
Identity protection giant Aura has officially confirmed a significant data breach that has exposed the personal information of nearly 900,000 marketing contacts. The incident, attributed to a sophisticated voice phishing (vishing) attack against an employee, resulted in the unauthorized access of names and email addresses belonging to a substantial number of individuals. While Aura asserts that highly sensitive data such as Social Security Numbers, account passwords, and financial information remained secure, the breach raises serious concerns about data security practices within the digital safety sector.
Genesis of the Breach: A Vishing Attack Unveils Sensitive Data
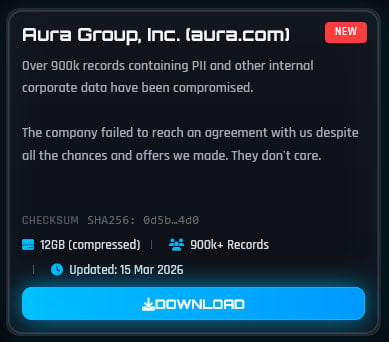
The breach, which came to light earlier this week when the notorious threat group ShinyHunters claimed responsibility on their data extortion site, was initiated through a deceptive vishing attack. This attack vector, increasingly prevalent in modern cyber threats, leverages social engineering tactics over voice calls to trick individuals into divulging sensitive information or granting unauthorized access. In this instance, the attackers successfully targeted an Aura employee, thereby gaining a foothold into the company’s systems.
According to Aura’s official statement, the compromised data originated from a marketing tool associated with a company acquired by Aura in 2021. This suggests that the vulnerability may have existed within the acquired entity’s systems prior to the integration, highlighting potential due diligence oversights during mergers and acquisitions. The exposed information is described by Aura as "limited" and pertains to marketing contacts, though the scale of the incident indicates a broader reach than initially suggested by the company’s initial assessment.
Scope of the Compromise: What Was Exposed and Who is Affected
The unauthorized access has impacted approximately 900,000 marketing contacts. Aura has specified that this includes data belonging to 20,000 current Aura customers and 15,000 former customers. The compromised data set encompasses full names, email addresses, home addresses, and phone numbers. Crucially, Aura has reiterated that core security data, including Social Security Numbers (SSNs), account passwords, and financial information, was not compromised. This distinction is vital for understanding the immediate risk to individuals, although the exposed contact details can still be exploited for further phishing attempts and identity manipulation.
The threat actor, ShinyHunters, claimed to have exfiltrated 12GB of files containing personally identifiable information (PII) on customers, as well as corporate data. The group subsequently leaked portions of the stolen data, citing a failure by Aura to reach an agreement with them despite what they termed "all the chances and offers" made. This indicates a potential ransomware or extortion element to the attack, where the threat actors sought financial gain in exchange for not releasing the data, or for its eventual release to further pressure the victim.
Independent Verification and Discrepancies
The independent cybersecurity service Have I Been Pwned (HIBP) has analyzed the leaked data and added it to its extensive database, a common practice when significant data breaches occur. HIBP’s analysis revealed additional details not explicitly mentioned in Aura’s initial statement, including customer service comments and IP addresses.

A notable discrepancy emerged regarding the total number of affected accounts. HIBP reported slightly over 901,000 affected accounts, a figure marginally higher than Aura’s confirmed count of 900,000. When questioned about this difference, Aura maintained that their figure was accurate. The company explained that the disparity stems from the nature of the data acquired through the marketing tool from the acquired company. While the database contained a large number of contacts, only approximately 35,000 of them were identified as actual Aura customers. The remaining contacts were likely leads, prospects, or individuals who had previously interacted with the acquired company’s marketing efforts.
Furthermore, HIBP stated that a significant majority, approximately 90%, of the email addresses exposed in this incident were already present in their database from previous security incidents. This suggests that many of the affected individuals have been victims of data breaches multiple times, increasing their overall vulnerability and the potential for sophisticated credential stuffing or targeted social engineering attacks.
Aura’s Response and Mitigation Efforts
In the wake of the breach confirmation, Aura has initiated a comprehensive internal review of its security protocols and data handling practices. This review is being conducted in partnership with external cybersecurity experts, a standard procedure to ensure an unbiased and thorough assessment of the incident and its contributing factors.
The company has also confirmed that it has formally notified law enforcement authorities about the breach. This engagement with law enforcement is crucial for potential investigation, prosecution of the perpetrators, and coordination of broader cybersecurity efforts.
Aura has committed to providing transparency to affected individuals. The company stated that personalized notifications will be sent to all individuals whose data was compromised. These notifications are expected to detail the specific information exposed and provide guidance on steps individuals can take to protect themselves from potential fallout.
Aura’s stance on the ShinyHunters claims regarding an alleged Okta SSO compromise remains undisclosed. The company declined to comment further on these specific allegations, which, if true, could indicate a more systemic security weakness extending beyond the initial vishing attack. Okta, a prominent identity and access management provider, has also experienced security incidents in the past, making such an alleged compromise a matter of significant concern for its extensive client base.
Broader Implications and Industry Context
The Aura data breach serves as a stark reminder of the persistent threats faced by even security-focused companies. Aura positions itself as an "all-in-one service for online protection," offering identity theft protection, credit and fraud monitoring, and online security tools, including phishing protection. The irony of a data breach occurring within a company dedicated to protecting consumers from such threats is not lost on cybersecurity professionals and the public alike.
This incident underscores several critical trends in the cybersecurity landscape:
- The Efficacy of Social Engineering: Vishing attacks, alongside phishing and smishing, continue to be highly effective methods for breaching corporate defenses. These attacks exploit human psychology rather than purely technical vulnerabilities, making them challenging to defend against solely through technological means.
- Supply Chain Risks: The involvement of data from an acquired company highlights the inherent risks associated with mergers and acquisitions. Robust due diligence and thorough security assessments of acquired entities are paramount to prevent inherited vulnerabilities from becoming active threats.
- The Persistent Threat of Data Extortion Groups: Groups like ShinyHunters continue to leverage data breaches for financial gain through extortion and public data leaks. Their operations highlight the financial incentives driving cybercrime and the need for organizations to have robust incident response plans that include negotiation and recovery strategies.
- The Value of PII: Even seemingly less sensitive data like names and email addresses can be highly valuable to cybercriminals. This information can be used for sophisticated phishing campaigns, account takeovers, and as a stepping stone for more significant attacks. The fact that 90% of the exposed emails were already in HIBP’s database indicates a population that is already highly targeted.
The breach also raises questions about the data retention policies and security measures employed by Aura and the acquired company. The fact that a marketing tool from a 2021 acquisition still held such a large volume of potentially sensitive contact information warrants scrutiny.
Moving Forward: Lessons Learned and Future Precautions
For individuals affected by this breach, the immediate steps should include heightened vigilance against phishing attempts, particularly those referencing Aura or seeking personal information. It is advisable to review account activity for any suspicious transactions or communications. Given that many individuals were already part of previous breaches, this incident adds another layer to their existing digital risk profile.
For companies, the Aura breach reinforces the need for:
- Continuous Security Training: Regular and comprehensive training for all employees on identifying and responding to social engineering threats, especially vishing.
- Robust Access Controls: Strict access controls and the principle of least privilege to limit the potential damage from any single compromised account.
- Third-Party Risk Management: Rigorous security assessments of all third-party vendors and acquired companies, including ongoing monitoring.
- Incident Response Preparedness: Well-defined and regularly tested incident response plans that address data breaches, including communication strategies and legal compliance.
- Data Minimization: Implementing policies to collect and retain only the data that is absolutely necessary, and securely disposing of data that is no longer required.
Aura’s commitment to notifying affected individuals and its collaboration with cybersecurity experts and law enforcement are positive steps. However, the long-term impact of this breach on consumer trust and Aura’s reputation remains to be seen. In an industry built on safeguarding digital lives, transparency, accountability, and demonstrable improvements in security posture will be critical for rebuilding confidence. The incident serves as a powerful case study on the evolving threat landscape and the paramount importance of a multi-layered, proactive approach to cybersecurity.







