
Microsoft has issued the Windows 10 KB5082200 cumulative update, a crucial release that addresses a significant number of security vulnerabilities identified in the April 2026 Patch Tuesday cycle. This update is particularly noteworthy for patching two zero-day exploits, which are flaws that have been actively exploited by malicious actors before a fix was available. The update also introduces enhancements to Remote Desktop Protocol security and provides new visibility into the Secure Boot certificate rollout.
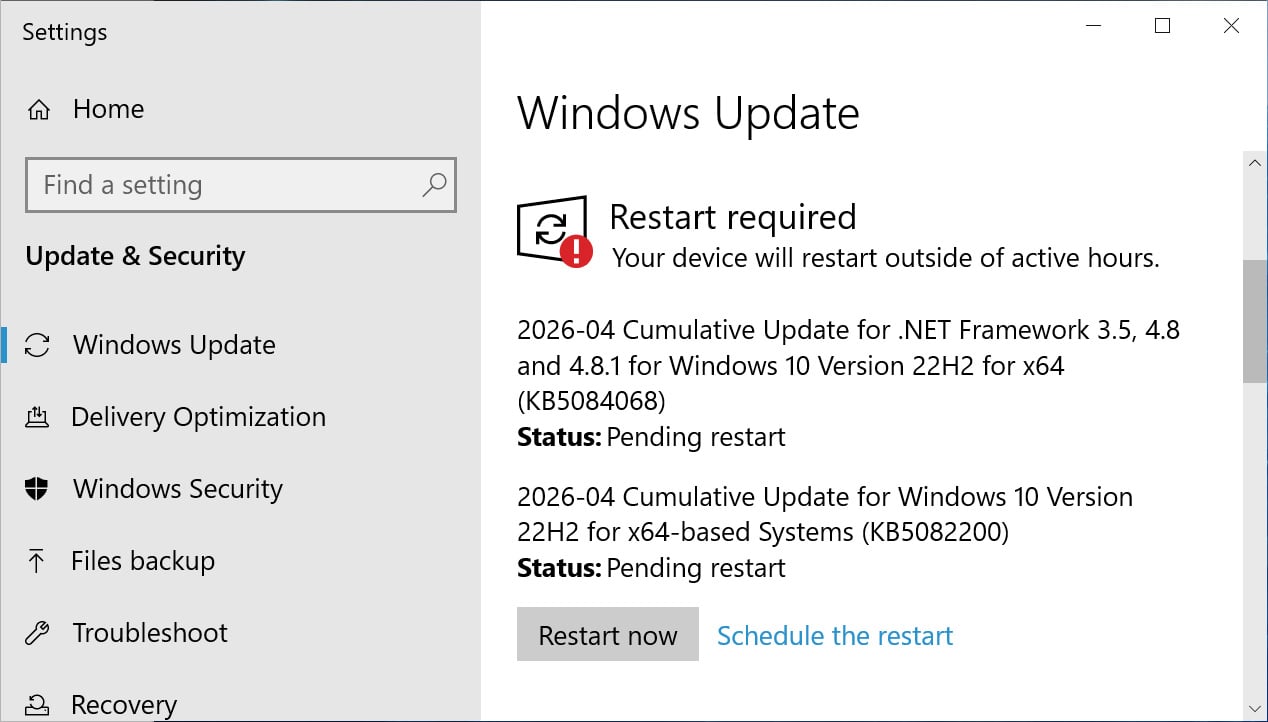
The KB5082200 update is available to users running Windows 10 Enterprise LTSC and those enrolled in the Extended Security Updates (ESU) program. Installation is a standard procedure, accessible through the Windows Update interface within the operating system’s settings. Users can initiate the update by navigating to Settings, selecting Windows Update, and then clicking "Check for Updates."
Following the installation of KB5082200, Windows 10 systems will be updated to build 19045.7184. For users of Windows 10 Enterprise LTSC 2021, the build number will be updated to 19044.7184. This cumulative update is primarily focused on security enhancements and bug fixes, as Microsoft has ceased the development of new features for the Windows 10 operating system. The company’s strategic focus has shifted towards its newer operating systems, particularly Windows 11.
April 2026 Patch Tuesday: A Deep Dive into the Vulnerabilities Addressed
The April 2026 Patch Tuesday, which this KB5082200 update rectifies, saw Microsoft addressing a substantial total of 167 vulnerabilities. This figure underscores the ongoing threat landscape and Microsoft’s commitment to patching critical flaws. The inclusion of two zero-day vulnerabilities highlights the immediate nature of some security threats, where attackers may have already begun exploiting these weaknesses in the wild. While the specific details of these zero-days are not always immediately disclosed by Microsoft to prevent further exploitation, their inclusion in this update signals a critical need for prompt patching by affected users.
The comprehensive list of fixes released with this update aims to fortify Windows 10 against a wide array of potential attacks, ranging from privilege escalation to remote code execution and denial-of-service vulnerabilities. These patches are the culmination of Microsoft’s security research and external vulnerability disclosures, a process that often involves collaboration with cybersecurity researchers and the broader security community.

Key Enhancements in KB5082200
Beyond the core security patches, KB5082200 introduces several notable enhancements designed to bolster the security posture of Windows 10 environments.
Advanced Remote Desktop Protocol (RDP) File Phishing Protections
One of the significant new features is the introduction of enhanced protections against file phishing within the Remote Desktop Protocol. RDP is a widely used tool for remote access to Windows machines, making it a prime target for attackers. Phishing attacks that leverage RDP can trick users into downloading malicious files or providing credentials that grant unauthorized access to systems. These new protections are expected to add an extra layer of defense, potentially by scrutinizing file transfers or warning users about suspicious file types when using RDP. This proactive measure aims to mitigate the risks associated with social engineering tactics that often accompany RDP-based attacks.
New Windows Security Indicators for Secure Boot Certificate Rollout
Microsoft is actively managing the lifecycle of its security infrastructure, including the Secure Boot certificates. These certificates are fundamental to the secure boot process, ensuring that only trusted software is loaded during system startup. Older Secure Boot certificates, dating back to 2011, are nearing their expiration in June 2026. To ensure a smooth transition and maintain system integrity, Microsoft has been orchestrating the rollout of new certificates.
With the KB5082200 update, users will now find new indicators within Windows Security that provide a clear status update on the rollout of these crucial Secure Boot certificates. This transparency allows administrators and users to monitor the progress of this important infrastructure update and identify any potential issues that might arise during the transition. The ability to check the status directly within the familiar Windows Security interface simplifies the management of this critical security component. This initiative is part of a broader industry effort to ensure that the foundational security mechanisms of modern operating systems remain robust and up-to-date.
Addressing a Long-Standing BitLocker Recovery Issue
The KB5082200 update also resolves a persistent bug that has troubled some Intel-based devices. Previously, certain Intel-based systems supporting Connected Standby could unexpectedly enter the BitLocker recovery screen after a restart. BitLocker is a full-disk encryption feature designed to protect data at rest. However, encountering the recovery screen without a valid reason can be disruptive and frustrating for users, potentially leading to data inaccessibility if recovery keys are not readily available. This fix, stemming from a longstanding issue that was also addressed in previous cumulative updates, demonstrates Microsoft’s ongoing commitment to refining the stability and user experience of Windows 10, even as it enters its later stages of support.

The Evolving Landscape of Windows 10 Support
The release of KB5082200 is particularly significant given that Windows 10 is approaching its official end-of-support date, which is October 14, 2025. After this date, Microsoft will no longer provide regular security updates, feature updates, or technical support for Windows 10. However, the company has introduced the Extended Security Updates (ESU) program, allowing businesses and organizations to continue receiving critical security patches for a limited period beyond the end-of-support date, for a fee. The KB5082200 update, released in April 2026, clearly indicates that Microsoft is still providing security updates for Windows 10, at least for those enrolled in the ESU program or using specific Long-Term Servicing Channel (LTSC) versions. This extended patching schedule is vital for organizations that may require more time to migrate to newer operating systems.
The ESU program is designed to provide a safety net for organizations that cannot immediately upgrade their infrastructure. This can be due to the complexity of their IT environments, the cost of new hardware, or the need for extensive software compatibility testing. By offering extended security updates, Microsoft aims to reduce the risk of cyberattacks on these legacy systems, which could otherwise become vulnerable once regular security support ceases. The inclusion of zero-day fixes in this later update underscores the continued importance of these extended security measures.
Chronology of Windows 10 Security Updates and Support
- July 2015: Windows 10 is officially launched.
- October 14, 2025: Official end of support for Windows 10.
- Post-October 14, 2025: Extended Security Updates (ESU) program becomes available for eligible customers.
- April 2026: Release of KB5082200, a cumulative update for Windows 10, demonstrating continued security patching for ESU participants and LTSC versions, including fixes for zero-day vulnerabilities and other critical flaws.
This timeline highlights the phased approach to Windows 10’s lifecycle, with a strong emphasis on security even as the operating system reaches its twilight years. The availability of updates like KB5082200 well into 2026 for specific user groups is a testament to the ongoing threat landscape and the need for continuous security vigilance.
Broader Impact and Implications
The release of KB5082200 carries significant implications for Windows 10 users, particularly those operating in enterprise environments. The patching of zero-day vulnerabilities is paramount, as these exploits represent the most immediate and severe threats. By addressing these flaws, Microsoft is actively working to close critical security gaps that could have been exploited to compromise sensitive data or disrupt operations.
The enhanced RDP file phishing protections are a proactive measure against evolving social engineering tactics. As remote work continues to be prevalent, RDP remains a critical tool for many organizations. Strengthening its security against phishing attempts is a vital step in safeguarding remote access infrastructure.
Furthermore, the visibility into the Secure Boot certificate rollout empowers IT administrators. The ability to monitor and manage this critical security component ensures that systems remain protected by robust boot-time security measures, preventing unauthorized software from loading at startup. This is especially important as older certificates expire, necessitating a seamless transition to newer, more secure cryptographic standards.
For organizations still reliant on Windows 10, especially those utilizing the ESU program, staying current with these cumulative updates is not merely a recommendation but a critical imperative. The continued provision of security patches, including those for zero-day threats, by Microsoft underscores the enduring risks associated with running unsupported or outdated software. The KB5082200 update serves as a timely reminder of the dynamic nature of cybersecurity and the ongoing need for robust defense mechanisms.
Microsoft has indicated that there are no known issues associated with this particular update, which is a positive sign for a smooth deployment. However, as with any significant system update, it is always advisable for organizations to conduct thorough testing in a controlled environment before widespread deployment to ensure compatibility with their specific applications and hardware configurations. This due diligence can help prevent unforeseen disruptions and ensure that the security benefits of the update are realized without compromising operational stability. The commitment to patching such critical vulnerabilities, even for an operating system nearing its end of support, reflects Microsoft’s broader strategy of maintaining a secure computing ecosystem for its users.







