North Carolina Musician Pleads Guilty to $10 Million Spotify Royalty Fraud Scheme Fueled by AI and Bots
A North Carolina musician has admitted to orchestrating a sophisticated streaming royalty fraud scheme that netted him over $10 million from major music platforms, including Spotify, Apple Music, Amazon Music,…
Navia Benefit Solutions Data Breach Exposes Sensitive Information of Nearly 2.7 Million Individuals
Navia Benefit Solutions, Inc. (Navia), a prominent administrator of employee benefits, has disclosed a significant data breach that has potentially compromised the sensitive information of approximately 2.7 million individuals. The…
CISA Issues Urgent Warning to U.S. Organizations After Stryker Intune Breach
The Cybersecurity and Infrastructure Security Agency (CISA) has issued a critical alert to U.S. organizations, urging them to fortify their Microsoft Intune endpoint management systems following a sophisticated cyberattack that…
Aura Confirms Data Breach Exposing Nearly 900,000 Marketing Contacts Following Voice Phishing Attack
Identity protection giant Aura has officially confirmed a significant data breach that has exposed the personal information of nearly 900,000 marketing contacts. The incident, attributed to a sophisticated voice phishing…
ConnectWise Patches Critical ScreenConnect Flaw Allowing Session Hijacking and Privilege Escalation
ConnectWise, a prominent provider of business management solutions for technology solution providers, has issued an urgent security bulletin warning its ScreenConnect customers about a critical cryptographic signature verification vulnerability. This…
Apple Introduces Novel Background Security Improvements to Patch Critical WebKit Vulnerability
Apple has launched its inaugural Background Security Improvements update, a significant stride in its security patching strategy, to address a critical WebKit vulnerability identified as CVE-2026-20643. This update is notable…
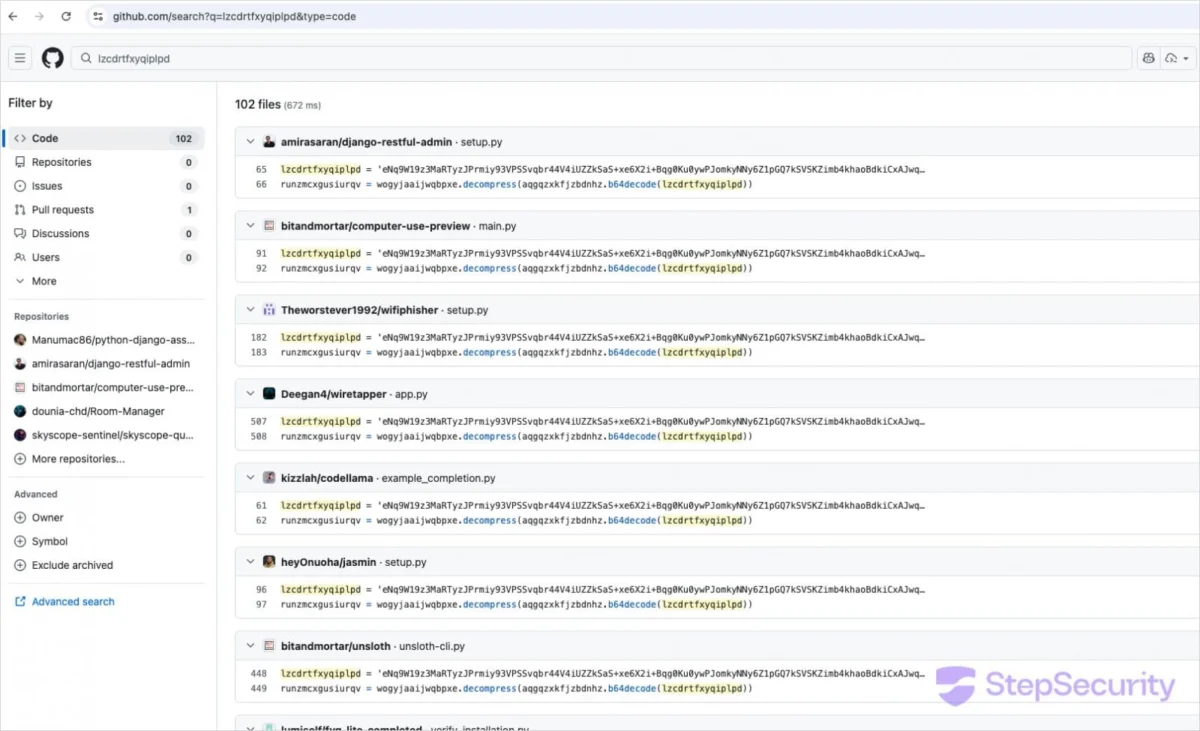
GlassWorm Malware Unleashes Widespread Supply Chain Attack, Compromising Over 400 Open-Source Components
A sophisticated and far-reaching supply chain attack, attributed to the persistent threat actor behind the "GlassWorm" campaign, has recently resurfaced, impacting a significant number of open-source projects. Researchers have identified…
The Dawn of Agentic AI Demands a Radical Rethinking of Security Through the Lens of Identity
The advent of agentic artificial intelligence heralds a transformative era for organizations, moving beyond mere assistance to autonomous action. These AI agents are not simply advanced chatbots or copilots; they…
LeakNet Ransomware Evolves with Stealthy ClickFix and Deno Runtime Tactics
The cybercriminal landscape continues to witness a concerning evolution in ransomware tactics, with the emerging LeakNet threat actor demonstrating a sophisticated and stealthy approach to infiltrate corporate networks. Recent analyses…
Stryker Cyberattack: Global Administrator Compromise Leads to Mass Device Wipes, No Malware Detected
In a significant cybersecurity incident that has disrupted operations for a leading medical technology company, Stryker, a sophisticated cyberattack has resulted in the remote wiping of tens of thousands of…