
The Federal Bureau of Investigation (FBI) is actively pursuing leads in a significant cybersecurity investigation targeting malicious software embedded within games distributed on the popular digital gaming platform, Steam. The agency’s Seattle Division has issued a public appeal, urging gamers who may have installed any of eight identified fraudulent titles between May 2024 and January 2026 to come forward with crucial information. This probe centers on a sophisticated operation designed to compromise user accounts and pilfer sensitive financial data, particularly cryptocurrency.
The FBI’s proactive outreach, disseminated through official channels, aims to meticulously reconstruct the timeline and scope of the attacks. The notice explicitly states, "The FBI’s Seattle Division is seeking to identify potential victims installing Steam games embedded with malware. The FBI believes the threat actor primarily targeted users between the timeframe of May 2024 and January 2026." This extended timeframe suggests a sustained and potentially evolving campaign by the perpetrators.
Eight Suspect Games Identified in Broadening Investigation
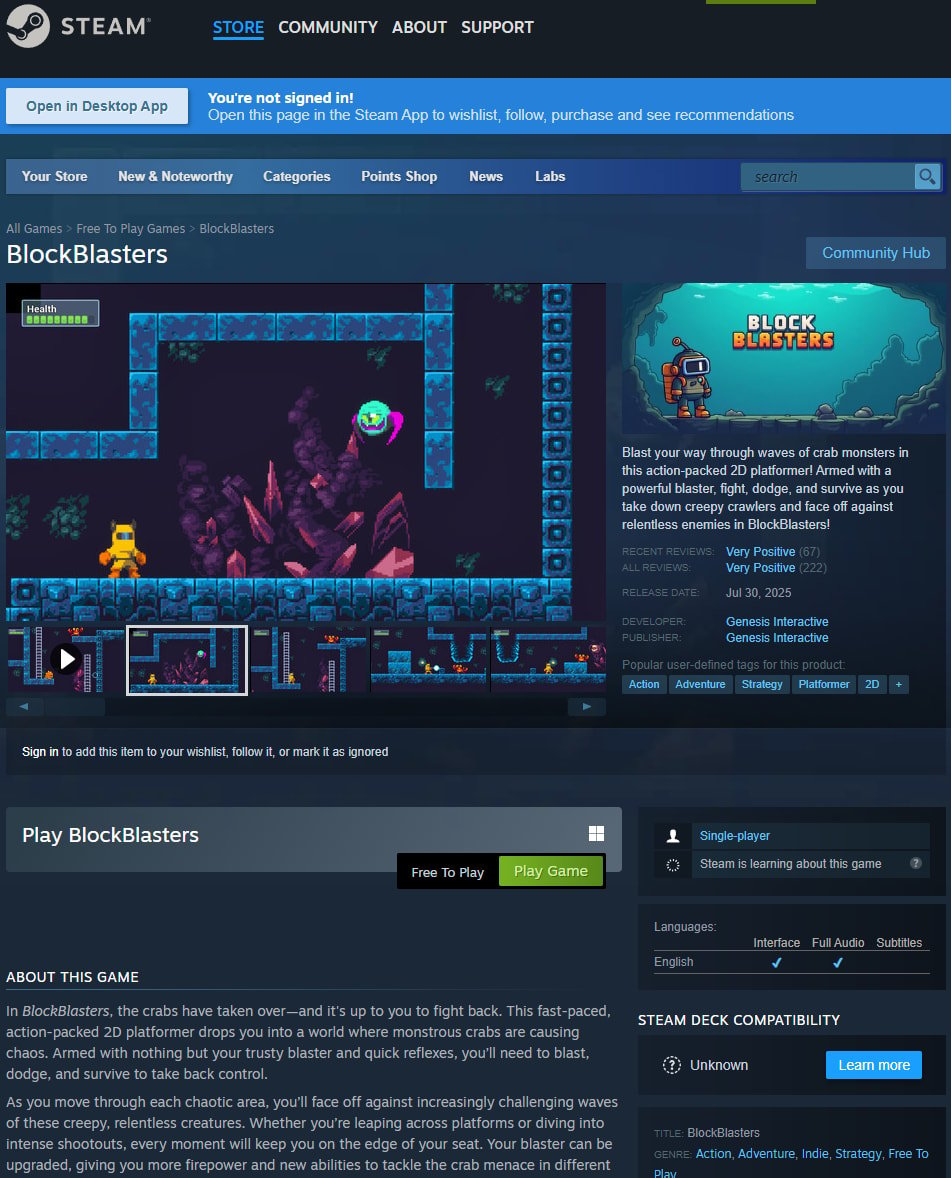
The FBI has publicly named several of the implicated games, providing a critical starting point for potential victims to self-identify. The identified titles include: BlockBlasters, Chemia, Dashverse/DashFPS, Lampy, Lunara, PirateFi, and Tokenova. The inclusion of these specific game titles allows the agency to narrow its focus and enables gamers to cross-reference their download histories with the ongoing investigation.
Individuals who believe they, or their minor dependents, may have fallen victim to these malicious games are encouraged to complete a short, secure online form provided by the FBI. This questionnaire is designed to gather specific details about their experiences, focusing on the nature of the compromise and the extent of any losses incurred. The FBI has emphasized the confidentiality of all victim identities, underscoring its commitment to protecting those who cooperate with the investigation.
Cryptocurrency Theft and Account Hijacking: The Primary Targets
A detailed examination of the FBI’s questionnaire reveals a clear emphasis on cryptocurrency theft and account hijacking as the primary objectives of the threat actors. Questions within the form delve into the specifics of cryptocurrency transactions, the extent of compromised accounts, and the estimated value of stolen funds. This focus highlights the lucrative nature of these cybercrimes and the sophisticated methods employed to exploit the decentralized financial landscape.

Furthermore, the FBI is requesting any screenshots of communications with individuals who promoted these fraudulent games. Such evidence is invaluable for investigators seeking to trace the flow of stolen cryptocurrency and identify the network of individuals responsible for distributing the malware. This approach underscores the multifaceted nature of the investigation, which seeks to dismantle not only the technical infrastructure of the attacks but also the social engineering and promotional efforts that facilitated their spread.
FBI’s Mandate and Commitment to Victim Support
The FBI’s involvement in this investigation stems from its legal mandate to identify victims of federal crimes. In its statement to BleepingComputer, the agency reiterated its commitment: "The FBI is legally mandated to identify victims of federal crimes it investigates. Victims may be eligible for certain services, restitution, and rights under federal and/or state law. All identities of victims will be kept confidential." This assurance aims to build trust and encourage wider participation from affected individuals.
The agency also confirmed the legitimacy of the communication channels being used. "The website and email listed in the mass notifications sent on March 12, 2026, are official and authorized by the FBI." This proactive clarification is crucial in combating potential phishing scams that might try to impersonate the FBI during such a high-profile investigation. For those with direct knowledge or who believe they have been affected, the FBI has also provided a dedicated email address: [email protected].
A Pattern of Deception: Malware Hidden Within Verified Steam Titles
The current FBI investigation is not an isolated incident but rather the culmination of a growing trend of malicious software being covertly introduced into the Steam ecosystem. Over the past two years, numerous games, some even appearing as "verified" titles on the platform, have been discovered to harbor information-stealing malware. These stealthy programs are meticulously designed to extract credentials, cryptocurrency wallet details, and other highly sensitive personal data directly from gamers’ computers.
One of the most widely publicized cases involved "BlockBlasters," a free-to-play 2D platformer that was available on Steam for a period between July and September 2024. Initially appearing as a legitimate and clean application, the game was later updated to include cryptodrainer malware. The malicious nature of BlockBlasters came to light dramatically during a livestream hosted by video game streamer Raivo Plavnieks, known as RastalandTV, who was engaged in a charity stream to raise funds for cancer treatment.
Following the download and installation of BlockBlasters, Plavnieks reported a staggering loss of over $32,000 from his cryptocurrency wallet. Subsequent investigations by blockchain analyst ZachXBT estimated the total losses to be approximately $150,000, affecting an estimated 261 Steam accounts. Cybersecurity researcher VX-Underground later provided an even higher figure, reporting that as many as 478 victims may have been impacted by this particular malicious game. This incident served as a stark warning of the increasing sophistication of malware distributed through seemingly trustworthy gaming platforms.
Another alarming case involved the survival crafting game "Chemia." Threat actors associated with the group known as EncryptHub reportedly injected HijackLoader malware into the game, which subsequently downloaded the Vidar information stealer. Further analysis revealed that Chemia also installed EncryptHub’s custom Fickle Stealer malware, a potent tool designed to exfiltrate credentials, browser data, cookies, and cryptocurrency wallet information. This multi-stage attack demonstrates a coordinated effort to maximize data extraction and financial gain.
The "PirateFi" game also emerged as a significant vector for malware distribution. This title was found to be spreading the Vidar infostealer and remained accessible on Steam for approximately one week in February 2025. It is estimated that as many as 1,500 users may have downloaded PirateFi before its eventual removal from the platform. Following the discovery, Steam issued a warning to players who had launched the game, alerting them to the potential execution of malicious files on their systems. The platform advised affected users to perform antivirus scans, review their installed software, and, in severe cases, consider reinstalling their operating system as a precautionary measure.
Broader Implications for Digital Security and Consumer Trust
The ongoing FBI investigation into malware-infiltrated Steam games carries significant implications for the broader digital security landscape and the trust consumers place in online platforms. The ease with which malicious actors can infiltrate a platform with millions of active users, and disguise their harmful software within seemingly legitimate applications, highlights systemic vulnerabilities.
The targeted nature of these attacks, specifically focusing on cryptocurrency and account credentials, underscores the evolving motivations of cybercriminals. As digital economies continue to expand, the value of personal financial data and digital assets becomes an increasingly attractive target. This investigation serves as a critical reminder for all users of online services to remain vigilant, practice robust cybersecurity hygiene, and be discerning about the software they download and install.
The FBI’s public appeal is a crucial step in mitigating further damage and bringing those responsible to justice. The agency’s commitment to transparency and victim support, while respecting confidentiality, is essential for fostering cooperation and rebuilding confidence in the digital marketplace. The success of this investigation will likely depend on the willingness of affected gamers to come forward and provide the necessary information, underscoring the collective responsibility in combating cyber threats.
The gaming industry, and platforms like Steam, face increasing pressure to implement more stringent security measures to vet applications and protect their user base. The revelation of these malicious games suggests that current verification processes may not be sufficient to detect sophisticated malware that is introduced or activated post-publication. Future developments in this investigation will undoubtedly shed more light on the specific methods used by the threat actors and inform potential improvements in platform security protocols. The FBI’s persistent efforts in pursuing these cybercriminals demonstrate a commitment to safeguarding digital assets and maintaining the integrity of online services for all users.







