
The Payouts King ransomware, a sophisticated cyber threat believed to be linked to former BlackBasta affiliates, has adopted a new and alarming tactic: the covert deployment of QEMU (Quick EMUlator) virtual machines. This innovative approach allows the ransomware to operate hidden within compromised systems, creating a powerful reverse SSH backdoor to bypass stringent endpoint security solutions and conduct its malicious operations undetected. Researchers at cybersecurity firm Sophos have meticulously documented two distinct campaigns showcasing this evolving methodology, shedding light on the growing sophistication of modern ransomware attacks.
The QEMU emulator, a well-established open-source tool for system emulation and virtualization, typically serves legitimate purposes, enabling users to run different operating systems as virtual machines (VMs) on a host computer. However, its inherent capability to create isolated environments has made it an attractive, albeit illicit, tool for cybercriminals. The core of its appeal for attackers lies in the fact that standard endpoint security solutions, designed to monitor the host operating system, often lack the visibility to inspect the internal workings of these virtual machines. This creates a blind spot, allowing attackers to execute their payloads, securely store malicious files, and establish covert remote access tunnels, often over SSH, without triggering immediate alerts.
This is not the first instance of QEMU being weaponized by threat actors. Its ability to mask malicious activity has led to its abuse in previous campaigns by various malicious groups. Notably, the 3AM ransomware group has been observed employing QEMU to breach networks, the LoudMiner cryptomining operation has utilized it to attack Windows and macOS systems, and the "CRON#TRAP" phishing campaigns have also exploited its stealth capabilities. The latest findings from Sophos indicate that Payouts King is now joining this list of sophisticated adversaries.
Sophos’s analysis identified two primary campaigns where QEMU played a pivotal role in the Payouts King operations. The first campaign, designated STAC4713, was initially observed in November 2025 and is directly linked to the Payouts King ransomware activity. The second, STAC3725, emerged in February of this year and specifically targets NetScaler ADC and Gateway instances by exploiting the critical CitrixBleed 2 vulnerability (CVE-2025-5777).

The Mechanics of Stealth: QEMU-Powered Alpine Linux VMs
The STAC4713 campaign, in particular, has been attributed by Sophos to the GOLD ENCOUNTER threat group, an entity known for its focus on hypervisors and its expertise in encrypting VMware and ESXi environments. This campaign demonstrates a highly organized and deliberate approach to infiltration and data exfiltration.
According to Sophos’s detailed report, the attackers initiate their malicious sequence by establishing a scheduled task on the compromised system. This task, ominously named "TPMProfiler," is designed to launch a hidden QEMU virtual machine operating with SYSTEM privileges. This strategic choice ensures the VM runs with the highest level of access, granting it broad control over the host system.
To further disguise their activities, the attackers employ virtual disk files that are deliberately made to resemble legitimate database or DLL files, making them less likely to arouse suspicion. The attackers then configure port forwarding to establish a covert channel for remote access. This is achieved through a reverse SSH tunnel, effectively creating a secure, encrypted link back to their command-and-control infrastructure.
The virtual machine itself is configured to run Alpine Linux, a lightweight and minimalist Linux distribution. Specifically, version 3.22.0 of Alpine Linux was observed. This choice of operating system is strategic, as its small footprint requires fewer resources and can be less resource-intensive, potentially reducing the chances of detection due to unusual system load. Crucially, this Alpine Linux environment is pre-loaded with a suite of sophisticated attacker tools, including AdaptixC2 (a command-and-control framework), Chisel (a high-performance TCP/UDP tunnel), BusyBox (a utility suite for embedded systems), and Rclone (a command-line program to manage files on cloud storage).
Sophos has detailed that initial access for the STAC4713 campaign was frequently achieved through exposed SonicWall VPNs, a common entry point for many threat actors. However, more recent iterations of attacks attributed to this group have also leveraged the exploitation of the SolarWinds Web Help Desk vulnerability, specifically CVE-2025-26399, indicating an adaptive approach to exploiting known security weaknesses.

In the post-infection phase, the attackers employ a multi-pronged strategy for data acquisition and exfiltration. They utilize Volume Shadow Service (VSS) utilities, specifically referencing "vssuirun.exe," to create shadow copies of the system’s data. This allows them to bypass file locks and access data that might otherwise be in use. Subsequently, they use the SMB protocol and the print command to copy critical system hives, including NTDS.dit (Active Directory database), SAM (Security Accounts Manager), and SYSTEM hives, to temporary directories. These hives contain invaluable credential information that can be further exploited for lateral movement and privilege escalation.
More recent observed incidents attributed to the GOLD ENCOUNTER threat actor reveal a continued evolution in their initial access methods. Sophos researchers noted an attack in February where the group exploited an exposed Cisco SSL VPN. In another instance in March, they impersonated IT staff, using Microsoft Teams to trick employees into downloading and installing QuickAssist, a legitimate remote support tool, which was then abused to deliver malicious payloads.
In both these latter cases, Sophos observed the threat actors leveraging the legitimate ADNotificationManager.exe binary. This binary was used to sideload a Havoc C2 payload disguised as a DLL file (vcruntime140_1.dll). Following this, Rclone was employed to exfiltrate the harvested data to a remote SFTP (SSH File Transfer Protocol) location, further emphasizing the use of covert channels.
Payouts King’s Suspected Lineage and Operational Modus Operandi
The recent Zscaler report provides crucial context regarding the identity and operational methods of the Payouts King ransomware. The report suggests a strong likelihood that Payouts King is connected to former affiliates of the BlackBasta ransomware group. This association is primarily drawn from the adoption of similar initial access techniques. These include:
- Spam Bombing: Overwhelming targets with a deluge of malicious emails to increase the chances of a successful infection.
- Microsoft Teams Phishing: Exploiting the trust and widespread use of Microsoft Teams to deliver malicious links or files disguised as legitimate communications.
- Quick Assist Abuse: As mentioned previously, leveraging the legitimate Quick Assist remote support tool to gain unauthorized access and deploy malware.
The Payouts King strain itself is characterized by its robust obfuscation techniques and anti-analysis mechanisms, designed to thwart security researchers and automated detection systems. It establishes persistence within compromised networks by creating scheduled tasks, a common but effective method. Furthermore, it actively seeks to disable or terminate security tools by utilizing low-level system calls, a technique that requires deep knowledge of operating system internals.

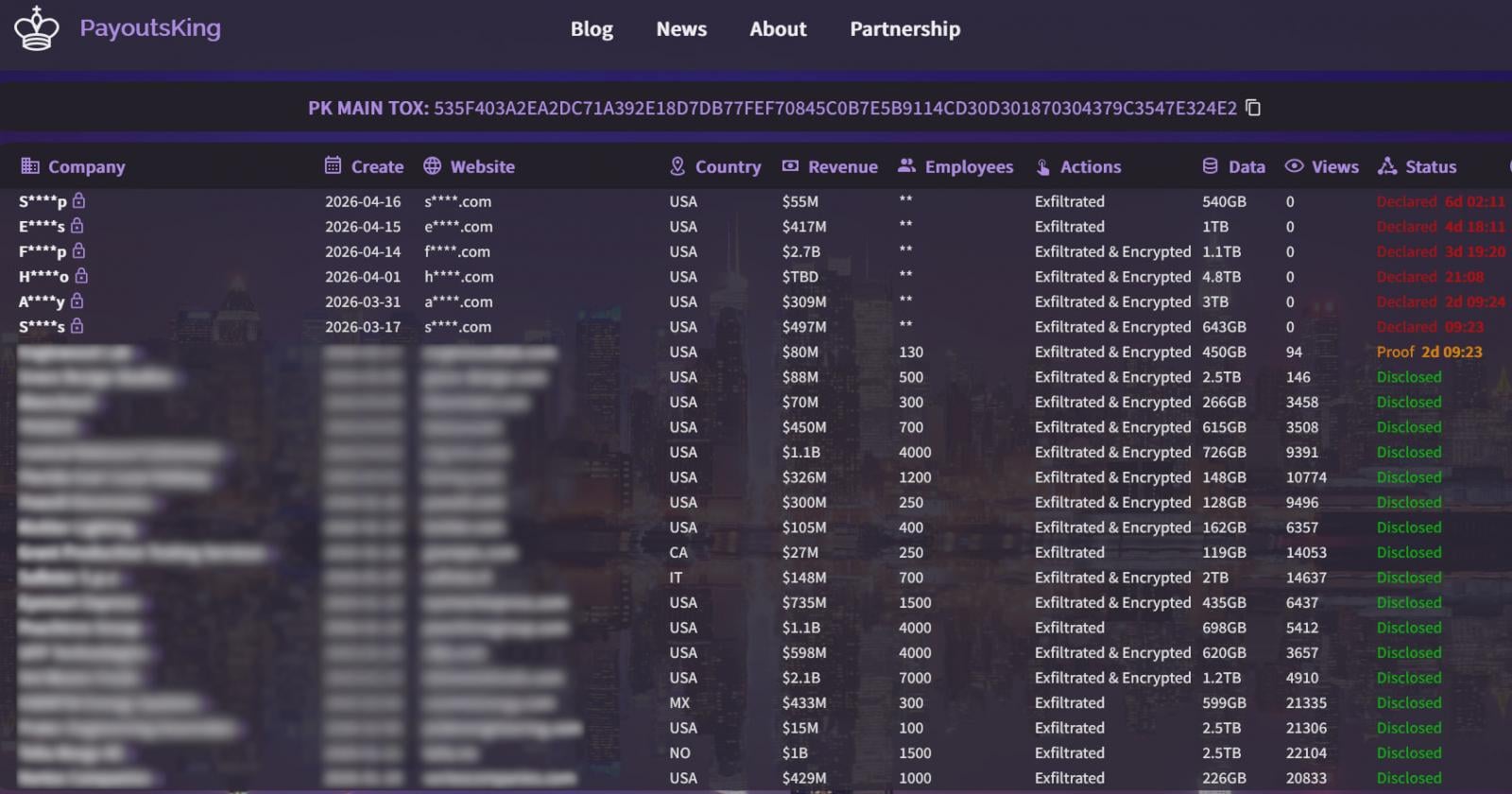
The encryption scheme employed by Payouts King is a potent combination of AES-256 in Counter (CTR) mode for data encryption, secured by RSA-4096 encryption for the symmetric keys. The use of intermittent encryption for larger files is a tactic to reduce the time and resources required for the encryption process, allowing attackers to complete their attack more rapidly. Upon successful encryption, victims are presented with ransom notes that direct them to dedicated leak sites on the dark web, where their stolen data is threatened with public release if the ransom is not paid.
The CitrixBleed 2 Exploitation and Secondary Campaign
The second campaign documented by Sophos, STAC3725, which has been active since February, highlights a different, yet equally concerning, vector of attack. This campaign capitalizes on the severe CitrixBleed 2 vulnerability (CVE-2025-5777) to gain initial access to target environments. This vulnerability affects NetScaler ADC and Gateway instances, critical components for secure remote access in many organizations.
Upon compromising NetScaler devices, the attackers deploy a ZIP archive containing a malicious executable. This executable performs several critical actions:
- Service Installation: It installs a service named "AppMgmt," which runs in the background and facilitates persistent access.
- User Creation: A new local administrator user account, "CtxAppVCOMService," is created, providing a backdoor for future access.
- ScreenConnect Installation: A ScreenConnect client is installed, a legitimate remote access tool that is weaponized by the attackers to establish a persistent connection.
The ScreenConnect client then connects to a remote relay server controlled by the attackers. From this relay, they establish a session with system privileges on the compromised host. Following this, they deploy and extract a QEMU package. This package is configured to run a hidden Alpine Linux VM using a custom disk image file named "custom.qcow2."
A key distinction in this campaign is the attackers’ approach to populating the virtual machine with tools. Instead of relying on pre-built toolkits, the threat actors in STAC3725 manually install and compile their arsenal within the VM. This meticulous approach suggests a desire for greater control and customization of their attack tools. The observed tools include a comprehensive suite for network reconnaissance and exploitation, such as Impacket (a collection of Python classes for working with network protocols), KrbRelayx (a tool for relaying Kerberos authentication), Coercer (a tool for forcing authentication), BloodHound.py (a tool for analyzing Active Directory), NetExec (a remote execution tool), Kerbrute (a Kerberos enumeration tool), and Metasploit (a penetration testing framework).
The observed activities in this campaign are extensive and focus on deep network compromise. This includes sophisticated credential harvesting, enumeration of Kerberos usernames, thorough Active Directory reconnaissance to map the network and identify valuable targets, and the staging of data for exfiltration via FTP servers.
Defensive Recommendations and Broader Implications
In light of these evolving threats, Sophos has provided critical recommendations for organizations to bolster their defenses. They advise looking for several key indicators of compromise:
- Unauthorized QEMU Installations: The presence of QEMU on systems where it is not expected or authorized can be a strong indicator of malicious activity.
- Suspicious Scheduled Tasks: Scheduled tasks running with SYSTEM privileges, especially those with unusual names or executing unfamiliar binaries, warrant immediate investigation.
- Unusual SSH Port Forwarding: The configuration of port forwarding, particularly for covert access, can be a sign of unauthorized remote access.
- Outbound SSH Tunnels on Non-Standard Ports: Legitimate SSH traffic typically uses standard ports. Outbound SSH connections on unusual ports can indicate an attempt to evade detection.
The implications of Payouts King’s adoption of QEMU-based tactics are far-reaching. It signifies a growing trend of ransomware groups leveraging virtualization and emulation technologies to evade established security controls. This forces security vendors and organizations to re-evaluate their detection strategies and invest in more advanced endpoint detection and response (EDR) capabilities that can inspect virtualized environments. The ability of attackers to hide their operations within isolated VMs presents a significant challenge to incident responders, making detection, containment, and eradication more complex and time-consuming.
The linkage to former BlackBasta affiliates suggests a continuity of high-level operational capabilities and a willingness to adapt to new defensive measures. Organizations that were previously targeted by BlackBasta should be particularly vigilant. The ongoing exploitation of known vulnerabilities like CitrixBleed 2 also underscores the persistent importance of robust vulnerability management and timely patching.
As cyber threats continue to evolve, the Payouts King ransomware’s use of QEMU serves as a stark reminder of the constant cat-and-mouse game between attackers and defenders. The future of ransomware defense will undoubtedly require deeper insights into virtualization technologies and a more proactive approach to threat intelligence and detection.







