
A sophisticated new information-stealing malware, dubbed VoidStealer, has emerged with a groundbreaking technique to bypass Google Chrome’s Application-Bound Encryption (ABE) and pilfer the critical master key used to decrypt sensitive user data stored within the browser. This novel approach, detailed in a recent report by Gen Digital, represents the first observed instance of an information stealer in the wild employing hardware breakpoints to extract the v20_master_key directly from the browser’s memory. Crucially, this bypass operates without necessitating privilege escalation or intrusive code injection, presenting a significant challenge to Chrome’s established security architecture.
The implications of this exploit are substantial, potentially exposing a vast trove of user credentials, financial information, and other sensitive data that users entrust to their web browsers. As VoidStealer operates as a Malware-as-a-Service (MaaS) platform, this bypass method could be rapidly disseminated among a wide array of threat actors, amplifying the risk to internet users globally.

The Genesis of Application-Bound Encryption and Its Vulnerability
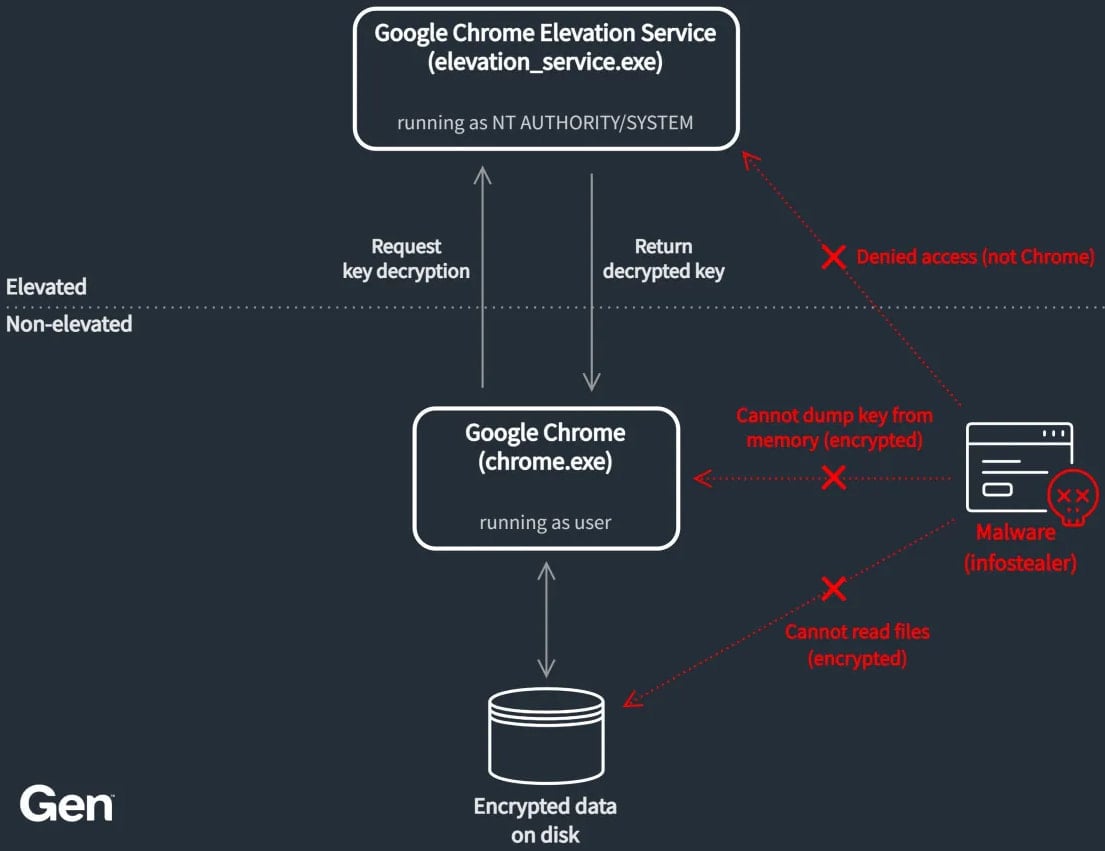
Google introduced Application-Bound Encryption (ABE) in Chrome version 127, released in June 2024, as a proactive measure to bolster the security of cookies and other sensitive browser data. The core principle behind ABE is to ensure that the master key, essential for decrypting this stored information, remains encrypted on disk. Accessing this key under normal user-level operations is designed to be impossible, with decryption requiring validation from the Google Chrome Elevation Service, a process that operates with SYSTEM privileges. This architecture aimed to create a robust defense against information-stealing malware that typically operates within the user’s permission scope.
However, the landscape of cybersecurity is a perpetual arms race, and the effectiveness of ABE was quickly challenged. Even before VoidStealer’s novel approach, multiple information-stealing malware families and publicly available open-source tools demonstrated the ability to bypass ABE. Google has since responded with fixes and enhancements to patch these identified vulnerabilities. Despite these efforts, new malware variants have reportedly continued to surface, employing alternative methods to circumvent the intended security protections. This ongoing cat-and-mouse game highlights the persistent threat posed by advanced malware development and the challenges in maintaining a completely impenetrable digital fortress.
VoidStealer’s Innovative Bypass Mechanism: A Deep Dive
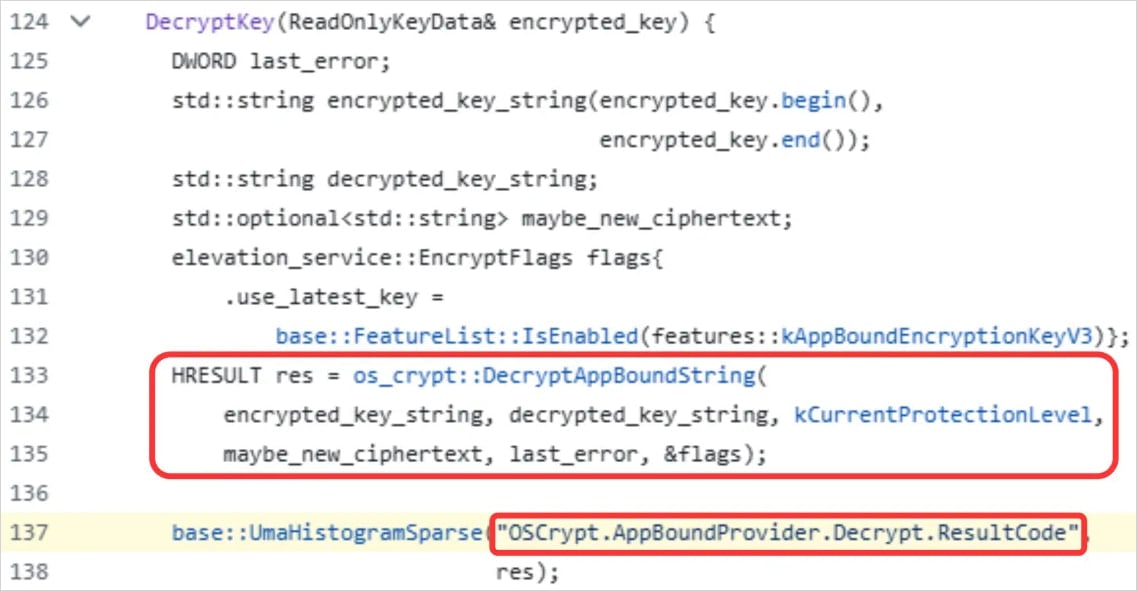
The breakthrough by VoidStealer, as detailed by threat researcher Vojtěch Krejsa from Gen Digital, lies in its exploitation of a fleeting moment when the v20_master_key resides in plaintext within Chrome’s memory. This occurs during decryption operations, a critical juncture that the malware expertly targets.
VoidStealer’s methodology involves several precise steps:
- Stealthy Process Initialization: The malware initiates a suspended and hidden instance of the Chrome browser process. This clandestine start-up ensures that the malicious activity is not readily apparent to the user or standard security monitoring tools.
- Debugger Attachment: The VoidStealer malware then attaches itself to this suspended process as a debugger. This allows it to gain a deep level of control and visibility into the target process’s execution.
- Targeting the Browser DLL: The next phase involves waiting for the core browser DLLs, such as
chrome.dllormsedge.dll, to load into the memory space of the attached process. These DLLs contain the critical code responsible for Chrome’s functionality, including its encryption and decryption routines. - Hardware Breakpoint Setup: Once the target DLL is loaded, VoidStealer scans it for a specific, recognizable string associated with the master key handling. Crucially, it identifies the address of the
LEA(Load Effective Address) instruction that references this string. This address is then designated as the target for a hardware breakpoint. Hardware breakpoints are a powerful debugging feature that allows a debugger to pause execution when a specific memory address is accessed or written to, offering a more precise and less intrusive method than software breakpoints. - Breakpoint Deployment and Triggering: VoidStealer strategically deploys this hardware breakpoint across all existing and newly created threads within the browser process. It then allows the process to resume execution, effectively waiting for the breakpoint to trigger. This trigger is designed to occur during the browser’s startup sequence, precisely when it is actively decrypting protected data, including the master key.
- Master Key Extraction: Upon the breakpoint being triggered, the execution pauses. At this critical juncture, the malware reads the CPU register that holds a pointer to the plaintext
v20_master_key. Using theReadProcessMemoryAPI call, VoidStealer extracts this sensitive key directly from the browser’s memory before the operating system or Chrome can remove it or re-encrypt it.
Gen Digital’s analysis further suggests that the most opportune moment for this exploit is during the browser’s initial startup. This is when Chrome typically loads ABE-protected cookies early in the session, compelling the immediate decryption of the master key to access this data.
Tracing the Origins: An Open-Source Pedigree
Interestingly, researchers believe that VoidStealer did not independently invent this sophisticated debugger-based bypass. Instead, the technique appears to have been adapted from an open-source project known as "ElevationKatz." ElevationKatz is part of the broader ChromeKatz toolset, a collection of utilities designed to demonstrate weaknesses in Chrome’s cookie-handling mechanisms and facilitate cookie dumping. This toolset has been publicly available for over a year, providing a potential blueprint for threat actors seeking to exploit Chrome’s security features.
.webp)
While there are discernible differences in the specific code implementation, the fundamental approach aligns closely with ElevationKatz, indicating a clear lineage of the bypass technique. This reliance on publicly available exploits underscores a growing trend where advanced malicious techniques are disseminated and repurposed by various threat actors, accelerating the evolution of cyber threats.
VoidStealer: A Growing Malware-as-a-Service Threat
VoidStealer itself is not a new entrant to the cybercrime landscape. It has been advertised and operated as a Malware-as-a-Service (MaaS) platform on dark web forums since at least mid-December 2025. The introduction of the ABE bypass mechanism in its version 2.0 marks a significant escalation in its capabilities and appeal to a broader criminal audience. MaaS models lower the barrier to entry for less technically skilled cybercriminals, allowing them to rent sophisticated malware tools and conduct their own attacks, thereby multiplying the potential number of threat actors.
The advertising of this specific bypass by cybercriminals, as evidenced by screenshots shared by Gen Digital, demonstrates a deliberate effort to highlight its effectiveness and attract customers by promising access to compromised browser data that was previously considered secure.
Broader Implications and Future Concerns
The successful exploitation of Chrome’s ABE by VoidStealer, and previously by other malware families, raises critical questions about the long-term effectiveness of such layered security approaches. While ABE was a significant step forward, its vulnerability highlights the constant need for vigilance and continuous improvement in browser security.
- Erosion of Trust: The ability of malware to bypass robust encryption mechanisms can erode user trust in browser security. Users may become increasingly apprehensive about storing sensitive information online if they perceive that even advanced protections can be circumvented.
- Amplified Data Breach Risks: A compromised master key grants attackers unfettered access to a wealth of sensitive data, including login credentials for banking sites, social media platforms, email accounts, and other online services. This can lead to identity theft, financial fraud, and reputational damage.
- The Arms Race Continues: This incident reinforces the ongoing arms race between cybersecurity defenders and attackers. As defenders implement new security measures, attackers invariably seek out and exploit novel vulnerabilities. The rapid adaptation of techniques like the debugger bypass by VoidStealer emphasizes the need for proactive threat hunting and swift patch deployment.
- Potential for Wider Impact: Given that VoidStealer is a MaaS platform, the widespread availability of this bypass could lead to a surge in credential theft attacks. This could impact not only individual users but also organizations that rely on employees accessing corporate resources via browsers.
While BleepingComputer reached out to Google for comment on this specific bypass method being utilized by threat actors, a response was not available at the time of publication. The company’s ongoing efforts to address such vulnerabilities will be closely watched by the cybersecurity community. The incident serves as a stark reminder that even well-intentioned security features require continuous scrutiny and adaptation in the face of evolving cyber threats. The battle to secure browser data remains a dynamic and challenging endeavor, requiring sustained innovation from both developers and security researchers.







