Cybercriminals have escalated their campaign of exploiting a critical remote code execution (RCE) vulnerability in the Marimo reactive Python notebook, leveraging the popular Hugging Face Spaces platform to distribute a sophisticated new variant of the NKAbuse malware. The exploitation of CVE-2026-39987, a flaw that allows unauthenticated attackers to execute arbitrary code, began just hours after its technical details became publicly available last week. Cloud security firm Sysdig has been actively monitoring the situation, uncovering a concerning trend of increasingly aggressive and diverse attack tactics.
The Marimo Flaw and Initial Exploitation
The vulnerability, officially designated CVE-2026-39987, presents a severe security risk to users of the Marimo notebook environment. Its nature as a pre-authentication RCE flaw means that attackers do not need to possess any credentials or even log into a vulnerable Marimo instance to initiate a compromise. This significantly lowers the barrier to entry for malicious actors, enabling rapid and widespread exploitation.
Sysdig’s initial observations indicated that the exploitation efforts commenced less than 10 hours after the disclosure of technical details. Early attacks were primarily focused on credential theft, a common objective for initial access in sophisticated cyber operations. This swift response by threat actors underscores the high value placed on this vulnerability within the cybercriminal underground. The speed at which these attacks materialized suggests that exploit code was either already prepared in anticipation of the disclosure or was rapidly developed by multiple groups.

Hugging Face Spaces: A New Vector for Malware Distribution
The latest wave of attacks, as identified by Sysdig researchers, reveals a cunning adaptation by threat actors: the weaponization of Hugging Face Spaces. Hugging Face, a prominent platform for the machine learning community, provides a collaborative environment for sharing AI models, datasets, and code. Its "Spaces" feature allows users to deploy and showcase interactive web applications directly from Git repositories, often used for demonstrations or tools related to AI.
In this specific campaign, attackers created a Hugging Face Space named vsccode-modetx. This name is a deliberate typosquat, mimicking the legitimate "VS Code" (Visual Studio Code) to potentially mislead unsuspecting users. Within this compromised Space, the attackers hosted two key components: a dropper script named install-linux.sh and a malware binary identified as kagent. The kagent binary itself is an apparent attempt to impersonate a legitimate Kubernetes AI agent, further camouflaging its malicious intent.
The exploitation chain works as follows: after successfully leveraging the Marimo RCE vulnerability, the attacker initiates a curl command. This command directs the compromised Marimo instance to download the install-linux.sh script from the Hugging Face Space. The use of Hugging Face Spaces, a legitimate and widely trusted HTTPS endpoint with a generally clean reputation, is a strategic move. This tactic significantly reduces the likelihood of triggering security alerts or being flagged by network intrusion detection systems, as the download originates from a seemingly innocuous source.
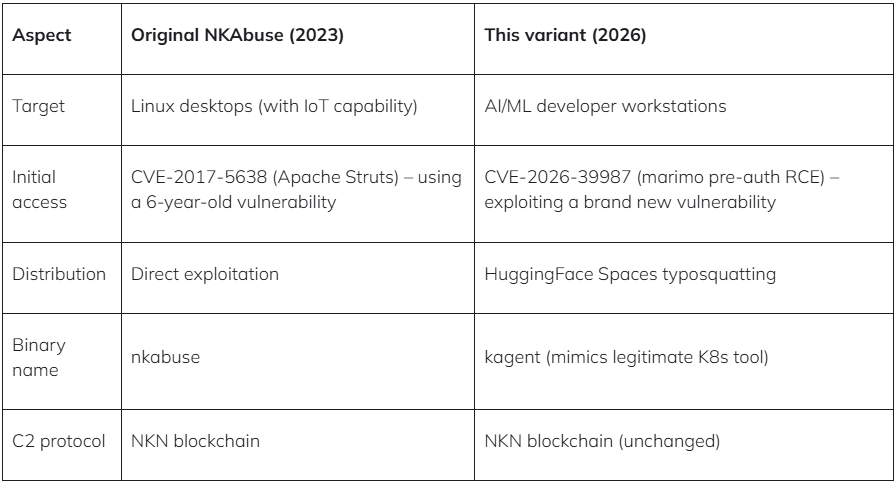
The NKAbuse Malware: Evolution and Capabilities
The payload delivered by the dropper script is a previously undocumented variant of the NKAbuse malware. This malware family first gained attention in late 2023 when researchers at Kaspersky detailed its novel approach to stealthy communication by abusing the NKN (New Kind of Network) decentralized peer-to-peer network. This decentralized architecture makes it considerably more challenging to track and disrupt command-and-control (C2) infrastructure compared to traditional centralized C2 servers.

According to Sysdig’s analysis, this new variant has evolved beyond its initial DDoS capabilities. It now functions as a sophisticated Remote Access Trojan (RAT). This means it can not only participate in distributed denial-of-service attacks but also execute arbitrary shell commands on infected systems. Crucially, the output of these executed commands is then exfiltrated back to the threat actor, providing them with direct control and visibility over the compromised environment.
Sysdig’s report elaborates on the technical underpinnings of this new NKAbuse variant: "The binary references NKN Client Protocol, WebRTC/ICE/STUN for NAT traversal, proxy management, and structured command handling – matching the NKAbuse family initially documented by Kaspersky in December 2023." This detailed technical insight confirms the lineage of the malware and highlights the sophisticated networking and communication techniques it employs to maintain persistence and evade detection. The inclusion of WebRTC/ICE/STUN further suggests an advanced capability to establish peer-to-peer connections and bypass network address translation (NAT) barriers, making it harder to block.
Chronology of Exploitation and Diversification of Tactics
The timeline of events paints a picture of rapid escalation and tactical evolution:
- Early Last Week: Technical details of CVE-2026-39987 in Marimo are publicly disclosed.
- Within 10 Hours of Disclosure: Initial exploitation attempts are detected, primarily focused on credential theft.
- Later Last Week: Sysdig researchers continue to monitor the situation, noting ongoing exploitation.
- April 12th Onwards: A new campaign emerges, leveraging Hugging Face Spaces to deploy a variant of NKAbuse.
- Ongoing: Sysdig observes other notable attacks utilizing the CVE-2026-39987 vulnerability with different objectives.
Beyond the NKAbuse deployment, Sysdig’s analysis uncovered other significant exploitation activities:
- Germany-Based Operator: This actor attempted a wide range of techniques, including 15 different reverse-shell methods across multiple ports. Following initial compromise, they focused on lateral movement within the network. A key tactic involved extracting database credentials from environment variables. Subsequently, they established connections to PostgreSQL databases, systematically enumerating schemas, tables, and configuration data, indicating a reconnaissance phase aimed at understanding the target’s data landscape.
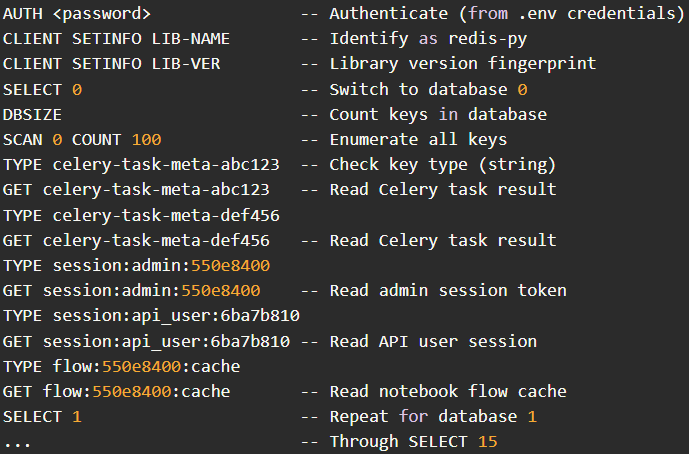
- Hong Kong-Based Actor: This attacker focused on exploiting stolen
.envcredentials to target a Redis server. They meticulously scanned all 16 available databases within the Redis instance and proceeded to dump stored data. This data likely included sensitive information such as user session tokens, application cache entries, and potentially other configuration secrets, offering valuable insights and access for further compromise.
These diverse attack vectors highlight that CVE-2026-39987 is not being exploited by a single, monolithic threat actor but rather by a spectrum of malicious entities with varying objectives and technical proficiencies. The common denominator is the ease of entry provided by the Marimo vulnerability.
Broader Impact and Implications
The exploitation of CVE-2026-39987 and the subsequent deployment of NKAbuse malware via Hugging Face Spaces carry significant implications for the cybersecurity landscape:
- Increased Sophistication of Attack Infrastructure: The use of platforms like Hugging Face for malware distribution signifies a growing trend of threat actors co-opting legitimate services. This blurs the lines between legitimate and malicious activity, making detection and mitigation more challenging for security teams. The reputation of these platforms acts as a shield, allowing malicious payloads to bypass initial security scrutiny.
- Evolution of Malware: The transformation of NKAbuse into a RAT with enhanced command execution and data exfiltration capabilities indicates a continuous development cycle within malware families. This necessitates ongoing research and threat intelligence to keep pace with emerging functionalities.
- Supply Chain Risks: The exploitation of a vulnerability in a development tool like Marimo, which is used to build and deploy applications, represents a form of supply chain risk. Compromising such tools can have a cascading effect, impacting numerous downstream applications and users.
- AI Community Vulnerability: The use of Hugging Face, a central hub for AI development, highlights the potential for the AI ecosystem itself to become a target or a vector for attacks. As AI tools become more integrated into critical infrastructure and business processes, securing these platforms becomes paramount.
- Need for Proactive Security Measures: The rapid exploitation of CVE-2026-39987 underscores the critical importance of timely patching and vulnerability management. Organizations must prioritize updating affected software as soon as patches become available, especially for vulnerabilities with publicly disclosed technical details.
Official Responses and Mitigation Strategies
While no direct statements from Hugging Face or Marimo developers regarding this specific exploitation campaign have been widely publicized at the time of reporting, the implied response from the cybersecurity community, particularly Sysdig, is clear: immediate action is required.
Sysdig’s recommendations for mitigating the risks associated with CVE-2026-39987 are direct and actionable:
- Immediate Upgrade: The most crucial step is to upgrade Marimo to version 0.23.0 or a later release. This version is expected to contain the necessary patches to address the vulnerability. Organizations should verify their Marimo installations and ensure they are running the latest secure version.
- Firewall Mitigation (If Upgrade is Not Possible): For environments where immediate upgrading is not feasible, Sysdig advises blocking external access to the
/terminal/wsendpoint. This endpoint is reportedly exploited by the vulnerability. Implementing firewall rules to deny inbound traffic to this specific path can serve as a temporary but effective measure to prevent exploitation. Blocking the endpoint entirely, if its functionality is not critical for external access, is also recommended.
The absence of immediate public statements from the affected software vendors does not diminish the severity of the situation. Security researchers often disclose findings to vendors first to allow for remediation before publicizing details. However, the rapid exploitation indicates that either the disclosure was broader, or the window for patching was exceptionally narrow.
The Evolving Threat Landscape
The exploitation of CVE-2026-39987 is a stark reminder of the dynamic and ever-evolving nature of cyber threats. Threat actors are continuously seeking out and exploiting vulnerabilities, adapting their tactics, and leveraging legitimate infrastructure to achieve their objectives. The weaponization of platforms like Hugging Face Spaces for malware distribution signals a concerning new frontier in cyberattacks, demanding vigilance and a proactive approach from both software developers and end-users.
Organizations must maintain a robust security posture that includes regular vulnerability scanning, prompt patching of known vulnerabilities, network segmentation, and comprehensive endpoint detection and response (EDR) solutions. Furthermore, fostering a culture of security awareness among employees is crucial to prevent them from falling victim to social engineering tactics or inadvertently downloading malicious content. The incident involving Marimo and NKAbuse serves as a critical case study, highlighting the need for continuous adaptation and resilience in the face of persistent and sophisticated cyber threats. The race to secure systems against these evolving threats is ongoing, and prompt action is the most effective defense.