
Cloud development platform Vercel has publicly acknowledged a significant security incident following claims by threat actors that they have successfully breached the company’s systems and are actively attempting to monetize the exfiltrated data. The revelation has sent ripples through the developer community, given Vercel’s prominent role in providing critical infrastructure for building, previewing, and deploying modern web applications, particularly those built with JavaScript frameworks. The company, renowned for its contributions to the open-source ecosystem, including the widely adopted Next.js framework, is now facing intense scrutiny as it works to understand the full scope of the breach and mitigate its impact on its user base.
The Genesis of the Breach Claims
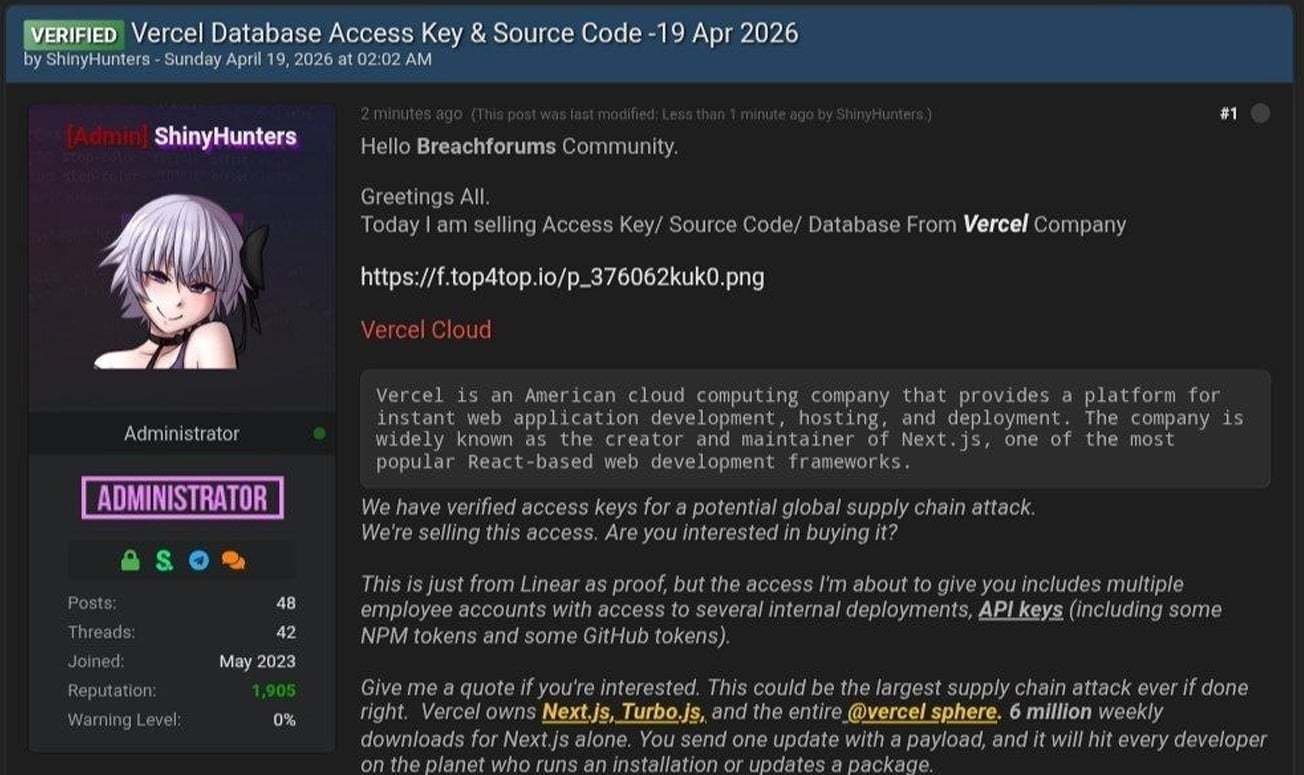
The incident came to light when a threat actor, operating under the pseudonym "ShinyHunters," posted on a clandestine hacking forum, asserting that they had gained unauthorized access to Vercel’s internal systems. The alleged perpetrator claimed to be in possession of sensitive company data, including access keys, source code repositories, database information, internal deployment details, and API credentials. In a subsequent display of purported evidence, the attacker shared a text file containing approximately 580 records of Vercel employee information, encompassing names, email addresses, account status, and activity timestamps. A screenshot allegedly depicting an internal Vercel Enterprise dashboard was also disseminated.
While the threat actor explicitly identified themselves as part of the "ShinyHunters" collective, an entity previously linked to various extortion campaigns, initial reports indicate that other actors associated with the ShinyHunters extortion gang have denied any involvement in this specific incident to BleepingComputer. This discrepancy raises questions about the attribution of the attack and the potential for splinter groups or opportunistic actors leveraging the notoriety of established hacking collectives.

Further escalating the situation, the threat actor reportedly engaged in communications via Telegram, claiming to have initiated contact with Vercel and even alleging a ransom demand of $2 million. The specifics of these alleged negotiations and Vercel’s response, if any, remain subjects of ongoing inquiry.
Vercel’s Acknowledgment and Initial Response
In a security bulletin released on the day of the public claims, Vercel confirmed that a security incident had indeed occurred, involving "unauthorized access to certain internal Vercel systems." The company stated that a "limited subset of customers" was affected. Vercel’s official communication emphasized their commitment to a thorough investigation, noting the engagement of external incident response experts to assist in understanding and remediating the breach. Furthermore, the company confirmed that law enforcement agencies have been notified and pledged to provide updates as the investigation progresses.
Crucially, Vercel asserted that its core services, including hosting and deployment infrastructure, have not been impacted by the security incident. This is a critical distinction, as it suggests that the compromise may be limited to internal systems rather than the operational infrastructure that developers rely on for their live applications. The company also stated that it is actively working with affected customers to provide guidance and support.
Recommendations for Developers and Security Posture

In response to the breach, Vercel has proactively issued recommendations to its customer base to bolster their own security. Developers are advised to meticulously review their environment variables, a common vector for credential exposure. Vercel specifically highlighted its "sensitive environment variable feature," encouraging its use to encrypt and protect critical information. The company also recommended rotating secrets, such as API keys and access tokens, as a precautionary measure to limit the potential fallout from any exposed credentials.
Background: Vercel’s Role in the Developer Ecosystem
Vercel has established itself as a leading platform for modern web development, particularly for applications built with JavaScript and its associated frameworks. Its core offerings revolve around simplifying the complexities of cloud infrastructure, enabling developers to focus on building and innovating. Key services include:
- Hosting and Deployment: Vercel provides a seamless experience for deploying web applications, integrating with Git repositories for automated builds and rollouts.
- Next.js Development: As the creators of Next.js, a popular React framework for server-side rendering and static site generation, Vercel is deeply intertwined with a significant portion of the modern web development landscape.
- Serverless Functions: The platform supports serverless computing, allowing developers to run backend code without managing servers, enhancing scalability and cost-efficiency.
- Edge Computing: Vercel leverages edge computing infrastructure, distributing application logic closer to users for reduced latency and improved performance.
- CI/CD Pipelines: The platform integrates Continuous Integration and Continuous Deployment pipelines, automating the software development lifecycle.
This deep integration into the developer workflow means that a compromise of Vercel’s internal systems, even if not directly impacting live applications, could have significant implications for the security of developer credentials, intellectual property, and potentially, the integrity of build processes.
Chronology of Events (Inferred and Reported)
While a precise timeline is still emerging and subject to the ongoing investigation, the events can be broadly reconstructed as follows:
- Pre-Breach Period: Threat actors gain unauthorized access to Vercel’s internal systems. The exact method and duration of this access are critical components of the current investigation.
- Discovery of Breach: Vercel’s internal security monitoring or external notification (potentially from the threat actor or researchers) triggers an awareness of the incident.
- Threat Actor Claims: A threat actor, identifying as "ShinyHunters," begins posting on hacking forums and potentially other channels, claiming to have breached Vercel and offering stolen data for sale.
- Vercel’s Internal Investigation: Vercel initiates its internal investigation and engages external cybersecurity experts.
- Public Disclosure: Vercel publishes a security bulletin acknowledging the incident and its impact on a subset of customers.
- Ongoing Investigation and Remediation: Vercel continues its investigation, works with law enforcement, and implements remediation measures. The company also provides guidance to its user base.
- Further Data Leak Claims: The threat actor may continue to release or offer additional data, or other actors may emerge claiming involvement or possession of related information.
Broader Implications and Potential Impact
The security incident at Vercel, a company deeply embedded in the modern web development infrastructure, carries several significant implications:
- Developer Credential Exposure: If API keys, access tokens, or employee credentials were compromised, it could expose developers and their organizations to further attacks, including unauthorized access to their code repositories, cloud resources, and other sensitive systems.
- Intellectual Property Risk: The potential exfiltration of source code raises concerns about the theft of intellectual property, which could be used for competitive advantage or sold to other malicious actors.
- Supply Chain Security: A breach at a platform like Vercel can be viewed as a supply chain attack. Compromising a trusted service provider can grant attackers a foothold into the systems of numerous downstream users. This highlights the growing importance of securing the entire software supply chain.
- Trust and Confidence: Incidents like these can erode trust in cloud platforms and development tools. Developers and businesses rely on these services to be secure and reliable, and a breach can lead to reassessments of vendor security practices.
- Ransomware and Extortion Trends: The alleged ransom demand of $2 million aligns with current trends in cybercrime, where attackers leverage data exfiltration as a primary means of extortion. The threat of public data release or the sale of compromised information often pressures victims to pay.
The fact that Vercel is investigating and has notified law enforcement are positive steps. However, the full ramifications will depend on the extent of the data accessed, the nature of the compromised credentials, and Vercel’s ability to effectively secure its systems and support its customers through the fallout. The developer community will be closely watching for further updates and the eventual findings of Vercel’s investigation. The incident serves as a stark reminder of the persistent and evolving nature of cyber threats, even for companies at the forefront of technological innovation.







