On Saturday, the decentralized finance (DeFi) ecosystem was rocked by a significant cyberattack targeting Kelp, a prominent liquid restaking protocol. The exploit, which involved suspicious cross-chain activity, forced Kelp to immediately pause its smart contracts for its restaking token, rsETH, across multiple blockchain networks. Initial reports from blockchain security firm Cyvers indicate that the attack resulted in the loss of approximately $293 million in digital assets, sending shockwaves through the already volatile cryptocurrency market and prompting widespread defensive measures from other DeFi protocols.
The sophisticated breach exploited a vulnerability within Kelp’s rsETH adapter bridge contract, the critical software component responsible for managing the integrity and functionality of its rsETH token. This contract, designed to facilitate the seamless transfer and management of the restaking token across different blockchain layers, became the entry point for the malicious actor. The attacker was able to siphon a substantial amount of funds, highlighting a recurring theme of security challenges within the interconnected landscape of decentralized finance.
Chronology of the Attack and Immediate Aftermath
The incident unfolded rapidly on Saturday, with Kelp’s security team identifying the unusual activity in the early hours. In a statement posted on X (formerly Twitter), the Kelp platform announced the discovery of "suspicious cross-chain activity involving rsETH" and confirmed the immediate pausing of rsETH contracts across the mainnet and several Layer-2 scaling solutions. This swift action, while aimed at containing further losses, also signaled the severity of the breach.
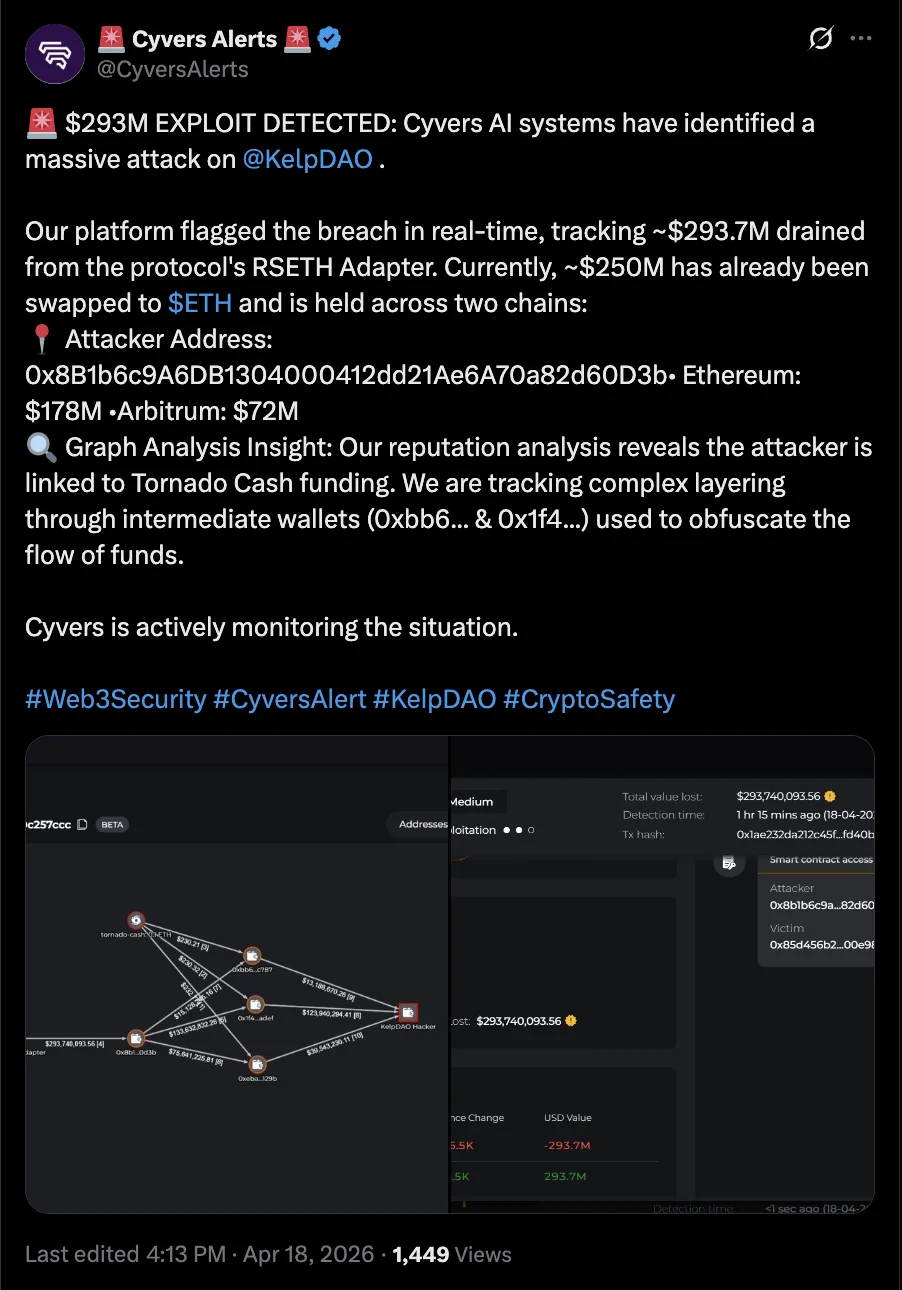
Blockchain security firm Cyvers was among the first to provide detailed insights into the exploit. Their analysis revealed that the attacker had successfully drained roughly $293 million from Kelp. Further investigation by Cyvers indicated that the perpetrator utilized a wallet funded through Tornado Cash, a cryptocurrency mixer known for its privacy-preserving features that can also be exploited by malicious actors to obscure the origin of funds.
The attacker’s subsequent actions were equally swift. Cyvers reported that approximately $250 million of the stolen assets had already been converted into Ether (ETH), the native cryptocurrency of the Ethereum Layer-1 blockchain. This conversion to a more liquid and widely accepted cryptocurrency is a common tactic employed by hackers to facilitate the cashing out of stolen funds and make them harder to trace. The remaining funds are still being monitored for any further movement.
Wider Implications and Defensive Measures Across DeFi

The repercussions of the Kelp exploit were felt far beyond the protocol itself. The interconnected nature of DeFi means that a breach in one protocol can have cascading effects on others that rely on its services or hold its tokens. In response to the exploit, decentralized finance lending platform Aave took immediate action to safeguard its users. Aave announced the freezing of rsETH markets on both its Aave V3 and V4 versions. This measure prevents any further trading or interaction with rsETH on the Aave platform, effectively isolating the affected asset and mitigating potential contagion.
Cyvers further elaborated on the systemic risk, reporting that at least nine other crypto protocols had exposure to Kelp’s rsETH token. These protocols, recognizing the threat, also moved to freeze activity related to rsETH on their respective platforms. This coordinated defensive response underscores the tight-knit and interdependent nature of the DeFi ecosystem, where a single point of failure can necessitate rapid, broad-based action.
Deddy Lavid, CEO of Cyvers, commented on the broader implications of the incident for Cointelegraph, stating, "This is exactly the kind of incident that highlights the risks of composability in DeFi." Composability, a key feature of DeFi that allows different protocols to interact and build upon each other, also creates complex dependencies. When one component is compromised, it can potentially destabilize the entire structure. This incident serves as a stark reminder of the inherent risks associated with this interconnectedness, particularly when security measures are not robust enough to withstand sophisticated attacks.
A Persistent Trend of Exploits in the Crypto Space
The Kelp exploit is not an isolated event but rather the latest in a disturbing trend of escalating cybersecurity breaches and exploits targeting cryptocurrency platforms. Over the past several months, the industry has witnessed a significant increase in the value of stolen assets. Data compiled by various security firms indicates that crypto losses from hacks and scams totaled approximately $482 million in the first quarter of 2026 alone. This figure highlights the ongoing and escalating threat landscape faced by the digital asset industry.
Context: The Drift Protocol Incident
Adding further context to the current climate of insecurity, the decentralized cryptocurrency exchange Drift Protocol also suffered a substantial exploit in April. The Drift breach resulted in the loss of approximately $280 million. Investigations into the Drift Protocol attack revealed a meticulously planned operation. The Drift team disclosed that the attack required "months of deliberate preparation" and suggested that North Korean state-affiliated hackers may have been involved.
In a detailed post-mortem update, the Drift team outlined how they had met the attackers at a major crypto conference. They reportedly collaborated with these individuals for several months, a period during which the attackers are believed to have infiltrated the platform by deploying malware on developer machines, ultimately leading to the compromise of the protocol. This revelation points to a new level of sophistication and social engineering employed by malicious actors in the DeFi space.

The Underlying Risks of Composability and Interoperability
The Kelp incident, much like the Drift Protocol exploit, brings to the forefront the inherent risks associated with the composability and interoperability that define modern DeFi. While these features enable innovation and efficiency, they also create complex attack surfaces. The rsETH token, designed to be a liquid representation of staked assets, necessarily interacts with various bridges and protocols to maintain its liquidity and utility. This intricate web of connections, while beneficial for users, provides multiple potential vectors for attackers.
The reliance on cross-chain bridges, in particular, has become a focal point for security concerns. These bridges are essential for moving assets between different blockchains but are often complex and can be difficult to secure comprehensively. Vulnerabilities in bridge contracts or the underlying smart contracts of protocols interacting with these bridges can lead to catastrophic losses, as demonstrated by the Kelp exploit.
Future Outlook and Security Imperatives
The recurring nature of these high-value exploits raises critical questions about the current state of security within the DeFi sector. While protocols like Kelp and Drift are taking steps to investigate and mitigate the damage, the industry as a whole faces an ongoing challenge to bolster its defenses.
Key areas of focus for enhanced security include:
- Rigorous Smart Contract Audits: While standard practice, audits need to be more comprehensive and include deeper analysis of potential cross-contract interactions and emergent vulnerabilities.
- Advanced Threat Detection and Response: Protocols need to invest in sophisticated real-time monitoring systems capable of identifying anomalous behavior and triggering immediate alerts.
- Formal Verification: Employing formal verification techniques to mathematically prove the correctness of smart contracts can significantly reduce the risk of logical flaws.
- Decentralized Security Solutions: Exploring decentralized security networks and bug bounty programs can incentivize white-hat hackers to identify and report vulnerabilities proactively.
- Enhanced Bridge Security: Given their critical role and frequent exploitation, greater scrutiny and innovation in the security of cross-chain bridge infrastructure are paramount.
The Kelp attack, resulting in hundreds of millions of dollars in losses, serves as a potent reminder that the rapid innovation in DeFi must be matched by an equally robust commitment to security. As the ecosystem matures, addressing these vulnerabilities will be crucial for fostering trust and ensuring the long-term sustainability of decentralized finance. The industry’s ability to learn from these incidents and implement more resilient security frameworks will determine its trajectory in the face of increasingly sophisticated cyber threats.







