
The Federal Bureau of Investigation (FBI) has issued a stark public service announcement, directly attributing a wave of sophisticated phishing campaigns to Russian intelligence-linked threat actors. These campaigns are specifically designed to compromise user accounts on widely used encrypted messaging applications, including Signal and WhatsApp. The warning, the first public instance of the FBI directly linking such operations to Russian intelligence services rather than a broader categorization of state-sponsored hackers, underscores a significant escalation in tactics aimed at circumventing the robust security features of these platforms. The FBI’s alert indicates that these malicious operations have already resulted in the compromise of thousands of accounts globally, with a particular focus on individuals possessing sensitive information.
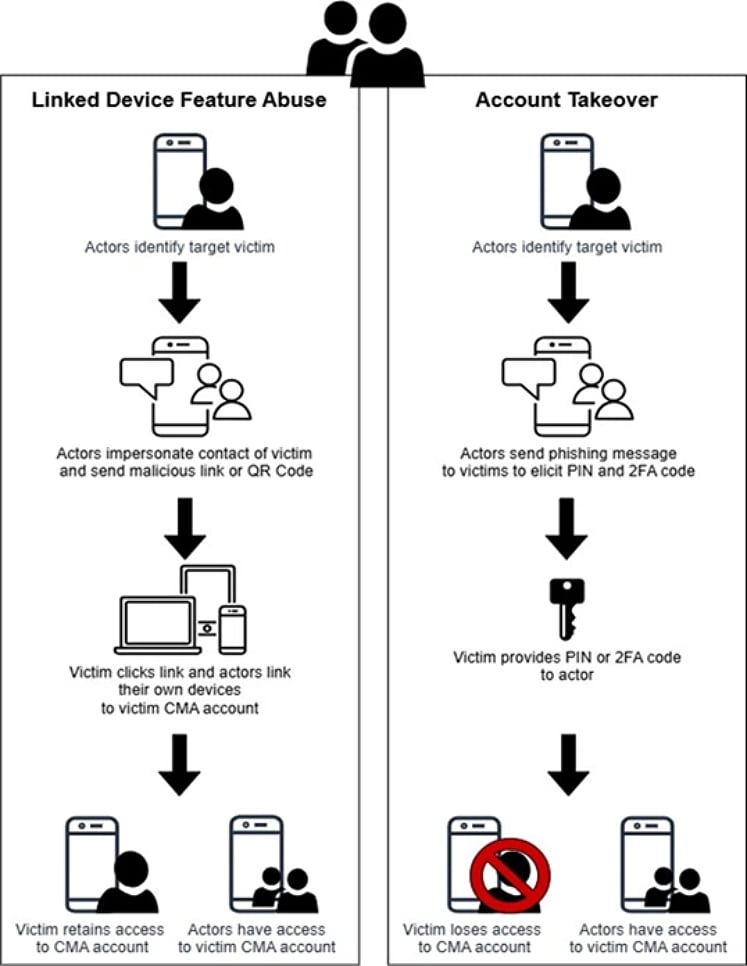
The core of these attacks, as detailed by the FBI, does not involve breaking the end-to-end encryption that secures communications on platforms like Signal and WhatsApp. Instead, the threat actors meticulously employ account hijacking techniques. This means they are not exploiting vulnerabilities within the encryption protocols themselves but rather manipulating users into inadvertently granting access or linking their accounts to malicious devices. The FBI noted that while these techniques are adaptable to various commercial messaging applications (CMAs), Signal users appear to be the primary targets. The potential fallout from a successful compromise is severe, ranging from unauthorized access to private messages and contact lists, to the ability of attackers to impersonate victims and launch further, more insidious phishing campaigns from a position of trusted contact.
The FBI’s public attribution follows a pattern of escalating warnings from international cybersecurity authorities. Earlier in October, Dutch intelligence agencies issued advisories detailing similar account-hijacking operations targeting Signal and WhatsApp users. These warnings highlighted the reliance of these attacks on tricking users into facilitating the addition of attacker-controlled accounts to their devices or linking their existing accounts to devices managed by the perpetrators. This corroboration from multiple national security agencies paints a clear picture of a coordinated and widespread effort.
Adding further weight to these concerns, France’s Cyber Crisis Coordination Center (C4) also published an alert on the same day as the FBI’s announcement, detailing the identical tactics being employed against instant messaging platforms. The French alert emphasized the pervasive nature of this activity, confirming its widespread and ongoing presence across numerous countries. This multi-national confirmation underscores the global reach and coordinated nature of these Russian intelligence-linked operations.

The Mechanics of Account Hijacking: Bypassing Encryption Through Deception
The common thread across all three advisories – from the FBI, Dutch intelligence, and France’s C4 – is the consistent methodology employed by the threat actors. They meticulously circumvent the strong encryption of messaging platforms by focusing on hijacking user accounts or illicitly linking devices to existing, legitimate accounts. This strategy cleverly bypasses the need to crack complex encryption algorithms, a feat that would be significantly more challenging and resource-intensive.
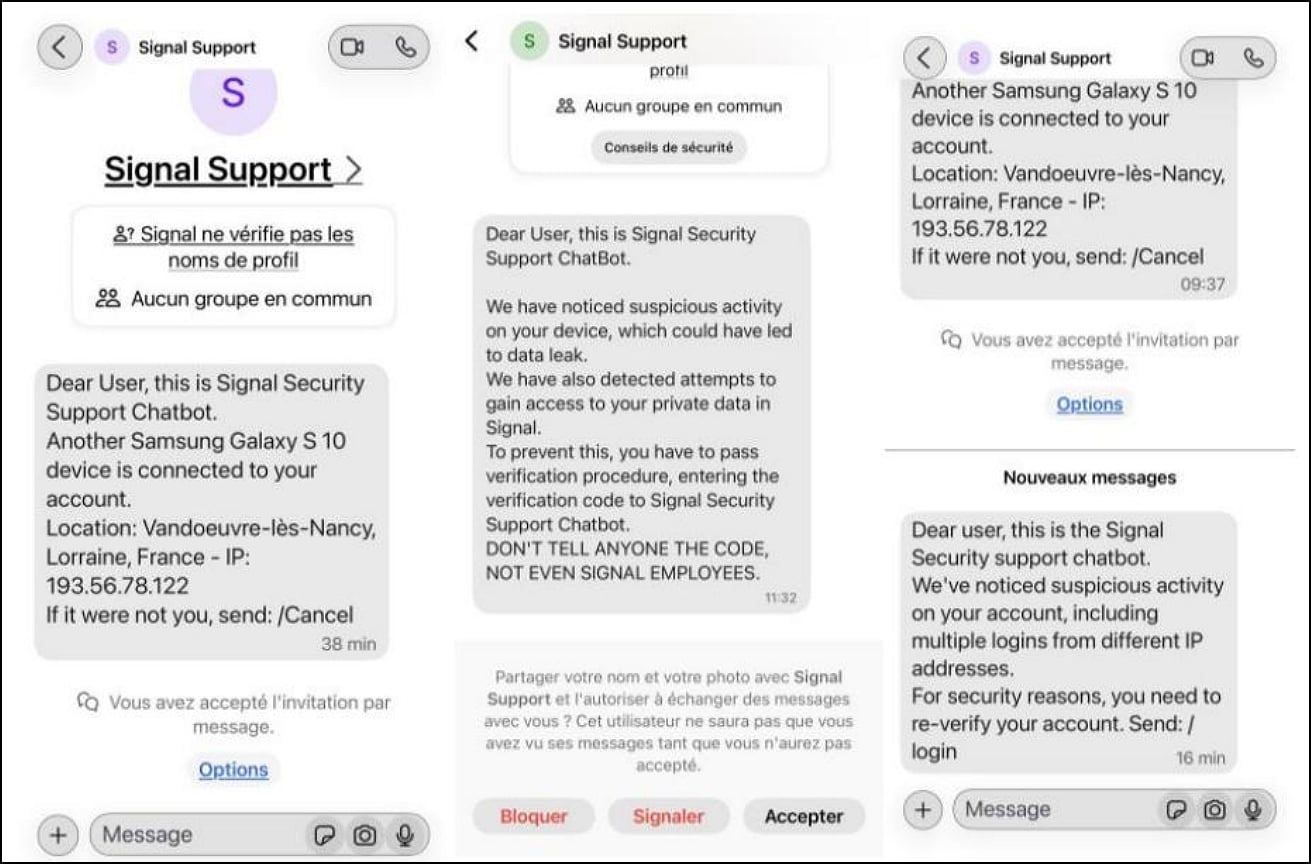
The FBI’s analysis reveals that a primary tactic involves the impersonation of official support accounts for the messaging applications. These fraudulent accounts then send messages to unsuspecting users, requesting them to perform a specific action. This action is carefully crafted to surreptitiously grant the threat actors the access they seek. Users are often duped into sharing critical verification codes, a crucial step in the account setup or device linking process for many messaging apps. In other instances, victims are persuaded to scan malicious QR codes. These QR codes, when scanned, link the user’s account to a device controlled by the attacker, effectively giving them a backdoor into the user’s communication history and contact network.
Signal, for example, allows users to link additional devices to their account through a process that often involves scanning a QR code or entering a code provided on the primary device. WhatsApp also employs a similar device-linking feature. The threat actors exploit the user’s trust in these official-looking support messages to initiate this linking process, but instead of linking to a new personal device, the user inadvertently links to the attacker’s device.
Once access is gained, the compromised accounts become powerful tools for further malicious activity. Threat actors can silently monitor all communications flowing through the compromised account. They can infiltrate existing group chats, potentially spreading disinformation or launching further phishing attacks from within a trusted group. Crucially, they can send messages impersonating the legitimate account holder, making it exceptionally difficult for the victim’s contacts to discern between authentic and fraudulent communications. This stealthy approach significantly hampers detection efforts and amplifies the potential for widespread exploitation.
The FBI’s PSA explicitly reassures users that the encryption mechanisms of Signal, WhatsApp, and similar platforms remain intact and secure. No inherent vulnerabilities within these encryption protocols are being exploited. The success of these attacks hinges entirely on social engineering and user deception, preying on the trust users place in support communications and the convenience of features like device linking.
Scope and Targets: High-Value Individuals Under Scrutiny
The FBI has indicated that the impact of this campaign is substantial, affecting "thousands" of accounts worldwide. The primary objective of these attacks appears to be the acquisition of sensitive information, suggesting a strategic targeting of individuals who possess such data.
The FBI’s public service announcement explicitly outlines the profile of the intended victims: "The activity targets individuals of high intelligence value, such as current and former U.S. government officials, military personnel, political figures, and journalists." This detailed description points towards a sophisticated intelligence-gathering operation, aiming to infiltrate circles of influence and access classified or sensitive information that could be leveraged for geopolitical advantage or other strategic purposes. The involvement of Russian intelligence services in targeting these specific demographics raises significant concerns about national security and the potential for espionage.
The timeline of these revelations suggests a growing awareness and concern among cybersecurity agencies. While the FBI’s public attribution is the most recent and direct, the groundwork was laid by earlier advisories from European counterparts. The Dutch intelligence agencies’ warning earlier in October provided critical insights into the tactics being employed. Subsequently, France’s C4 alert corroborated and expanded upon these findings, highlighting the widespread and ongoing nature of the threat. This coordinated international response indicates a shared understanding of the severity and nature of the threat posed by these Russian intelligence-linked operations.
Broader Implications and User Guidance
The implications of these successful account hijacking campaigns are far-reaching. Beyond the immediate breach of privacy for individual users, the ability of state-sponsored actors to infiltrate communication channels of high-value targets presents a significant threat to national security and democratic processes. The potential for misinformation campaigns, the compromise of sensitive diplomatic or military communications, and the disruption of journalistic activities are all serious concerns.
The sophistication of these attacks, which rely on social engineering rather than cryptographic exploits, highlights the persistent vulnerability of even highly secure digital systems when human factors are involved. The ease with which users can be tricked into compromising their own accounts underscores the critical need for enhanced cybersecurity awareness and robust user education.
In response to these threats, the FBI, along with other agencies, has provided crucial guidance for users of encrypted messaging applications:
- Maintain Vigilance Against Unexpected Messages: Users should exercise extreme caution with any unsolicited messages, especially those requesting immediate action or personal information.
- Be Wary of Device Linking Requests: Users should be highly suspicious of any requests to scan QR codes or link their accounts to new devices, particularly if these requests come from unexpected sources or impersonate official support.
- Never Share Verification Codes: Verification codes are a critical security layer. Users must never share these codes with anyone, including individuals or accounts claiming to be official support personnel.
- Verify Authenticity: When in doubt, users should independently verify the authenticity of any communication by contacting the platform’s official support channels through their website or app, rather than relying on contact information provided within a suspicious message.
The ongoing nature of these campaigns, confirmed by multiple international agencies, necessitates a sustained and collective effort to counter these evolving threats. The focus on account hijacking serves as a critical reminder that even the strongest encryption can be rendered ineffective by sophisticated social engineering tactics. As these threats continue to evolve, user education and proactive security measures remain paramount in safeguarding digital communications.







