
The open-source reactive Python notebook platform Marimo is facing a significant security crisis after a critical vulnerability was exploited by malicious actors a mere ten hours after its public disclosure. This rapid exploitation highlights a concerning trend in the cybersecurity landscape, where sophisticated threat actors can quickly weaponize newly revealed flaws, posing an immediate threat to organizations relying on vulnerable software. The vulnerability, officially designated as CVE-2026-39987, allows for unauthenticated remote code execution and has been rated with a critical severity score of 9.3 out of 10 by GitHub, underscoring the severity of the potential impact.
Background: The Rise of Reactive Notebooks and Marimo’s Role
In recent years, data science, machine learning, and artificial intelligence development has seen a surge in the adoption of interactive notebook environments. Platforms like Jupyter Notebooks have become ubiquitous, offering a flexible way to write and execute code, visualize data, and document findings. Marimo emerged as a modern alternative, aiming to enhance this experience by providing a reactive programming model. This means that changes in one part of the notebook automatically propagate to other connected parts, streamlining the development of data applications, dashboards, and interactive visualizations. Its popularity is evidenced by its substantial community support, boasting approximately 20,000 stars and 1,000 forks on GitHub, indicating a broad user base across research, academic, and industry sectors. This widespread adoption, however, also translates to a larger attack surface when vulnerabilities are discovered.
The Nature of CVE-2026-39987

The critical flaw, CVE-2026-39987, stems from an unauthenticated WebSocket endpoint within Marimo, specifically identified as "/terminal/ws". This endpoint was designed to provide interactive terminal access, a powerful feature for debugging and system interaction. However, it lacked adequate authentication and authorization checks, effectively allowing any unauthenticated client to establish a connection. This oversight grants attackers direct access to a full interactive shell, operating with the same privileges as the Marimo process itself. Such a level of access is highly coveted by attackers, as it can be leveraged for a wide range of malicious activities, from data exfiltration to the deployment of further malicious payloads.
Chronology of Discovery and Exploitation
The timeline of events surrounding CVE-2026-39987 is a stark illustration of the speed at which vulnerabilities can be weaponized.
- April 8, 2026: Marimo officially discloses the critical vulnerability in their platform. This disclosure, typically made through security advisories, provides detailed information about the flaw and its potential impact.
- Within 10 Hours of Disclosure: Researchers at Sysdig, a prominent cloud-security company, observed the first exploitation attempts in the wild. This rapid turnaround suggests that attackers were actively monitoring security feeds and were able to quickly develop and deploy an exploit based on the publicly available information in the developer’s advisory.
- First Exploitation Session: The initial attack involved a highly targeted approach. The attacker first validated the vulnerability by connecting to the "/terminal/ws" endpoint and executing a brief scripted sequence to confirm remote command execution. This validation phase was remarkably short, lasting mere seconds before the connection was terminated.
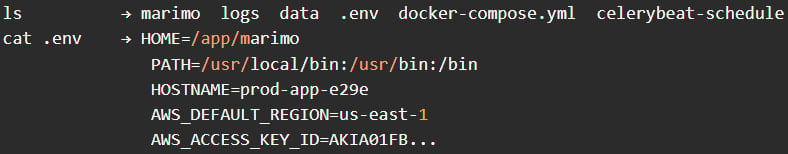
- Credential Harvesting: Shortly after validating the vulnerability, the attacker re-established a connection and initiated a manual reconnaissance phase. Basic commands such as
pwd(print working directory),whoami(display current user), andls(list directory contents) were executed to understand the compromised environment. The attacker then proceeded to navigate directories and specifically searched for SSH-related files, indicating an intention to gain further access. The primary objective quickly became credential harvesting. The attacker directly targeted.envfiles, which commonly store sensitive configuration information, including cloud credentials and application secrets. They successfully extracted environment variables and then attempted to read additional files within the working directory, continuing their search for SSH keys. The entire credential access phase was reportedly completed in under three minutes, according to the Sysdig report. - Second Exploitation Session: Approximately one hour after the initial credential theft, the same attacker returned, utilizing the same exploit sequence. This indicates a methodical approach and a clear objective.
- Reconnaissance Activity: Sysdig’s telemetry revealed that within the first 12 hours following the vulnerability disclosure, approximately 125 distinct IP addresses engaged in reconnaissance activities. This suggests a broader scanning effort by multiple threat actors attempting to identify and exploit vulnerable Marimo instances.
- April 10, 2026 (or shortly thereafter, based on reporting date): Marimo releases version 0.23.0, a patched version of their platform designed to address CVE-2026-39987. This release signifies the developers’ response to the critical vulnerability and their effort to secure their user base.
Analysis of Attacker Behavior
The behavior observed during the exploitation of CVE-2026-39987 provides significant insights into the attacker’s modus operandi. Sysdig researchers characterized the operator as a "methodical operator" who adopted a hands-on approach rather than relying solely on automated scripts. This suggests a skilled individual or small group focused on high-value targets. The deliberate focus on .env files and SSH keys points towards a strategic objective of gaining access to cloud infrastructure and potentially other sensitive systems. The absence of attempts to install persistence mechanisms, deploy cryptominers, or establish backdoors further supports the hypothesis of a quick, stealthy operation. The attacker’s goal appeared to be the rapid acquisition of valuable credentials for potential later use or sale, rather than immediate, noisy exploitation of the compromised system. This "smash and grab" approach is increasingly common in the current threat landscape, where attackers prioritize speed and stealth to avoid detection.

Supporting Data and Impact
The exploit’s speed and effectiveness are particularly alarming given the nature of Marimo’s user base. Data scientists, ML/AI practitioners, and researchers often handle sensitive intellectual property, proprietary datasets, and potentially personally identifiable information (PII). A successful compromise of a Marimo instance could lead to:
- Intellectual Property Theft: Loss of valuable algorithms, models, research findings, and proprietary code.
- Data Breaches: Exposure of sensitive customer data, financial information, or confidential research results.
- Cloud Account Compromise: If cloud credentials are exfiltrated, attackers could gain unauthorized access to cloud resources, leading to significant financial losses through resource abuse (e.g., cryptomining) or data manipulation.
- Reputational Damage: A data breach or security incident can severely damage an organization’s reputation, leading to loss of customer trust and business opportunities.
- Compliance Violations: Depending on the data handled, a breach could result in significant fines and legal repercussions for non-compliance with regulations like GDPR or CCPA.
The fact that the vulnerability allows for unauthenticated remote code execution without any prior authentication is a critical design flaw. This means that any Marimo instance exposed to the internet, even inadvertently, becomes an immediate target. The developers themselves noted that users who deployed Marimo as an editable notebook or exposed it to a shared network using the --host 0.0.0.0 flag while in edit mode were particularly at risk. These common deployment patterns, often used for development and collaboration, inadvertently expanded the attack surface significantly.
Official Responses and Recommendations
In response to the critical vulnerability and its rapid exploitation, the Marimo development team has taken swift action.
- Patch Release: Version 0.23.0 of Marimo has been released, containing the necessary fixes to address CVE-2026-39987. Users are strongly urged to upgrade to this latest version immediately. The release notes for 0.23.0 explicitly address the security vulnerability and provide guidance on the necessary upgrade.
- Mitigation Strategies: For organizations unable to upgrade immediately, Marimo has outlined alternative mitigation strategies. The most effective of these is to block or disable access to the "/terminal/ws" endpoint entirely. This can be achieved through network firewalls or Web Application Firewalls (WAFs).
- Monitoring: Marimo also recommends that users monitor their WebSocket connections, specifically looking for any unusual activity directed towards the "/terminal/ws" endpoint.
- Credential Rotation: A crucial step for any organization that may have been affected is to immediately rotate all exposed secrets and credentials, including API keys, cloud access keys, and database passwords. This limits the potential damage if credentials have already been compromised.
- Network Segmentation: Restricting external access to Marimo instances via firewalls is a fundamental security best practice that can prevent unauthorized access from the public internet.
Broader Implications for Open-Source Software Security
The incident involving Marimo serves as a potent reminder of the inherent risks associated with open-source software. While open-source projects benefit from community collaboration and transparency, which can lead to faster bug detection and resolution, they are also susceptible to rapid exploitation once vulnerabilities are disclosed. The ease with which attackers could weaponize the information from Marimo’s own security advisory is a cause for concern.
This event underscores the need for:
- Proactive Security Audits: Developers of popular open-source projects should conduct thorough security audits and penetration testing before public releases.
- Responsible Disclosure Practices: While Marimo followed responsible disclosure by releasing a patch, the speed of exploitation highlights the need for even more rapid response capabilities from development teams.
- Enhanced Security Awareness: Organizations using open-source software must maintain a robust vulnerability management program, including timely patching, continuous monitoring, and incident response planning.
- Supply Chain Security: The security of the software supply chain is paramount. Organizations need to understand the dependencies in their projects and the security posture of the open-source components they utilize.
The rapid exploitation of CVE-2026-39987 by sophisticated attackers demonstrates a concerning trend where the window of vulnerability is shrinking. The cybersecurity community must remain vigilant, and organizations must prioritize immediate patching and robust security practices to protect themselves from these evolving threats. The Marimo incident is a clear call to action for both developers and users of open-source technologies to bolster their defenses against increasingly agile and determined adversaries.







