the full compromise of the Nginx server.
Broader Implications and Recommendations
The active exploitation of CVE-2026-33032 carries significant implications for organizations worldwide. The ease of exploitation, coupled with the critical impact of a full server takeover, makes this a high-priority threat. The ability for unauthenticated attackers to gain administrative control over web servers can lead to a cascade of negative consequences, including:
- Data Breaches: Sensitive customer data, proprietary information, and financial records stored on or accessible through the compromised server can be stolen.
- Service Disruption: Attackers can deface websites, take services offline, or disrupt critical business operations, leading to financial losses and reputational damage.
- Malware Distribution: Compromised servers can be used to host and distribute malware to unsuspecting users, further spreading the attack.
- Lateral Movement: A compromised web server can serve as a pivot point for attackers to move deeper into an organization’s network, targeting other systems and sensitive data.
- Ransomware Attacks: Attackers could encrypt critical data on the server and demand a ransom for its decryption.
- Botnet Integration: The compromised server could be enlisted into a botnet for distributed denial-of-service (DDoS) attacks or other malicious activities.
Given the confirmed active exploitation and the availability of public proof-of-concept exploits, the recommendation from security professionals is unequivocal: immediate patching is essential. System administrators and security teams are urged to apply the latest security updates to their Nginx UI installations as a matter of utmost urgency.
The latest secure version of nginx-ui, which addresses CVE-2026-33032, is 2.3.6, released on April 8th, 2026. This version supersedes the initial fix provided in 2.3.4 and represents the most current and secure state of the software. Organizations that have not yet updated should prioritize this action above almost all other security tasks.
For those unable to immediately update, mitigating measures might include:
- Network Segmentation: Restricting access to the Nginx UI management interface to only trusted IP addresses or internal networks.
- Firewall Rules: Implementing strict firewall rules to block all incoming traffic to the Nginx UI’s management port from untrusted sources.
- Intrusion Detection/Prevention Systems (IDS/IPS): Ensuring that IDS/IPS systems are configured to detect and block the specific patterns associated with this exploit.
- Regular Auditing: Conducting frequent security audits of Nginx configurations and server logs to detect any unauthorized changes or suspicious activity.
The incident serves as a potent reminder of the ongoing cybersecurity challenges faced by organizations. Even with rapid vendor patching, the window between vulnerability discovery, public disclosure, and active exploitation can be perilously short. Proactive vulnerability management, robust patching strategies, and continuous security monitoring are not merely best practices but essential components of a resilient security posture in today’s threat landscape. The Nginx UI vulnerability, CVE-2026-33032, is a clear case study of how a single unpatched flaw can lead to catastrophic consequences when actively exploited by determined adversaries.







