Microsoft Azure Monitor alerts are being deceptively weaponized by malicious actors to disseminate callback phishing emails, impersonating official warnings from the Microsoft Security Team regarding unauthorized account charges. This alarming trend exploits a legitimate cloud service to bypass standard security protocols, posing a significant threat to both individual users and potentially corporate networks. The sophisticated nature of these attacks, leveraging the trust associated with Microsoft’s infrastructure, underscores a growing challenge in cybersecurity defense.
Azure Monitor, a cornerstone of Microsoft’s cloud platform, is designed to provide comprehensive monitoring and analytics for Azure resources, applications, and infrastructure. Its capabilities include performance tracking, billing anomaly detection, issue identification, and the triggering of automated alerts based on predefined conditions. This functionality, intended to enhance operational efficiency and security, is now being perverted by threat actors to facilitate fraudulent activities.
Over the past month, a noticeable surge in user reports across various online forums and Microsoft’s own support channels has highlighted the prevalence of these deceptive alerts. Numerous individuals have come forward, detailing the reception of Azure Monitor notifications that falsely warn of suspicious charges or unusual invoice activity on their Microsoft accounts. These fabricated alerts invariably direct recipients to contact a provided phone number to "resolve" the purported issue, a classic callback phishing tactic.
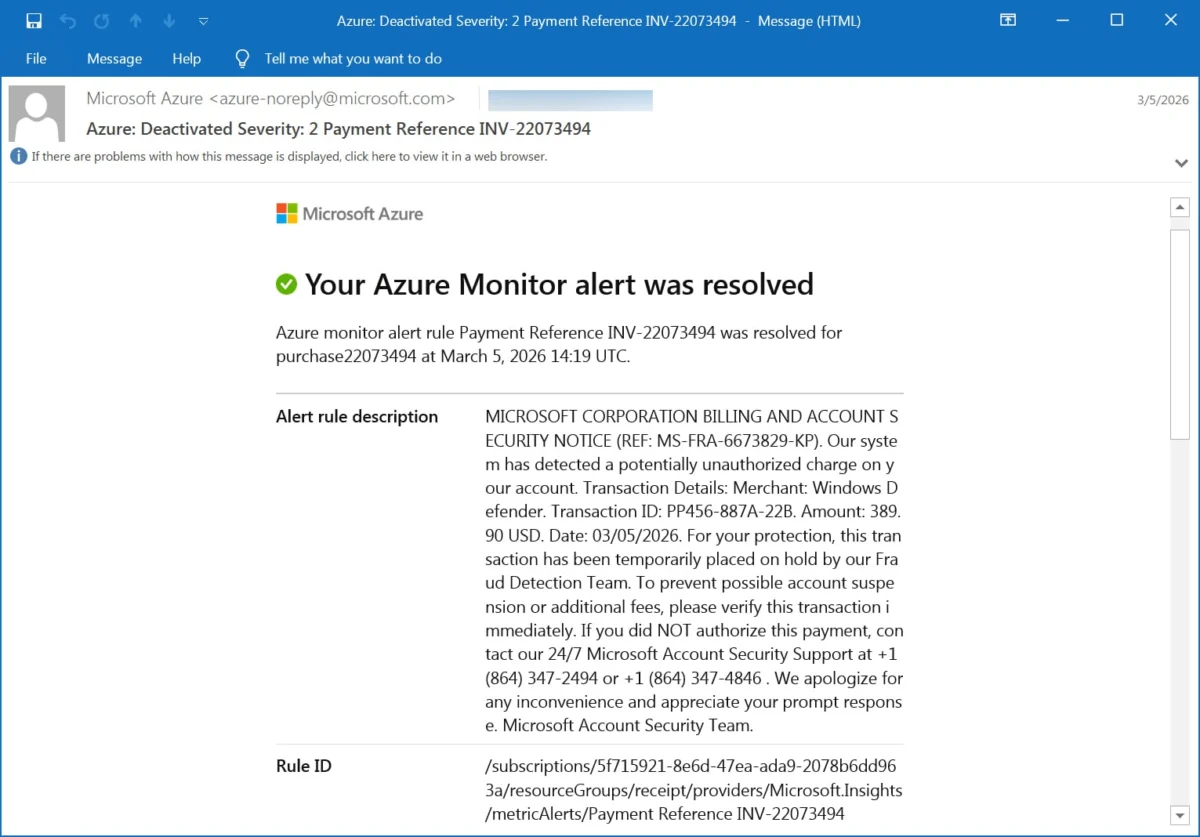
One such example of a deceptive alert reads: "Alert rule description MICROSOFT CORPORATION BILLING AND ACCOUNT SECURITY NOTICE (REF: MS-FRA-6673829-KP). Our system has detected a potentially unauthorized charge on your account. Transaction Details: Merchant: Windows Defender. Transaction ID: PP456-887A-22B. Amount: 389.90 USD. Date: 03/05/2026l." The message continues with a fabricated urgency, stating, "For your protection, this transaction has been temporarily placed on hold by our Fraud Detection Team. To prevent possible account suspension or additional fees, please verify this transaction immediately. If you did NOT authorize this payment, contact our 24/7 Microsoft Account Security Support at +1 (864) 347-2494 or +1 (864) 347-4846." The communiqué concludes with a disingenuous apology, "We apologize for any inconvenience and appreciate your prompt response. Microsoft Account Security Team."

Exploiting Trust Through Legitimate Channels
A critical aspect of this phishing campaign is its method of delivery. Unlike traditional phishing attacks that often rely on email spoofing, these malicious alerts are not forged. Instead, they are dispatched directly from the Microsoft Azure Monitor platform itself, utilizing the legitimate and authorized email address [email protected]. This fundamental difference in execution is what grants these messages a significant advantage in bypassing conventional security measures.
Because the emails originate from Microsoft’s own infrastructure, they successfully pass crucial email authentication protocols such as SPF (Sender Policy Framework), DKIM (DomainKeys Identified Mail), and DMARC (Domain-based Message Authentication, Reporting, and Conformance). These protocols are designed to verify the legitimacy of email senders and prevent unauthorized use of domain names. By passing these checks, the phishing emails appear highly authentic to both email servers and end-users, significantly reducing the likelihood of them being flagged as spam. The provided authentication results in sample emails confirm this:
Authentication-Results: relay.mimecast.com;
dkim=pass header.d=microsoft.com header.s=s1024-meo header.b=CKfQ8iOB;
arc=pass ("microsoft.com:s=arcselector10001:i=1");
dmarc=pass (policy=reject) header.from=microsoft.com;
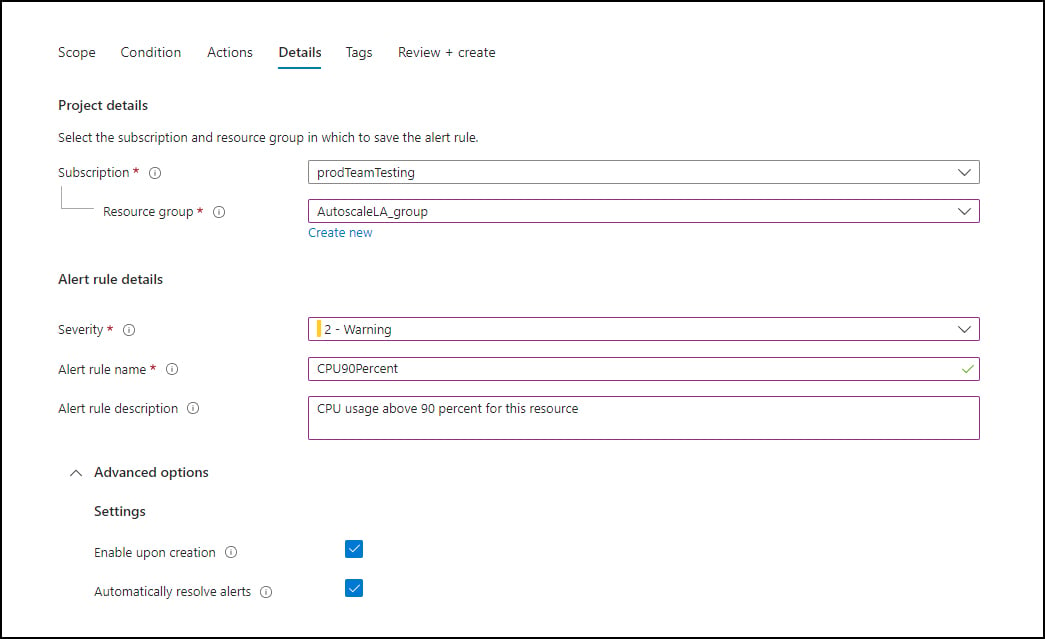
spf=pass (relay.mimecast.com: domain of [email protected] designates 40.107.200.103 as permitted sender) [email protected]This technical proficiency in exploiting Azure Monitor’s alerting system is a testament to the evolving tactics of cybercriminals. Threat actors are meticulously creating alert rules within Azure Monitor that are designed to be triggered by common and easily manipulated conditions. These conditions often include events related to new orders, payment processing, invoice generation, and other routine billing activities.
The exploit hinges on a feature within Azure Monitor that allows users to customize the "Alert rule description" field. Attackers are populating this field with their fabricated phishing messages, effectively embedding their malicious content within a seemingly legitimate system notification. When an alert is configured, it can be set to send an email notification. The attackers appear to be orchestrating this by creating these alerts and directing them to mailing lists under their control. These lists then act as intermediaries, forwarding the crafted alert emails to a broader, targeted audience. This multi-stage approach not only preserves the original Microsoft headers and authentication results but also adds a layer of indirection that can further obfuscate the source of the attack.
A Timeline of Escalation and Exploitation
While the exact origin date of this specific campaign remains unconfirmed, reports of suspicious Microsoft-themed billing alerts have been gradually increasing over the past few months. The surge in publicly reported incidents in the last month suggests a significant ramp-up in the scale and sophistication of the operation. Initial reports likely went unnoticed or were dismissed as isolated incidents, but the sheer volume of similar reports indicates a coordinated and expanding effort by threat actors.
The underlying technique of abusing monitoring services for phishing is not entirely new, but the specific application to Azure Monitor and the sophisticated methods employed represent a notable escalation. Previously, attackers might have focused on less robust systems or more easily spoofed email addresses. The current campaign demonstrates a deeper understanding of enterprise cloud infrastructure and a calculated effort to exploit its trusted communication channels.
BleepingComputer’s analysis has identified several categories of alerts being utilized in this campaign. The primary focus appears to be on invoice and payment-related alert rules, meticulously designed to mimic the automated billing notifications that businesses and individuals commonly receive from legitimate services. This mimicry is crucial for building a facade of authenticity.
The core psychological tactic employed in this campaign is the creation of a sense of urgency. The fabricated $389 Windows Defender charge, for instance, is a carefully chosen amount and a recognizable service to evoke immediate concern. Users, faced with an unexpected and potentially significant financial charge, are more likely to react impulsively without thoroughly scrutinizing the email’s authenticity. The instruction to "verify this transaction immediately" and the threat of "account suspension or additional fees" are designed to bypass rational decision-making processes.
While BleepingComputer did not directly engage with the provided phone numbers to avoid falling victim to the scam, historical data from similar callback phishing campaigns indicates severe consequences. These typically include credential theft, where victims are tricked into revealing their Microsoft account usernames and passwords, leading to account compromise. In other instances, victims may be defrauded of money directly or coerced into installing remote access software, granting attackers unfettered control over their devices.
Broader Implications for Cybersecurity
The implications of this Azure Monitor-based phishing campaign extend beyond individual user accounts. The use of an enterprise-grade cloud monitoring service, coupled with an "enterprise or corporate theme" in the fabricated alerts, suggests a potential strategic objective. Threat actors may be targeting these types of alerts to gain initial access to corporate networks. Once inside, they can conduct further reconnaissance, deploy ransomware, exfiltrate sensitive data, or launch more extensive cyberattacks. The ability to masquerade as a legitimate internal notification within a business environment makes this a particularly insidious threat to organizational security.
The success of this campaign highlights a critical vulnerability in the trust model of cloud services. While platforms like Azure Monitor offer powerful tools for legitimate users, their inherent functionalities can be subverted by those with malicious intent. This necessitates a multi-layered approach to security that goes beyond traditional email filtering and authentication checks.
Organizations and individuals alike are urged to exercise extreme caution when encountering any alert, particularly those related to billing or account security, that originates from Microsoft or any cloud service. Key indicators of potential phishing include:
- Unexpected or Urgent Requests: Be wary of alerts demanding immediate action regarding financial transactions or account status.
- Unsolicited Notifications: If you did not initiate a transaction or expect an invoice, treat the notification with suspicion.
- Requests for Sensitive Information: Legitimate security alerts typically do not ask for passwords, credit card numbers, or other highly sensitive personal information directly within the email or over the phone.
- Suspicious Phone Numbers: While the provided numbers in this campaign appear to be standard US phone numbers, always verify contact information through official Microsoft channels rather than relying solely on the alert.
Official Response and Future Safeguards
As of the reporting of this incident, Microsoft has not issued a broad public statement specifically addressing this Azure Monitor phishing campaign. However, the company has a long-standing commitment to combating phishing and other cyber threats. It is highly probable that Microsoft’s security teams are actively investigating this exploitation and working to implement countermeasures.
Potential mitigation strategies from Microsoft could include:
- Enhanced Monitoring of Alert Creation: Implementing stricter controls or anomaly detection for alert rule descriptions that contain suspicious keywords or patterns indicative of phishing.
- User Education Initiatives: Reinforcing user awareness campaigns about recognizing sophisticated phishing tactics, especially those leveraging legitimate services.
- Refined Alerting Mechanisms: Potentially introducing additional verification steps or alternative communication channels for critical billing-related alerts.
- Platform-Level Defenses: Exploring ways to identify and block the misuse of alert descriptions for malicious purposes, possibly through AI-driven content analysis.
In the interim, end-users and IT professionals are advised to remain vigilant. A critical step for organizations is to educate their employees about this specific threat and to reinforce existing security policies. Regularly reviewing Azure activity logs and monitoring for unusual alert configurations can also provide early warning signs of such abuse. The ongoing evolution of cyber threats requires a continuous adaptation of security strategies, emphasizing both technological defenses and robust user awareness programs. The weaponization of Azure Monitor alerts serves as a stark reminder that even the most trusted technological tools can become vectors for malicious attacks when exploited by determined adversaries.







