A sophisticated and far-reaching supply chain attack, attributed to the persistent threat actor behind the "GlassWorm" campaign, has recently resurfaced, impacting a significant number of open-source projects. Researchers have identified a coordinated effort that has compromised over 400 code repositories, packages, and extensions across major platforms including GitHub, npm, and the VSCode/OpenVSX ecosystems. This latest offensive marks an escalation in the campaign’s scope and technical complexity, raising alarms within the cybersecurity community about the vulnerability of the open-source software development pipeline.
The extensive nature of this recent wave of attacks has been meticulously documented by a consortium of cybersecurity researchers from Aikido, Socket, Step Security, and the OpenSourceMalware community. Their collective analysis points to a single, highly organized threat actor orchestrating these widespread compromises. Evidence for this unified operation includes the consistent use of a specific Solana blockchain address for command-and-control (C2) communications, the deployment of identical or functionally equivalent malicious payloads, and the leveraging of shared infrastructure across the compromised components.
The GlassWorm malware first gained notoriety in October of the previous year, where it was observed employing an insidious technique: the use of "invisible" Unicode characters to conceal malicious code within software packages. This initial wave primarily targeted cryptocurrency wallet data and developer credentials, aiming to pilfer sensitive information. Since then, the campaign has demonstrated a persistent and evolving threat, characterized by multiple distinct waves of activity.
A Chronicle of Escalation: The Evolution of GlassWorm

The initial emergence of GlassWorm in October marked a significant threat due to its novel method of obfuscation. Attackers cleverly exploited Unicode characters that are visually imperceptible to human eyes but are interpreted differently by computer systems, allowing them to hide malicious scripts within seemingly innocuous code. This allowed them to exfiltrate cryptocurrency wallet information, a prime target for cybercriminals seeking to exploit the decentralized finance ecosystem.
Following its initial detection, GlassWorm did not disappear but rather adapted and expanded its attack vectors. Subsequent waves saw the malware infiltrate Microsoft’s official Visual Studio Code marketplace, a widely used platform for developers. Furthermore, it extended its reach to the OpenVSX registry, a crucial alternative for developers using IDEs that do not officially support the VS Code marketplace. This expansion was meticulously tracked by researchers like John Tuckner of Secure Annex, who identified these subsequent waves targeting these critical developer tools.
The malware’s evolution also included a concerted effort to target macOS systems. In one notable instance, GlassWorm was found to be distributing trojanized clients for popular hardware cryptocurrency wallets, such as Trezor and Ledger. This represented a direct assault on the security infrastructure of cryptocurrency holders, aiming to compromise their digital assets directly. Later, the campaign continued to target macOS developers through compromised extensions hosted on the OpenVSX registry, underscoring a consistent focus on the developer ecosystem.
The Latest Offensive: A Broader Reach and Deeper Compromise
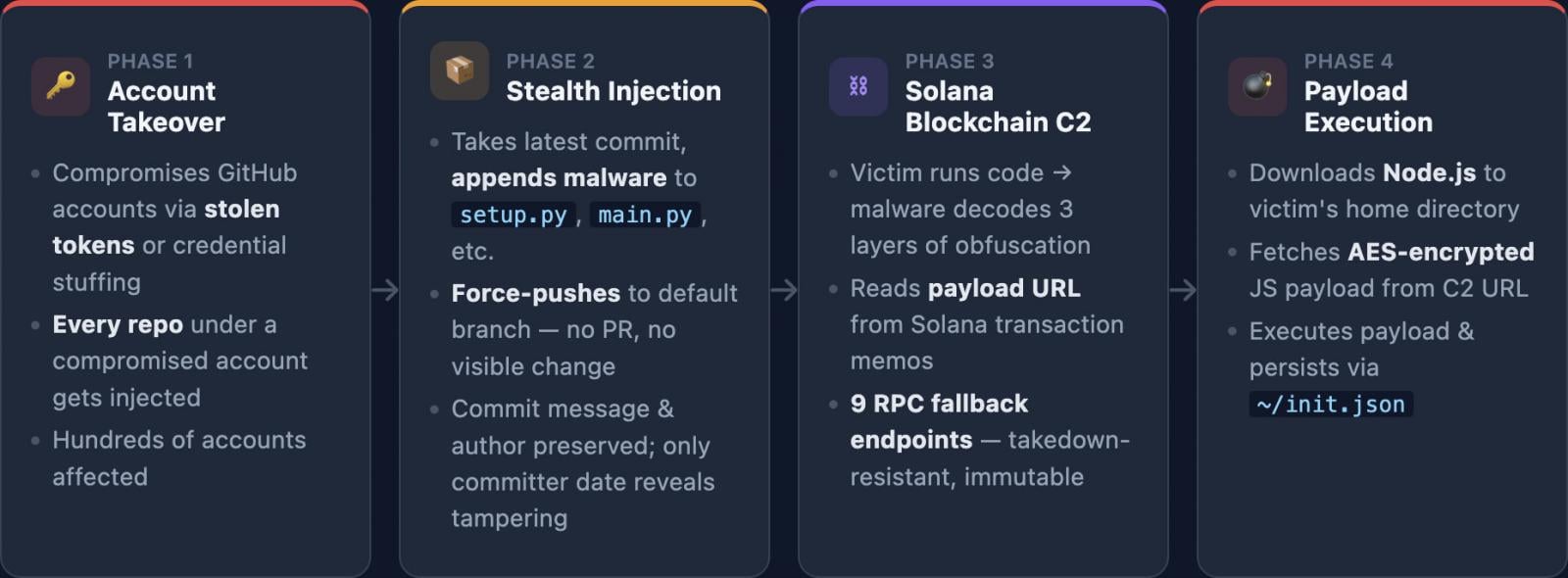
The current iteration of the GlassWorm attack campaign is characterized by its unprecedented scale and a more intricate multi-stage approach. The initial point of compromise typically occurs on GitHub, where threat actors gain unauthorized access to developer accounts. Once access is secured, they employ malicious commits, often using a "force-push" technique to overwrite legitimate code with their own malicious alterations. This allows them to inject their malware directly into the codebase of unsuspecting projects.
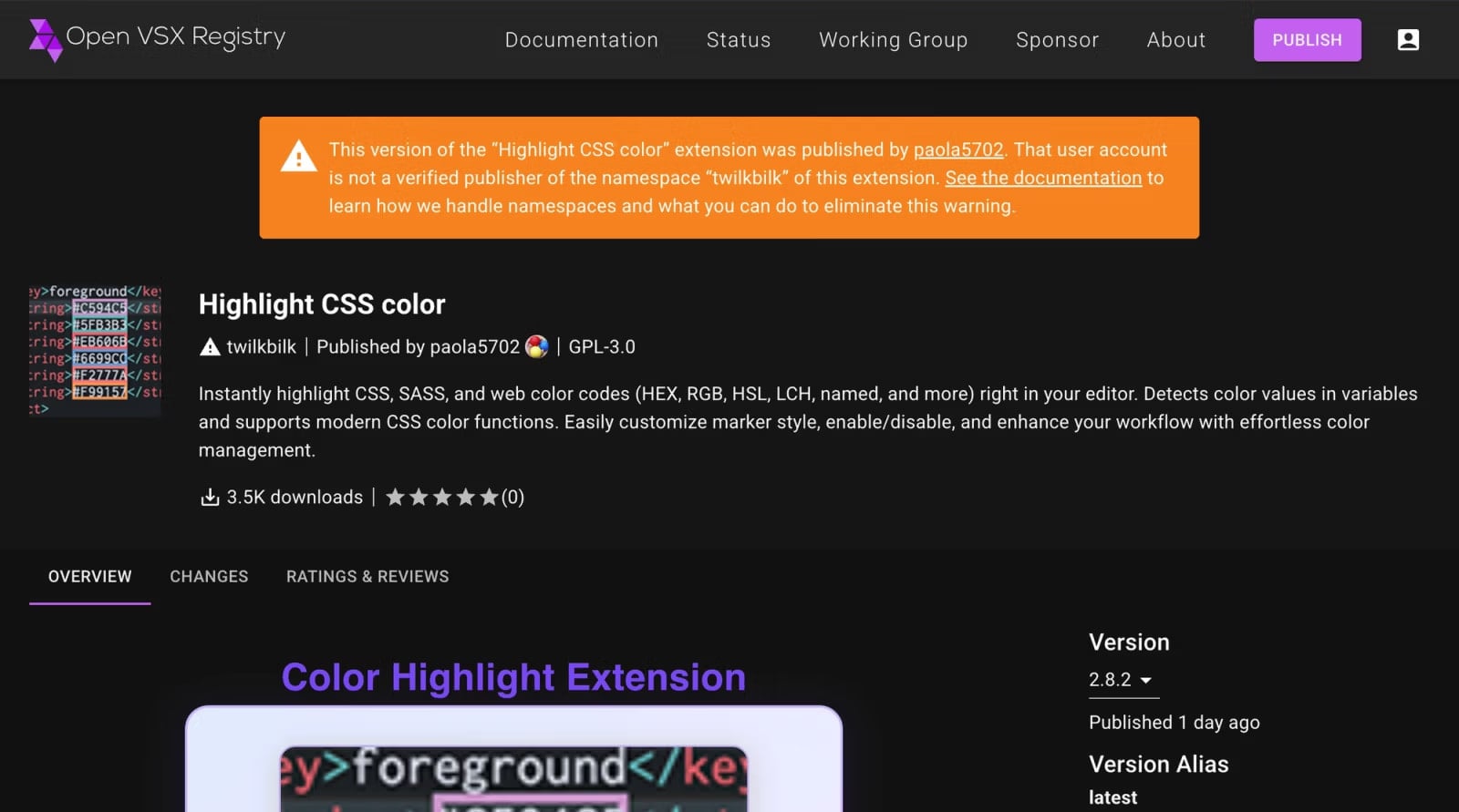
Following the compromise of repositories on GitHub, the malicious code is then disseminated through various open-source package managers and extension marketplaces. This includes the publishing of tainted packages on npm, the de facto standard package manager for Node.js, and the uploading of malicious extensions to both the VSCode marketplace and the OpenVSX registry. In these instances, the obfuscation techniques, including the use of invisible Unicode characters, are again employed to evade automated security scans and human inspection, making detection exceptionally challenging.
The Solana Blockchain: A Central Command and Control Nexus
A key element of the GlassWorm campaign’s operational efficiency and resilience is its reliance on the Solana blockchain for command and control (C2) activities. Researchers have observed that the malware queries the Solana blockchain at remarkably short intervals, specifically every five seconds, in search of new instructions. This continuous monitoring allows the threat actors to dynamically update their malicious payloads and directives without requiring direct access to the compromised systems.
Data analyzed by Step Security reveals a significant number of transactions on the Solana blockchain between November 27, 2025, and March 13, 2026. During this period, over 50 new transactions were recorded, with the primary purpose of updating the URL pointing to the malicious payload. These crucial instructions are embedded as "memos" within the blockchain transactions, a common practice for embedding arbitrary data. Upon receiving these instructions, the compromised systems are then directed to download the Node.js runtime and execute a JavaScript-based information stealer. This sophisticated C2 mechanism provides a high degree of stealth and adaptability, making it difficult to disrupt the attackers’ operations.
Targets and Tactics: What GlassWorm Steals
The ultimate objective of the GlassWorm malware is the exfiltration of highly sensitive data. Its primary targets include:
- Cryptocurrency Wallet Data: This encompasses private keys, seed phrases, and other credentials necessary to access and control digital assets, making it a lucrative target for financially motivated cybercriminals.
- Developer Credentials and Access Tokens: Compromising these credentials can grant attackers access to a wide range of systems, including cloud infrastructure, code repositories, and internal networks, facilitating further lateral movement and data theft.
- SSH Keys: These are critical for secure remote access to servers and systems. Their compromise can lead to unauthorized access and control over critical infrastructure.
- Developer Environment Data: This can include configuration files, project secrets, and other sensitive information that can be leveraged for further attacks or intellectual property theft.
Attribution and Indicators of Compromise
While definitive attribution remains challenging, analysis of the malware’s code comments and its operational characteristics provide some clues. Evidence suggests that the GlassWorm campaign is orchestrated by Russian-speaking threat actors. This hypothesis is further supported by the malware’s behavior, which includes skipping execution if a Russian locale is detected on a compromised system. However, cybersecurity researchers emphasize that this is not yet sufficient evidence for confident attribution, as threat actors often employ misdirection tactics.
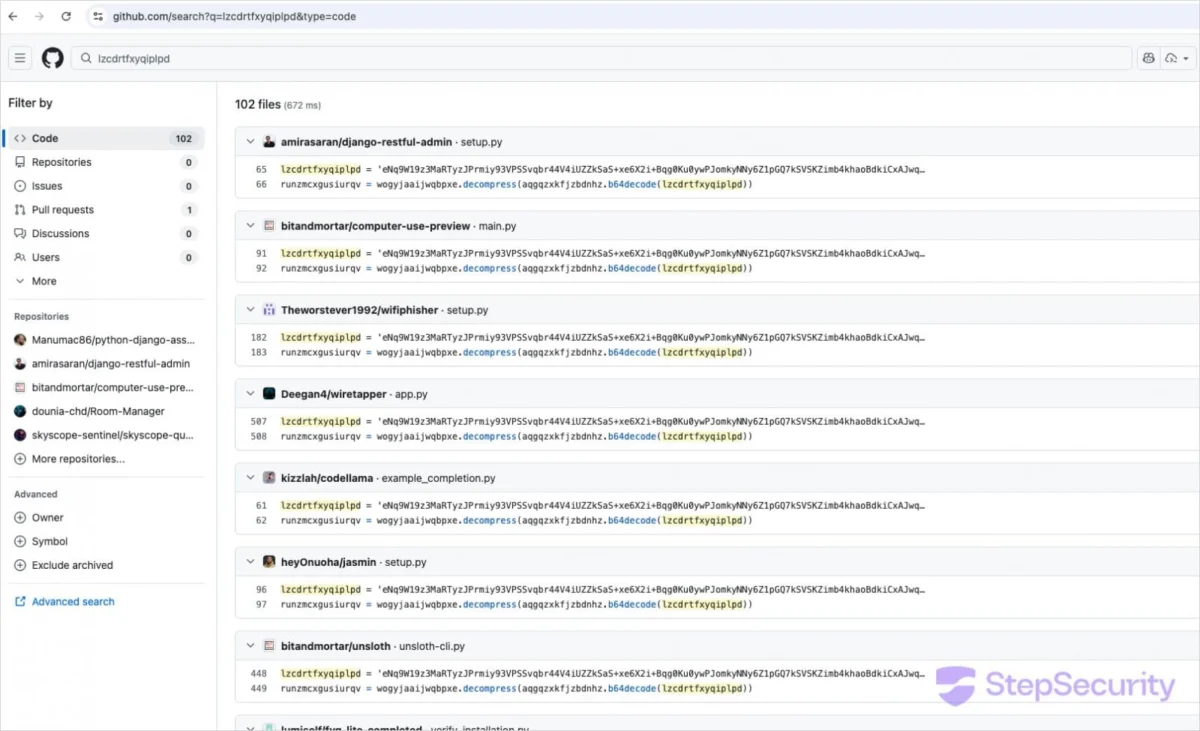
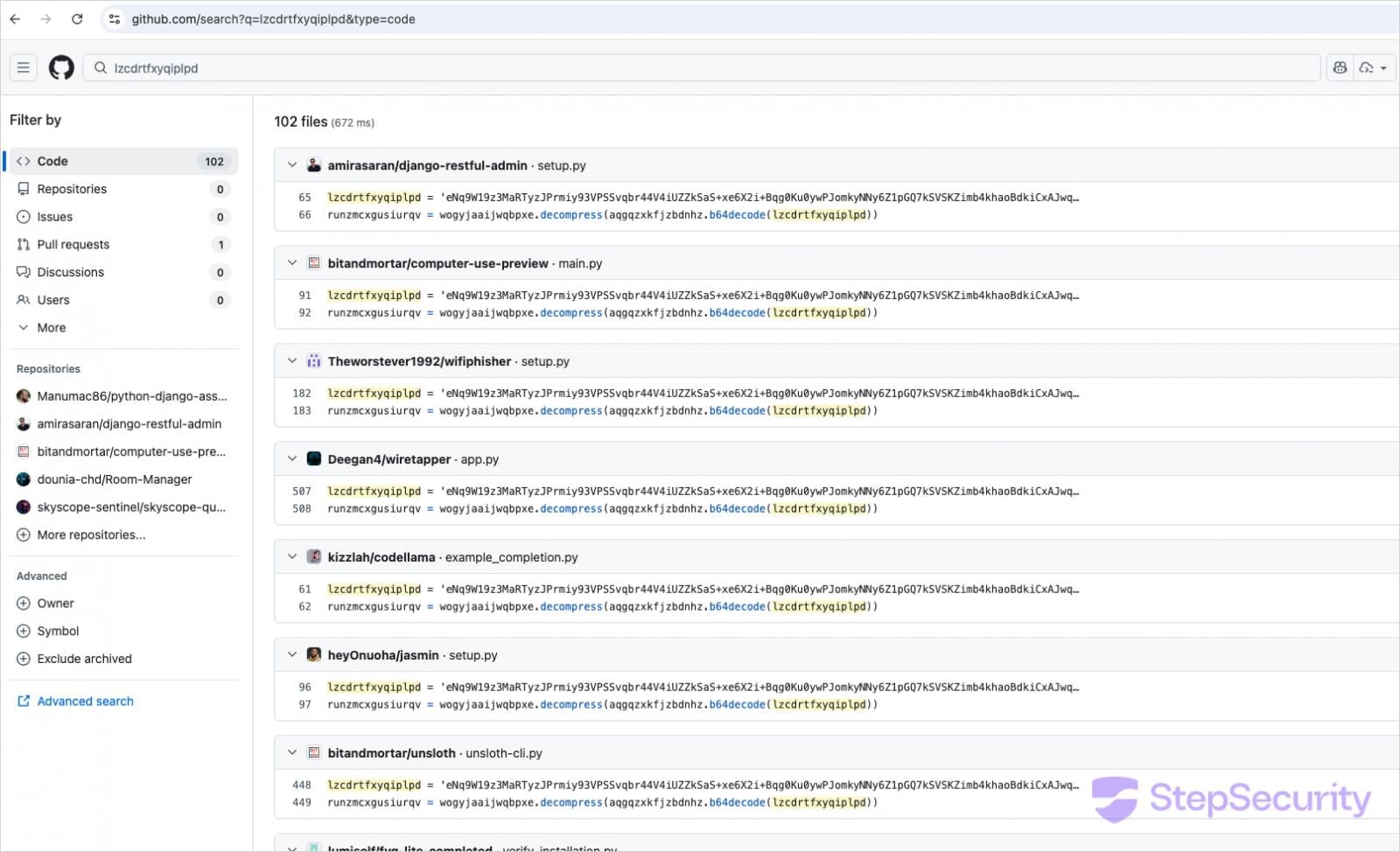
To aid developers in identifying and mitigating the threat, Step Security has provided specific indicators of compromise. Developers who directly install Python packages from GitHub or clone repositories are advised to scrutinize their codebase for the presence of the marker variable lzcdrtfxyqiplpd. This variable is a known indicator associated with the GlassWorm malware.
Furthermore, systems should be inspected for the existence of the ~/init.json file, which is used by the malware to establish persistence on the compromised system. Unexpected installations of the Node.js runtime in the user’s home directory, particularly those with version numbers like ~/node-v22*, should also raise suspicion.
Developers are also encouraged to search for suspicious i.js files within recently cloned projects. A thorough review of Git commit histories is also recommended, looking for anomalies such as commits where the committer date is significantly more recent than the original author date, which could indicate a malicious rewrite of the code.
Broader Implications for the Open-Source Ecosystem
The sustained and evolving threat posed by GlassWorm highlights critical vulnerabilities within the open-source software supply chain. The reliance on open-source components is a cornerstone of modern software development, offering efficiency and innovation. However, this interconnectedness also creates a single point of failure if malicious actors can compromise popular libraries or tools.
The success of GlassWorm in infiltrating multiple platforms and compromising hundreds of components underscores the need for enhanced security measures throughout the open-source ecosystem. This includes more rigorous vetting of contributions, improved vulnerability scanning for packages and extensions, and greater awareness among developers about supply chain risks. The use of blockchain for C2 communication also signals a new frontier in attack methodologies, requiring adaptive security strategies to counter such innovative approaches.
The continuous evolution of GlassWorm serves as a stark reminder that the threat landscape is constantly shifting. As developers and organizations continue to rely heavily on open-source software, the diligence and proactive security measures employed by both creators and consumers of these components will be paramount in safeguarding against sophisticated supply chain attacks. The collective efforts of researchers and the community in identifying and publicizing these threats are vital in fostering a more secure digital environment.







